A Deceptive Tax Trap: New Phishing Campaign Delivers AsyncRAT in India The digital landscape is a constant battleground, and threat actors relentlessly refine their tactics. [...]
A new and critical vulnerability, dubbed React2Shell and tracked as CVE-2025-55182, has sent immediate ripples through the cybersecurity landscape. Within hours of its public disclosure, [...]
Freedom Mobile Data Breach: An Analysis of Compromised Customer Data The digital landscape consistently presents new challenges to data security. Recently, Canadian wireless provider Freedom [...]
The Deceptive Trap: Threat Actors Exploit Foxit PDF Reader in Recruitment Scams The digital landscape is constantly challenged by cunning cyber adversaries. A recent development [...]
Stealthy Surveillance: Unpacking the iOS Zero-Day Exploit Chain Exploited by Mercenary Spyware In a stark reminder of the persistent threats facing high-value targets, a sophisticated [...]
The digital landscape is a constant battleground, where the defense continually adapts to new threats. Google Chrome’s recent implementation of App-Bound Encryption was a significant [...]
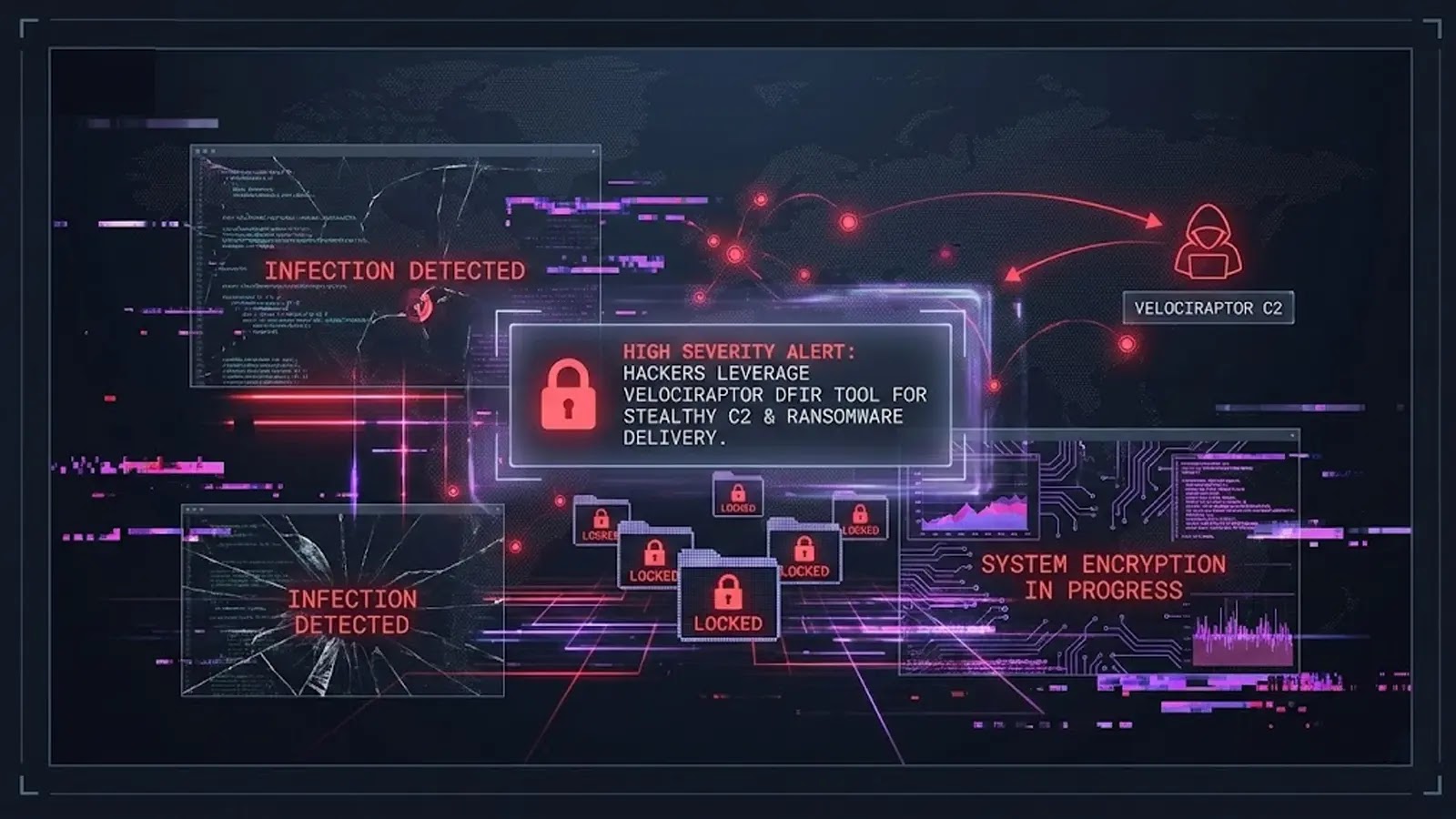
In the relentless cat-and-mouse game of cybersecurity, attackers are constantly refining their methodologies to evade detection. A disturbing trend has emerged: the weaponization of legitimate [...]
The digital landscape is under siege once again, highlighting the persistent threats lurking within widely used software. A critical remote code execution (RCE) vulnerability within [...]
The rapid evolution of web frameworks like ReactJS and Next.js has revolutionized application development, but this agility comes with inherent security considerations. A new vulnerability, [...]
In a striking example of greenwashing in the cybersecurity domain, Kohler’s new “Dekoda” smart toilet camera system, launched with assurances of “end-to-end encryption,” has been [...]