The rapid evolution of AI agents has ushered in unprecedented efficiency across various digital tasks, from managing complex email systems to orchestrating cryptocurrency trades. However, [...]
A significant cybersecurity threat has emerged, potentially impacting thousands of organizations globally. BeyondTrust, a leading provider of privileged access management solutions, has disclosed a critical [...]
Securing the AI Frontier: OpenClaw and VirusTotal Forge a Partnership for ClawHub’s Future The burgeoning landscape of Artificial Intelligence (AI) agents is transforming how businesses [...]
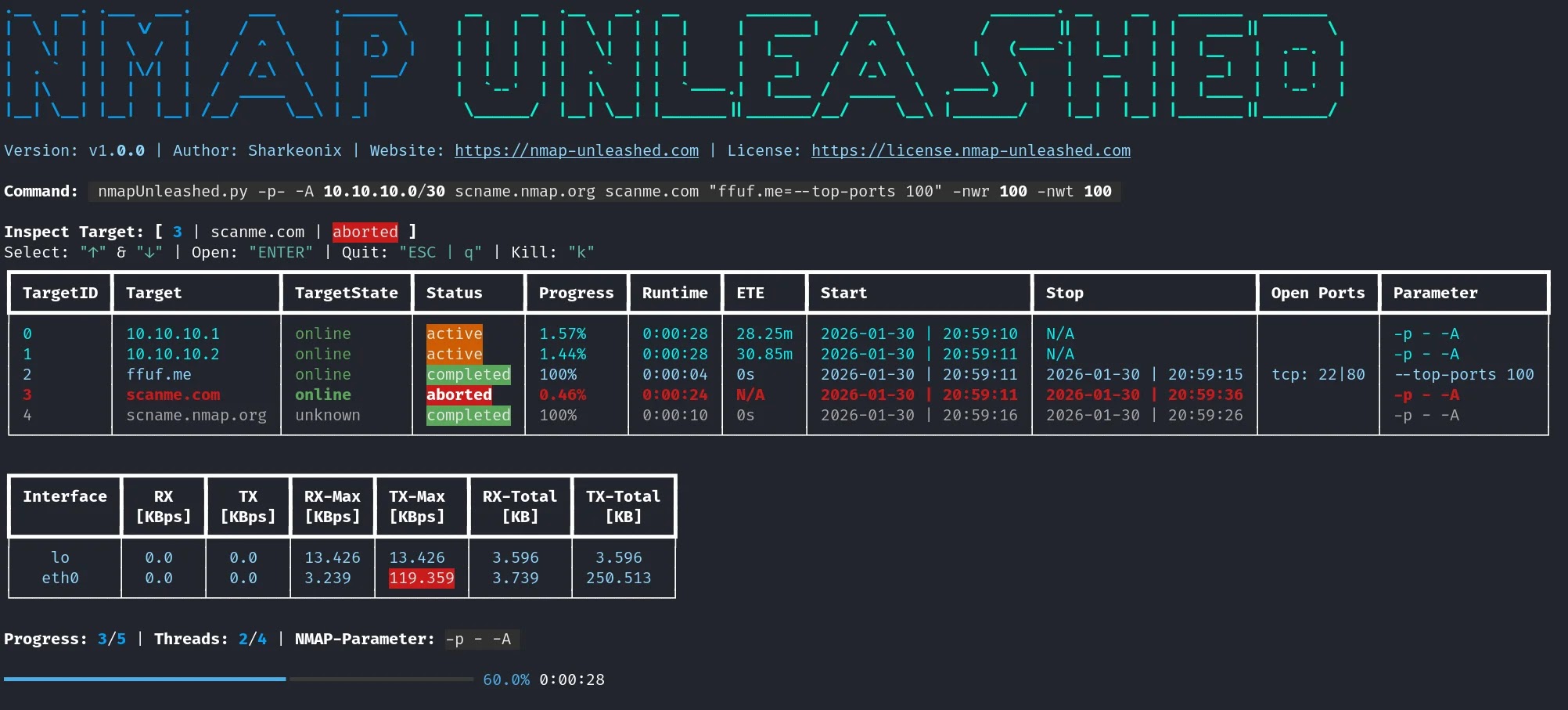
Network reconnaissance is the bedrock of effective cybersecurity. For decades, the Nmap (Network Mapper) tool has been the industry standard for uncovering network topology, identifying [...]
The Silent Threat: How Malicious Cybersquatting Becomes a Malware Gateway The digital landscape is a constant battleground, and even seemingly innocuous domain name disputes have [...]
The cybersecurity landscape has just experienced a seismic shift. Anthropic’s latest AI model, Claude Opus 4.6, has not only arrived but has immediately demonstrated jaw-dropping [...]
Bulletproof Hosting’s New Cloak: How Legitimate ISPsystem Tools Empower Cybercriminals The digital battlefield is constantly evolving, with cybercriminals perpetually seeking new methods to evade detection [...]
India’s burgeoning technology sector, a global hotbed of innovation, faces a new and insidious threat. Traditionally focused on governmental and defense targets, the Pakistan-based hacking [...]
A silent threat is stalking Android banking customers, particularly in Poland. A new, sophisticated banking trojan, dubbed “FvncBot,” has emerged, meticulously designed to bypass security [...]
The Silent Threat: CISA Mandates Removal of End-of-Life Network Edge Devices The digital perimeter of any organization is its first line of defense. Yet, for [...]