In the quiet corners of the internet, a persistent and financially motivated threat actor has been operating under the radar for over two years, leveraging [...]
Unpacking GPUBreach: A New Era of GPU-Powered System Compromise The landscape of system security just got significantly more complex with the emergence of GPUBreach, a [...]
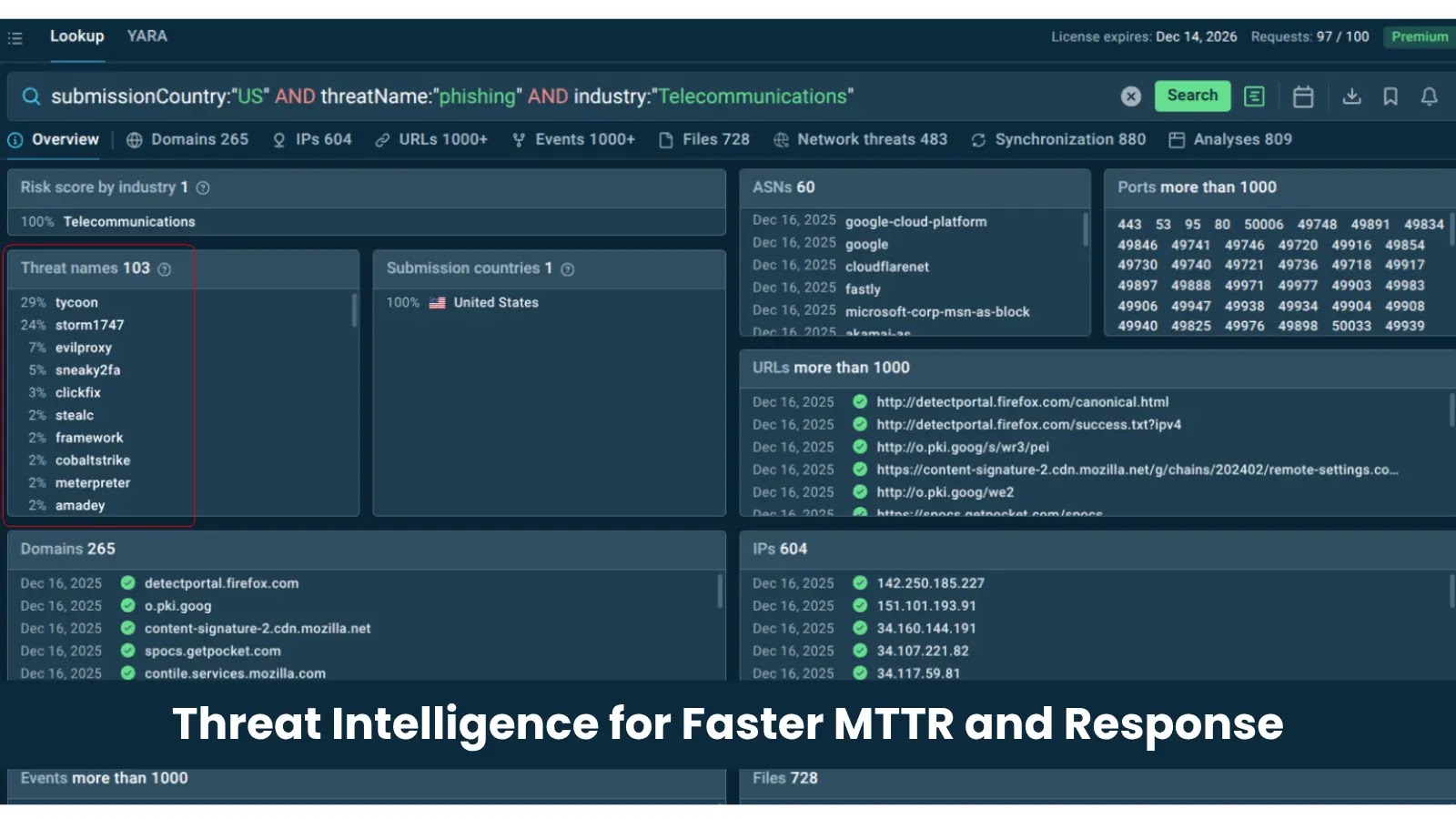
From Alert Overload to Rapid Response: Why Threat Intelligence Is a Top Solution for Fast MTTR Modern Security Operations Centers (SOCs) face a relentless deluge [...]
The digital landscape is a constant battleground, with new threats emerging daily. For Android users and organizations relying on the platform, staying ahead of vulnerabilities [...]
The Deceptive Lure: Threat Actors Weaponize LogMeIn Resolve and ScreenConnect in Multi-Stage Phishing Attacks In a chilling demonstration of evolving cyber tactics, threat actors are [...]
BlueHammer: Exploiting Windows Defender for Privilege Escalation The digital defense landscape faces constant challenges, and the recent public release of “BlueHammer” highlights a critical vulnerability [...]
A disturbing trend has emerged from the Middle East, underscoring the persistent threat of identity-based attacks. Recent intelligence indicates that an Iran-linked threat actor [...]
Microsoft Warns Against Storm-1175: Medusa Ransomware’s Zero-Day Assault on Web-Facing Assets Organizations worldwide are facing a renewed and aggressive threat as Microsoft issues a [...]
Proactive Protection: Microsoft Defender’s Latest Update Secures Windows Installation Images In a landscape where new threats emerge daily, ensuring foundational security is paramount. Microsoft [...]
Imagine finding a golden ticket online – free premium access to a tool you use daily, like TradingView. For many traders and financial analysts, TradingView [...]