The relentless pace of cyber threats demands innovative solutions. Traditional penetration testing, while crucial, often struggles to keep up with the speed of modern web [...]
In the constant battle against cyber threats, a new and insidious adversary has emerged, specifically targeting Windows users with a penchant for cryptocurrency and valuable [...]
The Alarming Rise of AiTM: A New MFA Bypass Threat to Microsoft 365 and Okta Users Organizations worldwide face an escalated threat from a sophisticated [...]
Unearthing Secrets: How Researchers Revived a 20-Year-Old “Blinkenlights” Attack to Dump Smartwatch Firmware In a fascinating demonstration of cybersecurity ingenuity, researchers at Quarkslab have successfully [...]
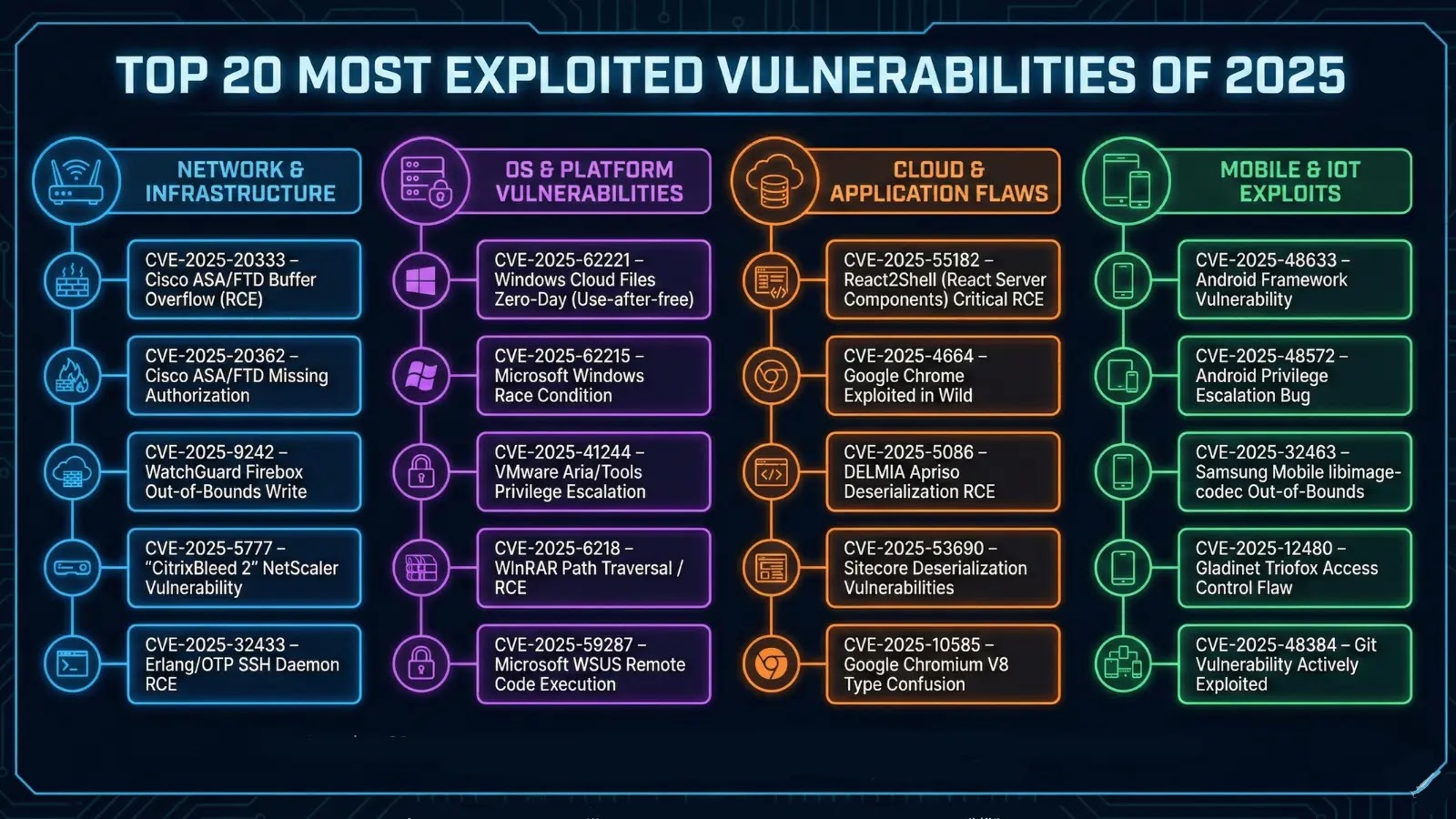
The year 2025 has cemented its place in cybersecurity history as a period of relentless and sophisticated vulnerability exploitation. Organizations across every sector, from nascent [...]
In the relentlessly evolving landscape of cyber threats, understanding the tactics and tools of adversarial groups is paramount for effective defense. Today, we delve into [...]
In the relentless landscape of cyber threats, a sophisticated new phishing technique has emerged, targeting Microsoft accounts with alarming efficacy. Dubbed “ConsentFix,” this attack bypasses [...]
NANOREMOTE Malware Leverages Google Drive API for Command-and-Control (C2) to Attack Windows Systems
NANOREMOTE Malware: Google Drive API Becomes Its Malicious Command Center A new and potent threat to Windows systems has emerged, cunningly camouflaged within the very [...]
Beyond the Click: Unpacking the Dark Aftermath of Stolen Phishing Data The deceptive simplicity of a phishing email often belies the profound and far-reaching consequences [...]
The landscape of cybersecurity is in constant flux, demanding tools and platforms that evolve at an equally rapid pace. For penetration testers, ethical hackers, and [...]