Navigating the Quantum Horizon: Introducing Crypto Scanner The specter of quantum computing advances looms large over contemporary cryptography. As the timeline for powerful quantum [...]
The digital landscape demands vigilance, especially within collaborative platforms. Microsoft Teams, a cornerstone for many organizations, is now empowering its users with a critical [...]
The dark underbelly of the cybercrime ecosystem just experienced a significant tremor. Reports indicate that the database of WormGPT, a notorious AI platform tailor-made [...]
In the relentless cat-and-mouse game of cybersecurity, threat actors continuously refine their tactics to bypass defenses. One such persistent adversary, GuLoader (also known as [...]
The promise of artificial intelligence often comes hand-in-hand with the implicit trust users place in these powerful tools. Yet, recent revelations serve as a stark [...]
In the relentless landscape of cyber threats, a formidable adversary known as Bloody Wolf, or Stan Ghouls, has surged to the forefront, orchestrating a series [...]
Criminal IP Integrates with IBM QRadar to Deliver Real-Time Threat Intelligence Across SIEM and SOAR
In the high-stakes realm of cybersecurity, the speed and accuracy of threat detection and response are paramount. Security operations teams constantly battle to stay ahead [...]
Singapore’s Telecoms Under Siege: UNC3886 Targets Edge Devices in Sophisticated Cyber Espionage The digital arteries of a nation, its telecommunications infrastructure, are under constant [...]
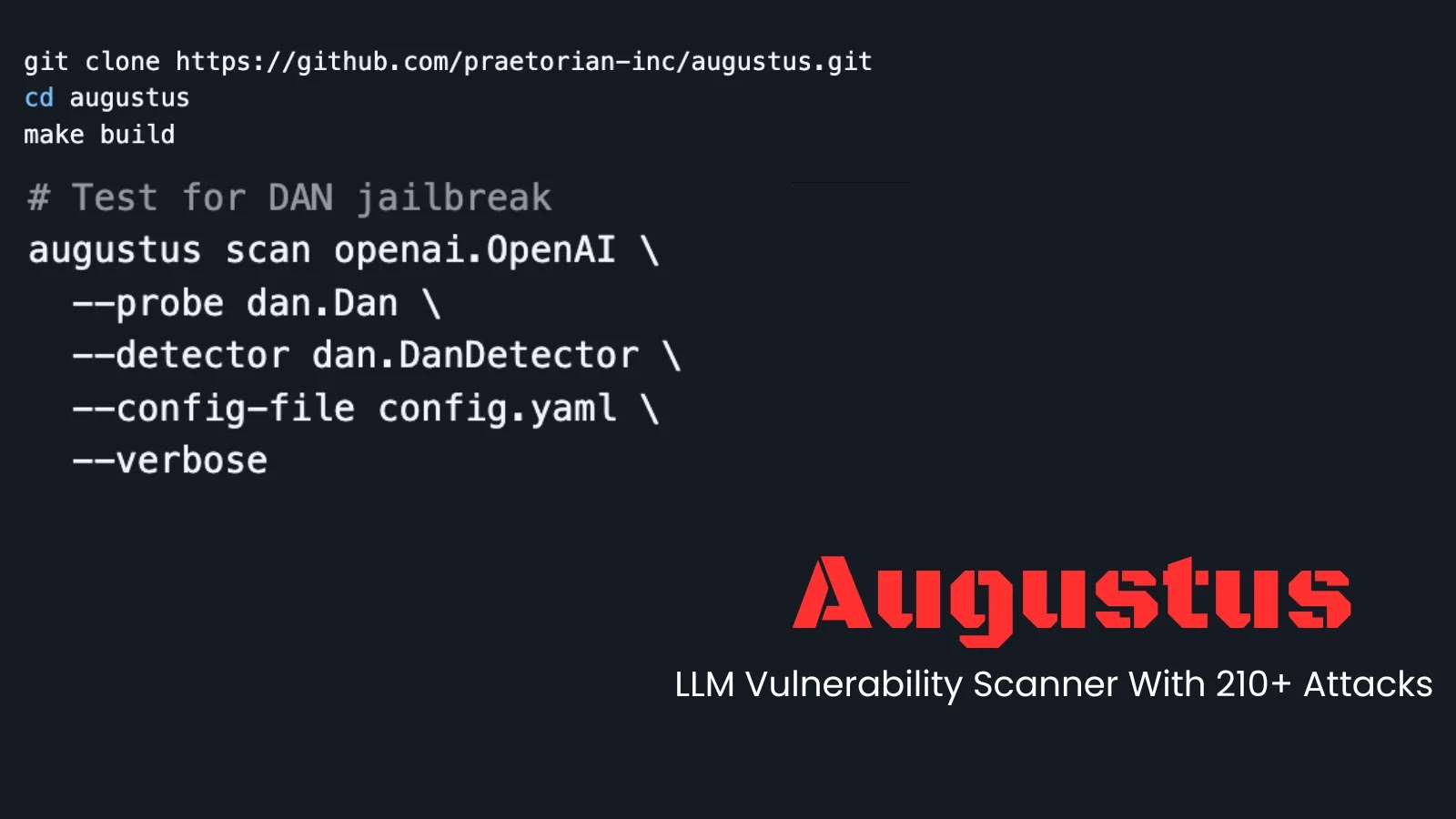
The rapid adoption of Large Language Models (LLMs) has introduced a new frontier for cybersecurity, presenting novel attack surfaces and complex vulnerabilities. Securing these [...]
The digital frontier of remote employment, a landscape once offering unparalleled flexibility, now confronts an escalating and insidious threat. North Korean operatives, long recognized for [...]