A critical flaw in Google Chrome’s WebView component has necessitated an urgent security update, highlighting the persistent challenges in maintaining robust application security. This vulnerability, [...]
A silent, yet widespread digital threat is actively compromising systems across Central and Eastern Europe and beyond. The cybersecurity landscape has been rattled by [...]
The Holiday Phishing Onslaught: DocuSign Spoofing and Identity Theft Questionnaires The festive season, a time typically associated with cheer and goodwill, has unfortunately brought with [...]
Microsoft’s ambitious integration of artificial intelligence (AI) features into Windows 11 has certainly stirred the pot. While these new functionalities, like Copilot and Recall, promise [...]
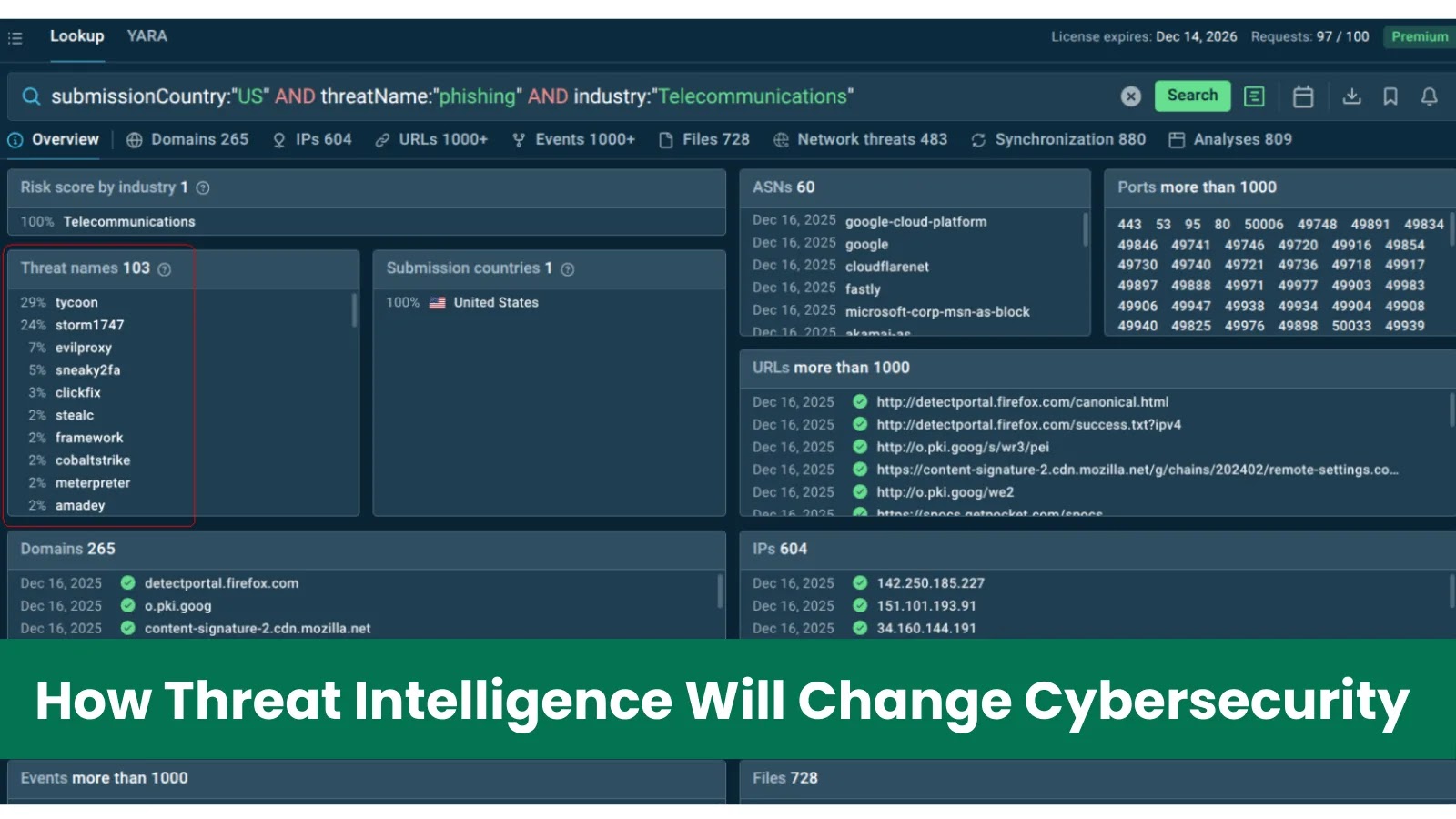
The Shifting Sands of Cyber Defense: How Threat Intelligence Will Redefine Cybersecurity by 2026 The cybersecurity landscape is in constant flux, a relentless battle [...]
NordVPN: Clearing the Air on Dark Web Data Breach Claims The digital shadows of the dark web frequently harbor unsubstantiated claims that can send [...]
Critical Dolby Codec Vulnerability Threatens Android Devices A significant security flaw has recently emerged, putting millions of Android devices at risk. Google’s January 2026 [...]
The Unprecedented Demand: 20 Million Anonymized ChatGPT Logs Ordered in Copyright Showdown The landscape of artificial intelligence is rapidly evolving, bringing with it a complex [...]
A chilling revelation has sent ripples through the developer community, particularly those relying on the robust capabilities of AdonisJS. A critical path traversal vulnerability has [...]
The digital landscape is a constant battleground, and even the most robust organizations can fall victim to sophisticated cyber threats. Recently, Sedgwick, a prominent claims [...]