Navigating the AI Frontier: Microsoft’s Enhanced Security for Generative Models in Azure AI Foundry The explosive growth of generative artificial intelligence presents unprecedented opportunities, [...]
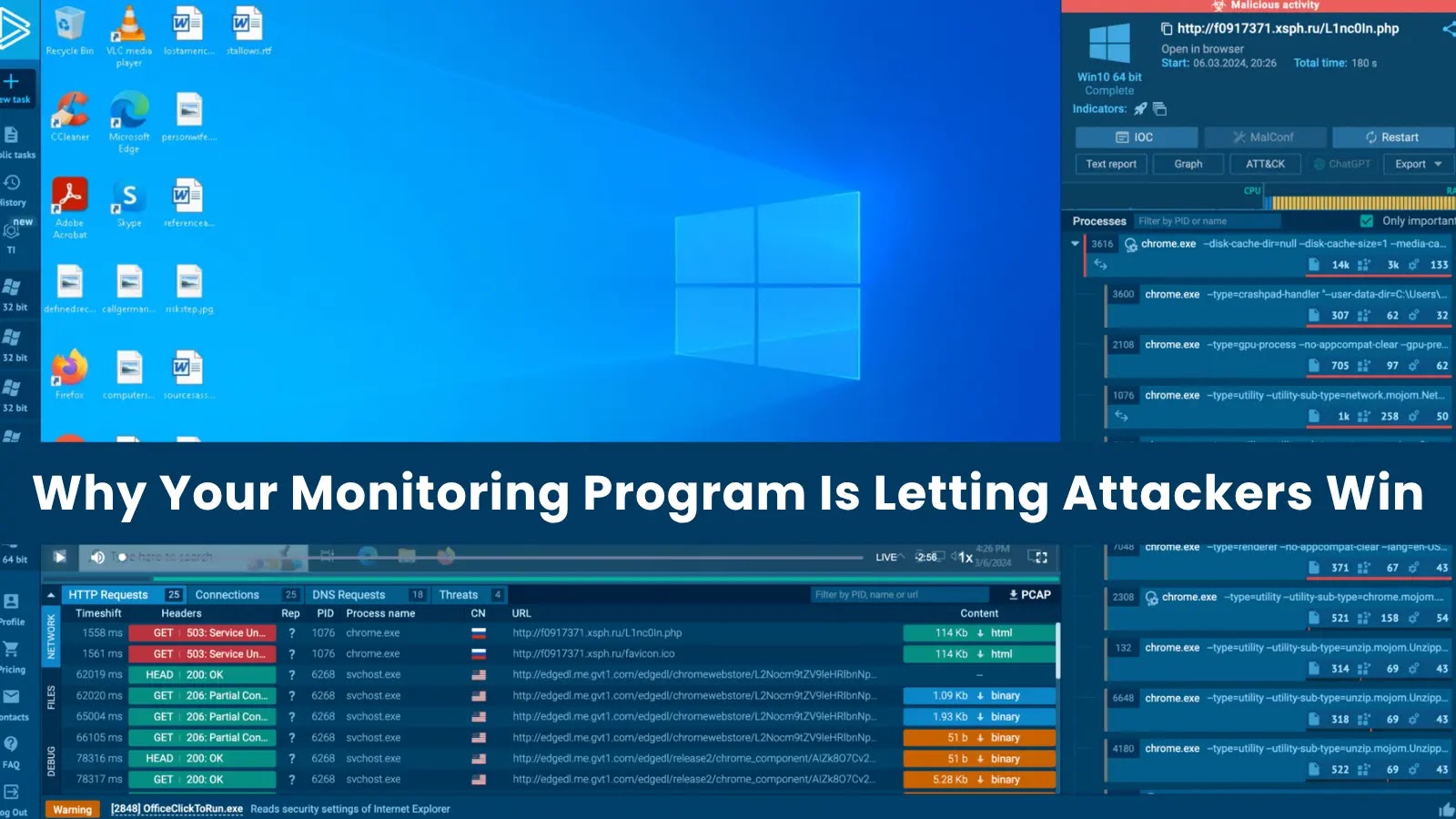
In the high-stakes world of cybersecurity, a sophisticated monitoring program is often considered the bedrock of defense. Organizations invest heavily in advanced logging infrastructures, myriad [...]
The digital underworld, a labyrinth of illicit markets and clandestine communications, has long posed a formidable challenge to cybersecurity professionals. Its sheer scale and the [...]
Distributed Denial of Service (DDoS) attacks are a persistent and growing threat, capable of crippling online services, disrupting businesses, and causing significant financial and reputational [...]
The dark web just became a more dangerous place for organizations. On March 22, 2026, a new Tor-based leak site, “ALP-001,” emerged, openly advertising itself [...]
Urgent Chrome Security Update: Patch Now to Thwart Remote Code Execution Google has once again stepped in to fortify its widely used Chrome browser, [...]
In the complex landscape of modern enterprise, the lines between technological advancements, strategic business objectives, and regulatory compliance are increasingly blurring. For cybersecurity, this convergence [...]
Urgent Security Alert: Roundcube Webmail Patches Critical Vulnerabilities The digital landscape demands constant vigilance, especially for widely-used open-source platforms. Recently, the popular web-based IMAP [...]
The lines between innovation and exploitation blur as cybercriminals increasingly leverage cutting-edge technologies and social engineering tactics against unsuspecting users. A recent campaign highlights this [...]
In an alarming discovery, over half a million End-of-Life (EOL) Microsoft Internet Information Services (IIS) instances remain exposed to the public internet, creating a [...]