A New Threat: APT36’s Python-Based ELF Malware Targets Indian Government The digital battlefield is constantly evolving, and nation-state threat actors are at the forefront of [...]
A silent and sophisticated threat has emerged in the cybersecurity landscape, raising significant concerns among security experts. A clandestine Out-of-Band Application Security Testing (OAST) [...]
Unmasking Tomiris: A Global Resurgence with Advanced Tactics The cybersecurity landscape just became significantly more challenging as the notorious Tomiris hacker group has re-emerged [...]
Unpacking the Azure API Management Flaw: Cross-Tenant Account Creation Risks In the complex landscape of cloud security, even “by design” functionalities can harbor critical [...]
A silent threat lurked within the development workflows of many, a vulnerability in OpenAI’s Codex CLI that could have turned routine tasks into an [...]
The Silent Infiltration: How LOLBins Bypass Your EDR Defenses Organizations invest heavily in advanced security solutions, yet a stealthier and more insidious threat is [...]
The digital landscape is a constant battleground, and even the most trusted applications can harbor hidden dangers. A recent revelation has sent shockwaves through the [...]
Outlook’s Latest Snag: Excel Attachments and Non-ASCII Characters In the intricate ecosystem of daily business operations, email and spreadsheets form critical arteries of information [...]
A disturbing revelation has shaken the e-commerce landscape: South Korean online retail giant Coupang recently confirmed a substantial data breach, compromising the personal records [...]
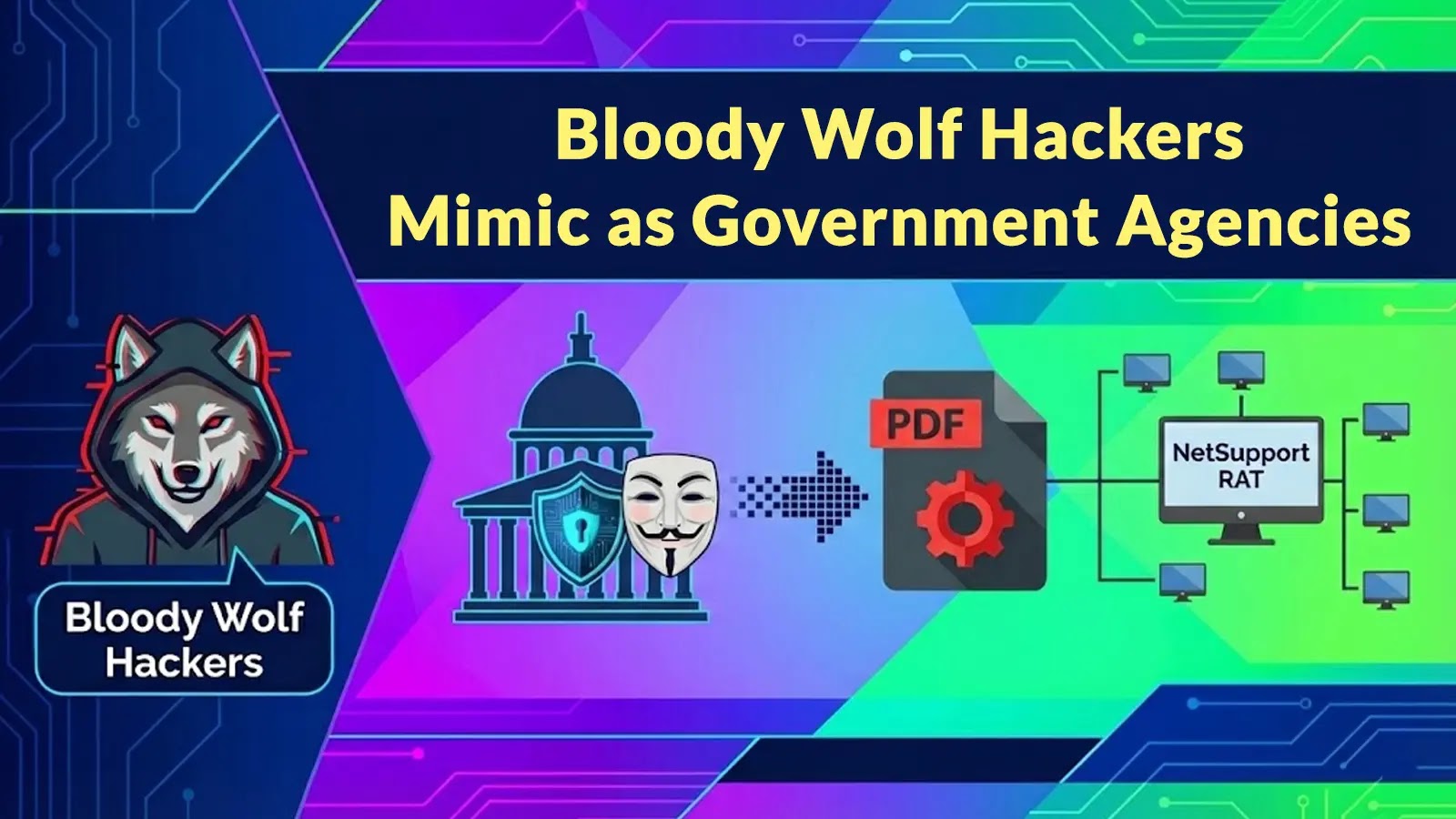
Bloody Wolf Hunts Central Asia: Unmasking Sophisticated Government Impersonation and NetSupport RAT Deployment The digital landscape of Central Asia is under siege. A highly sophisticated [...]