Unmasking SharkStealer: The EtherHiding Pattern and Web3’s Dark Side The cybersecurity landscape is constantly shifting, with threat actors relentlessly innovating their tactics to bypass defenses. [...]
Bitter APT Targets Government Agencies with WinRAR Zero-Day Exploits In a compelling display of sophisticated cyberespionage, the notorious Bitter APT group, also identified as APT-Q-37 [...]
Unmasking the Threat: How Microsoft 365 Exchange Direct Send Becomes a Hacker’s Gateway In the intricate landscape of modern cybersecurity, even seemingly innocuous features can [...]
A critical security disclosure from Atlassian has sent ripples through the IT security community, revealing a high-severity path traversal vulnerability impacting Jira Software Data Center [...]
CISA Warns of Motex LANSCOPE Endpoint Manager Vulnerability Under Active Exploitation Cybersecurity agencies rarely issue warnings without significant cause. The recent alert from CISA [...]
Urgent Warning: Adobe Magento RCE Vulnerability Under Active Exploitation – Is Your Store at Risk? The digital storefronts powering countless businesses are facing a [...]
In a significant move against burgeoning cybercrime, SpaceX has taken decisive action, disabling over 2,500 Starlink satellite internet terminals found operating in notorious scam [...]
The digital world we navigate demands constant vigilance, especially when the devices we rely on daily become targets for sophisticated attacks. Recent developments at [...]
In the rapidly evolving landscape of AI-powered tools, the line between helpful assistance and potential exploitation can become alarmingly thin. A recent disclosure has [...]
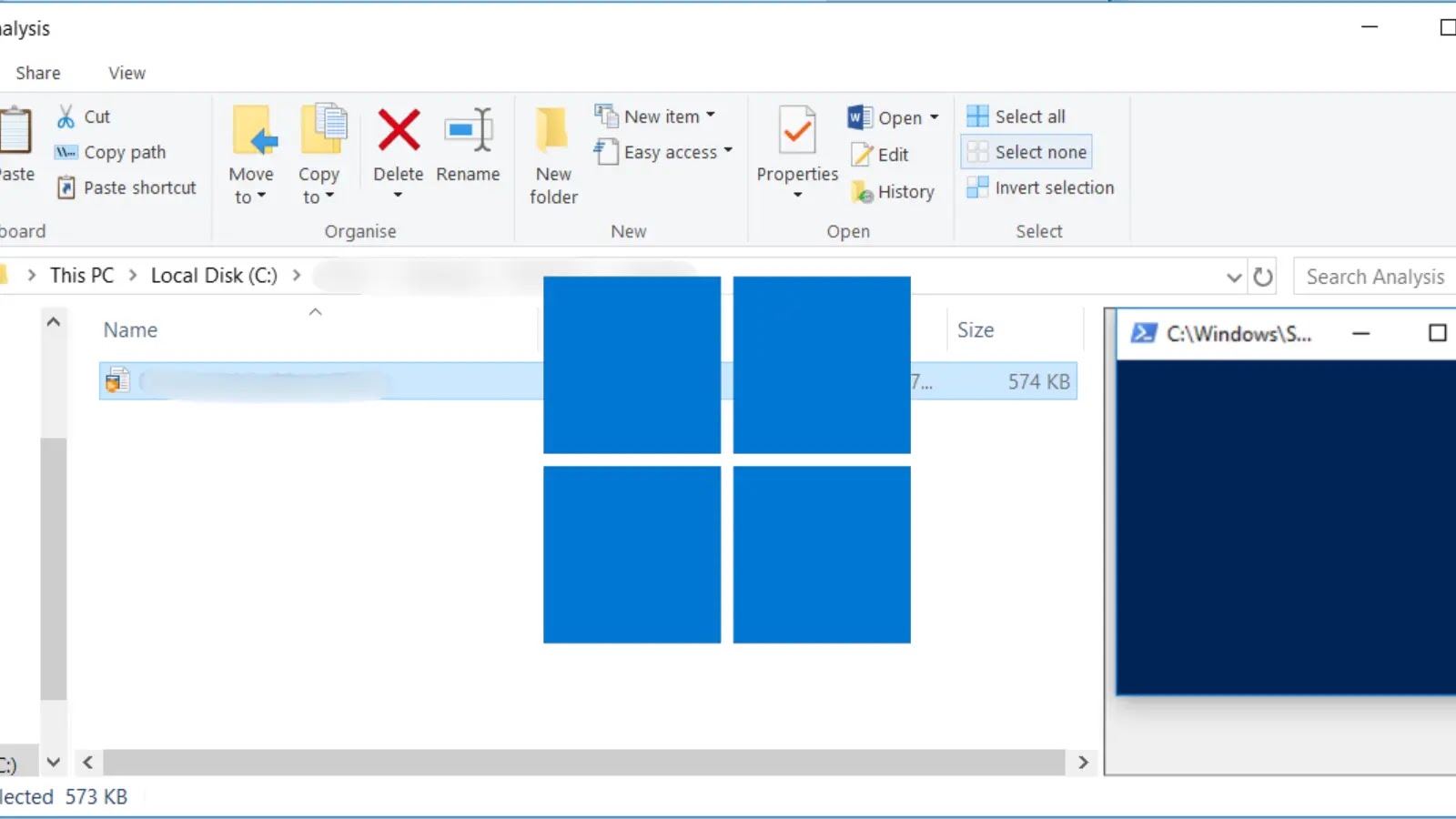
In the relentless pursuit of robust digital defenses, Microsoft has once again demonstrated its commitment to user security. A critical update, rolling out starting with [...]