CISA’s Urgent Warning: Windows Vulnerability Actively Exploited in Attacks The cybersecurity landscape is in constant flux, and organizations must remain vigilant against emerging threats. A [...]
The digital landscape is a constant battleground, and even seemingly archaic attack vectors can resurface with renewed effectiveness. In early October 2025, cybersecurity experts [...]
A disturbing development in the cybersecurity landscape has caught the attention of Capitol Hill. U.S. Senator Bill Cassidy, Chairman of the Senate Health, Education, Labor, [...]
The digital landscape is under siege, and a new, formidable adversary has emerged from the shadows: Qilin ransomware. Operating with alarming sophistication and leveraging a [...]
The digital landscape is a perpetual battleground, and even the most vigilant users can fall victim to sophisticated attacks. One of the most insidious threats [...]
Unmasking the Mysterious Elephant: A New APT Threat to Asia-Pacific Institutions In the complex and often shadowy world of cyber warfare, new adversaries constantly [...]
Operation Silk Lure: Unraveling the Threat of ValleyRAT via Windows Scheduled Tasks The digital landscape is under constant siege, and threat actors continually refine [...]
The digital landscape is a constant battleground, where sophisticated adversaries relentlessly innovate their attack vectors. Recently, North Korean state-sponsored threat actors have demonstrated this prowess [...]
Cisco IOS and IOS XE Vulnerabilities: A Critical Threat to Network Control Network infrastructure forms the backbone of modern business operations, and the devices [...]
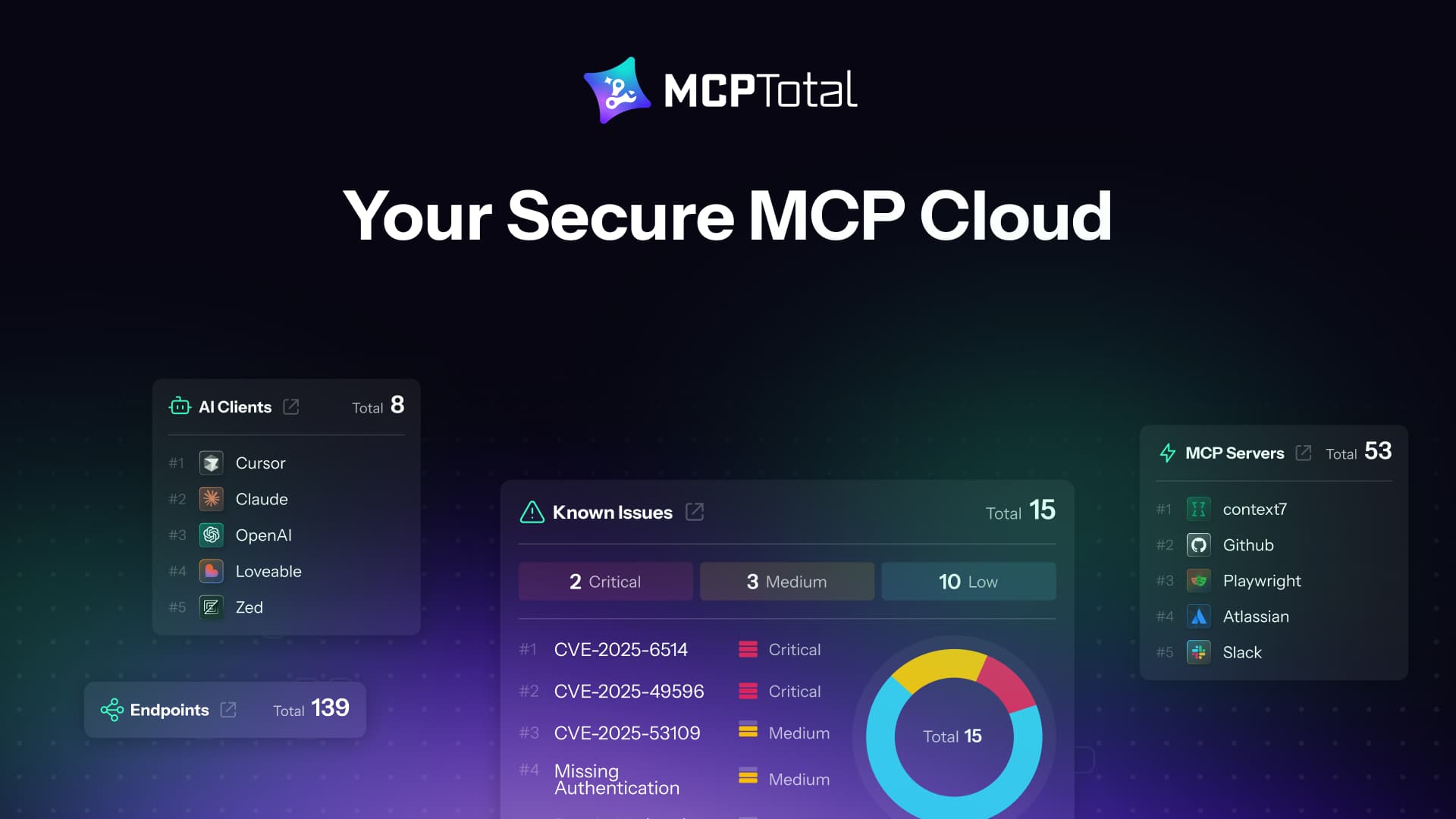
The Critical Need for Secure Model Context Protocol (MCP) Workflows The rapid integration of Artificial Intelligence (AI) models into enterprise systems has revolutionized how businesses [...]