Navigating the Evolving Landscape of Penetration Testing: The Rise of PTaaS In a cybersecurity climate where threats constantly evolve and compliance mandates tighten, organizations face [...]
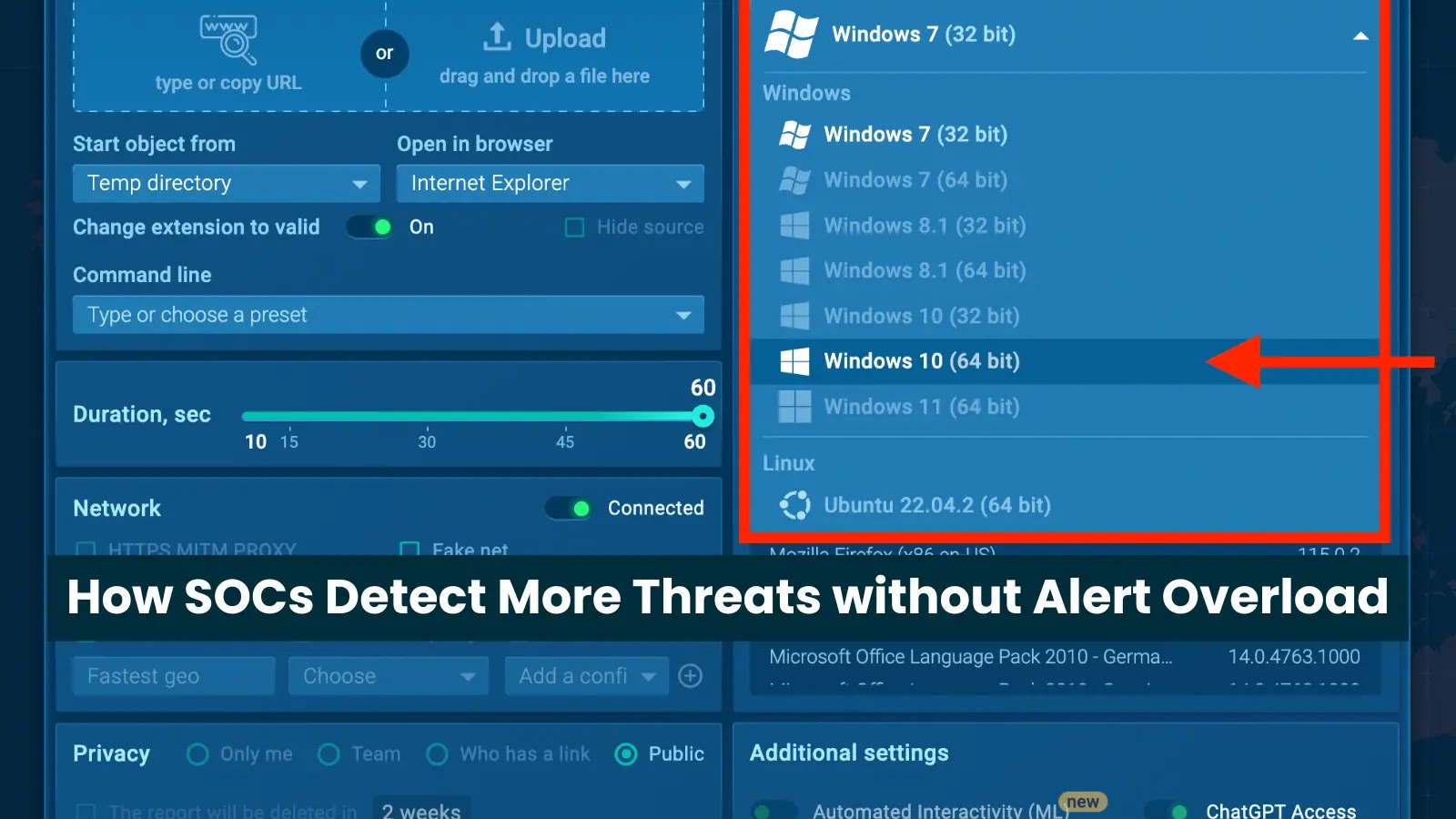
For many Security Operations Centers (SOCs), the daily reality can feel like an endless deluge of alerts. This constant barrage often leads to alert fatigue, [...]
Unmasking Critical SAP NetWeaver Vulnerabilities: A Deep Dive into Authorization Bypass and OS Command Execution The digital landscape for enterprises often hinges on robust, reliable [...]
Urgent Alert: October 2025 Microsoft Update Disrupts Active Directory Syncs on Windows Server 2025 The backbone of countless enterprise networks, Active Directory (AD), is currently [...]
The digital landscape is a constant battleground, and sophisticated adversaries are always seeking new ingress points. A recent campaign by the Chinese APT group known [...]
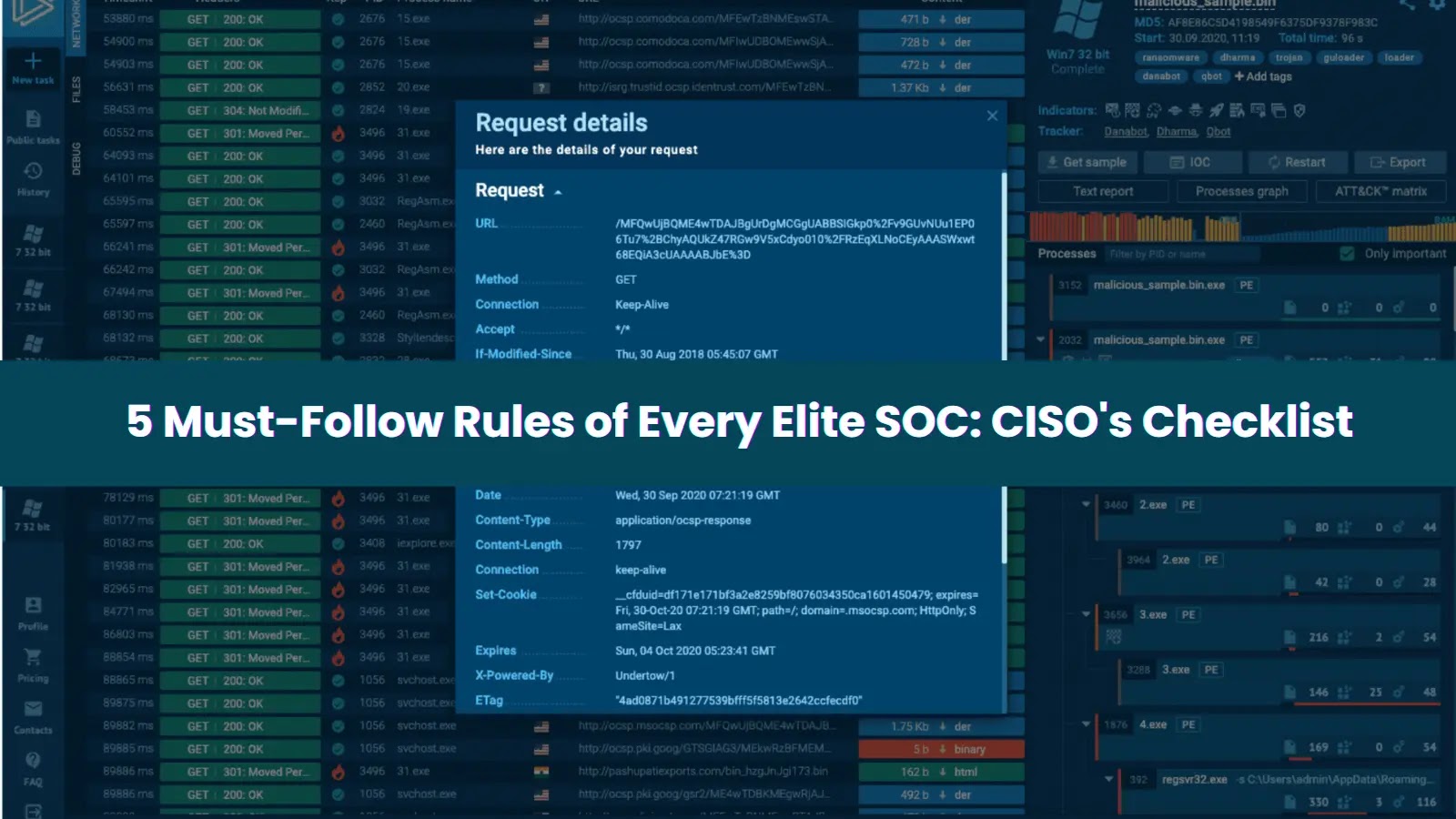
The silence in a Security Operations Center (SOC) after a critical alert hits can be deafening. In that tense moment, security analysts hold their breath, [...]
The digital landscape is under siege from an increasingly sophisticated array of cyber threats. A stark reminder of this reality emerged in mid-2025: a novel [...]
The digital landscape was shaken recently by the news of a significant breach affecting F5, a formidable name in application security and delivery. On October [...]
Cisco SNMP 0-Day: Operation Zero Disco Exploits Critical Vulnerability for Linux Rootkits The cybersecurity landscape has been rocked by the disclosure of “Operation Zero Disco,” [...]
Unmasking GhostBat: How Fake RTO Apps Are Stealing Banking Data in India In an increasingly connected world, the very tools designed for convenience can become [...]