A new, highly sophisticated self-propagating worm has emerged, leveraging the WhatsApp messaging platform to unleash banking malware. This aggressive campaign specifically targets users of [...]
The software supply chain, a critical but often overlooked attack vector, has once again been weaponized by sophisticated adversaries. North Korean state-sponsored threat actors have [...]
A Disturbing New Attack: Microsoft Edge’s IE Mode Exploited by Threat Actors The cybersecurity landscape has documented a concerning escalation: threat actors have discovered [...]
A critical vulnerability in Axis Communications’ Autodesk Revit plugin has exposed Azure Storage Account credentials, creating significant security risks for customers and potentially enabling [...]
The Disarming Simplicity: Prompt Injection Bypasses OpenAI Guardrails The promise of enhanced AI safety through sophisticated guardrail frameworks is a critical defense line in [...]
Astaroth Banking Malware’s Latest Evolution: Leveraging GitHub for Evasive Configuration Hosting The landscape of cyber threats is perpetually shifting, and banking malware remains a persistent [...]
RMPocalypse: Unmasking a Critical Threat to AMD SEV-SNP Confidential Computing In the evolving landscape of cloud security, confidential computing stands as a pillar, promising unprecedented [...]
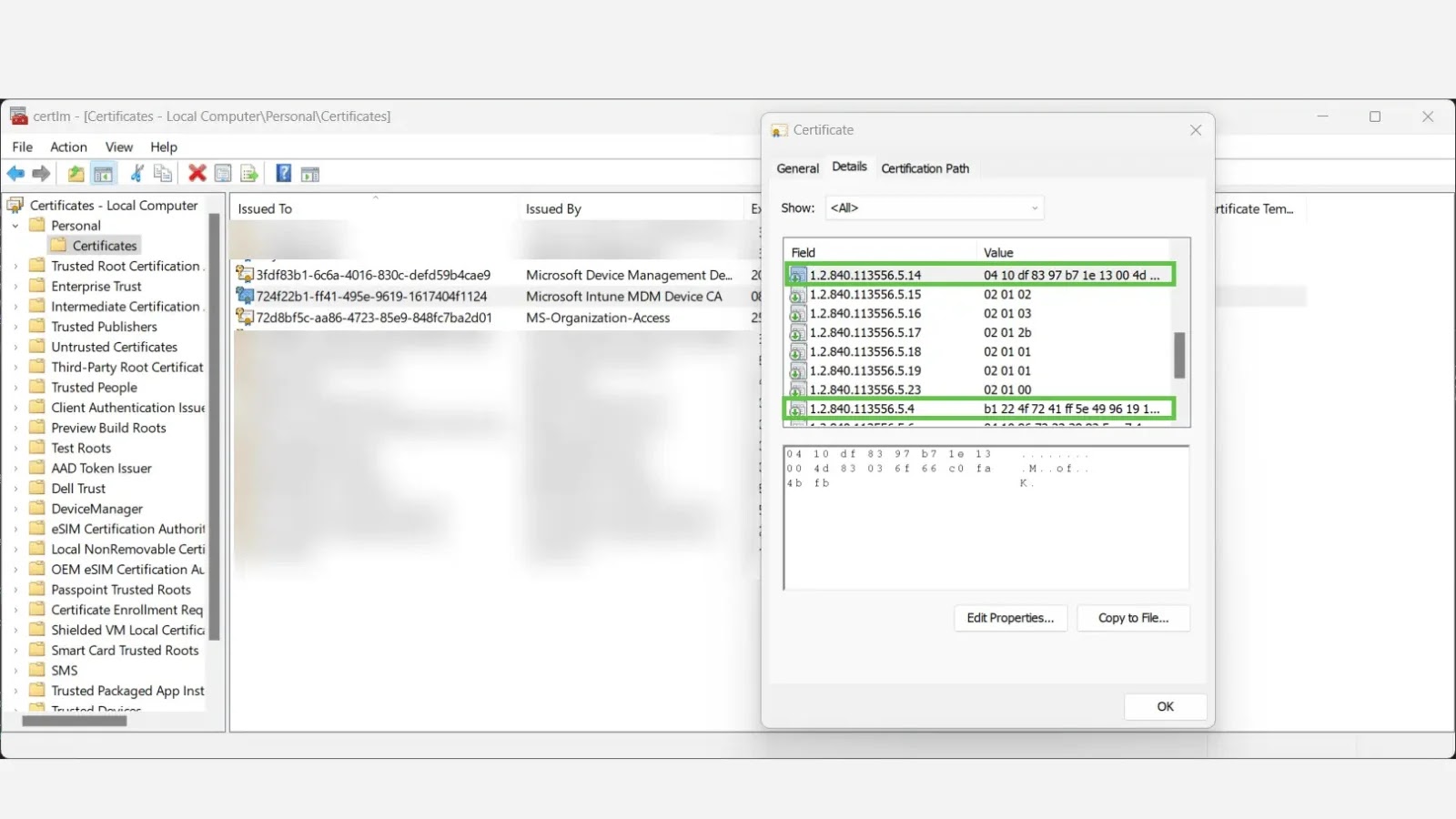
Unveiling Device Identity: How Intune MDM Certificates and Entra ID Strengthen Trust In the complex landscape of modern IT, accurately verifying device identity is paramount [...]
Unmasking the Discord Webhook C2 Threat: A New Era of Supply Chain Attacks In the evolving landscape of cyber threats, attackers constantly seek novel [...]
The relentless cat-and-mouse game between cybersecurity professionals and malicious actors continues to evolve. While Endpoint Detection and Response (EDR) solutions are cornerstones of modern defense [...]