Unmasking the Invisible Threat: ASCII Smuggling and its Impact on LLMs like Gemini The landscape of cyber threats is perpetually shifting, with attackers continually finding [...]
Windows 11 25H2 General Availability: What You Need to Know The digital landscape consistently drives forward, and with it, operating systems evolve to meet [...]
A critical zero-day vulnerability is actively compromising thousands of Cisco firewalls globally. Threat actors are aggressively exploiting this flaw in the wild, posing an [...]
A New Breed of Android Banking Trojan: Hidden VNC for Total Control The landscape of mobile threats is constantly evolving, with attackers devising increasingly [...]
A significant alert has been issued by the OpenSSL Project, revealing critical vulnerabilities that pose a serious threat to the security of digital communications. These [...]
The rapid ascent of Artificial Intelligence has irrevocably reshaped how we interact with technology. From generating sophisticated text to synthesizing complex data, AI tools [...]
The digital landscape is a constant battleground, and even the most robust defenses can harbor critical vulnerabilities. In a recent alert that sent ripples [...]
The Silent Takeover: Threat Actors Hijack MS-SQL Servers with XiebroC2 The digital landscape is a constant battleground, and a new and concerning campaign highlights [...]
In the high-stakes realm of international cybersecurity, a new alarm has been sounded. The Iranian-aligned threat group APT35, also known by monikers such as [...]
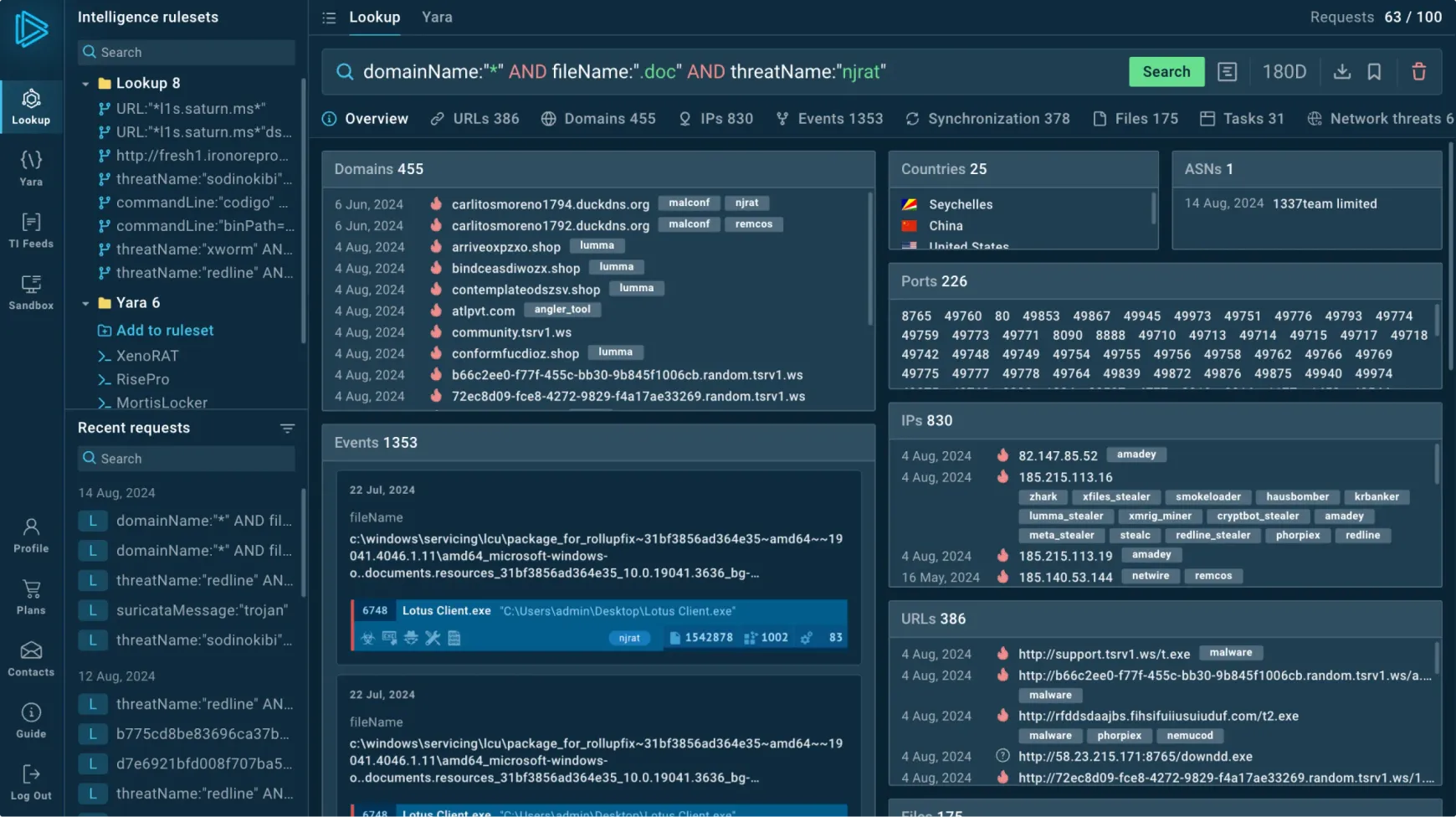
Accelerating Cyber Threat Detection: The Power of Threat Intelligence Feeds for SOC Teams Security Operations Centers (SOCs) are the front lines of defense for organizations, [...]