The cybersecurity landscape is a constant battleground, with new threats emerging daily. Yet, some vulnerabilities resurface, reminding us of persistent risks. Recently, the Cybersecurity [...]
A recent security advisory from Elastic has brought to light a significant vulnerability within the Kibana CrowdStrike Connector. This medium-severity flaw, identified as CVE-2025-37728, [...]
A critical new command injection vulnerability in OpenSSH has been disclosed, enabling remote code execution and posing a significant threat to countless systems worldwide. This [...]
Cl0p Strikes Oracle: Urgent 0-Day Vulnerability in E-Business Suite Demands Immediate Action The cybersecurity landscape has once again been rattled, this time by the [...]
In a deeply troubling development, cybersecurity researchers have unearthed a sophisticated Android malware campaign specifically targeting elderly individuals. This operation leverages fraudulent travel and [...]
The digital landscape is a constant battleground, and even the most robust platforms can present vulnerabilities. Recently, Splunk, a leading platform for security information [...]
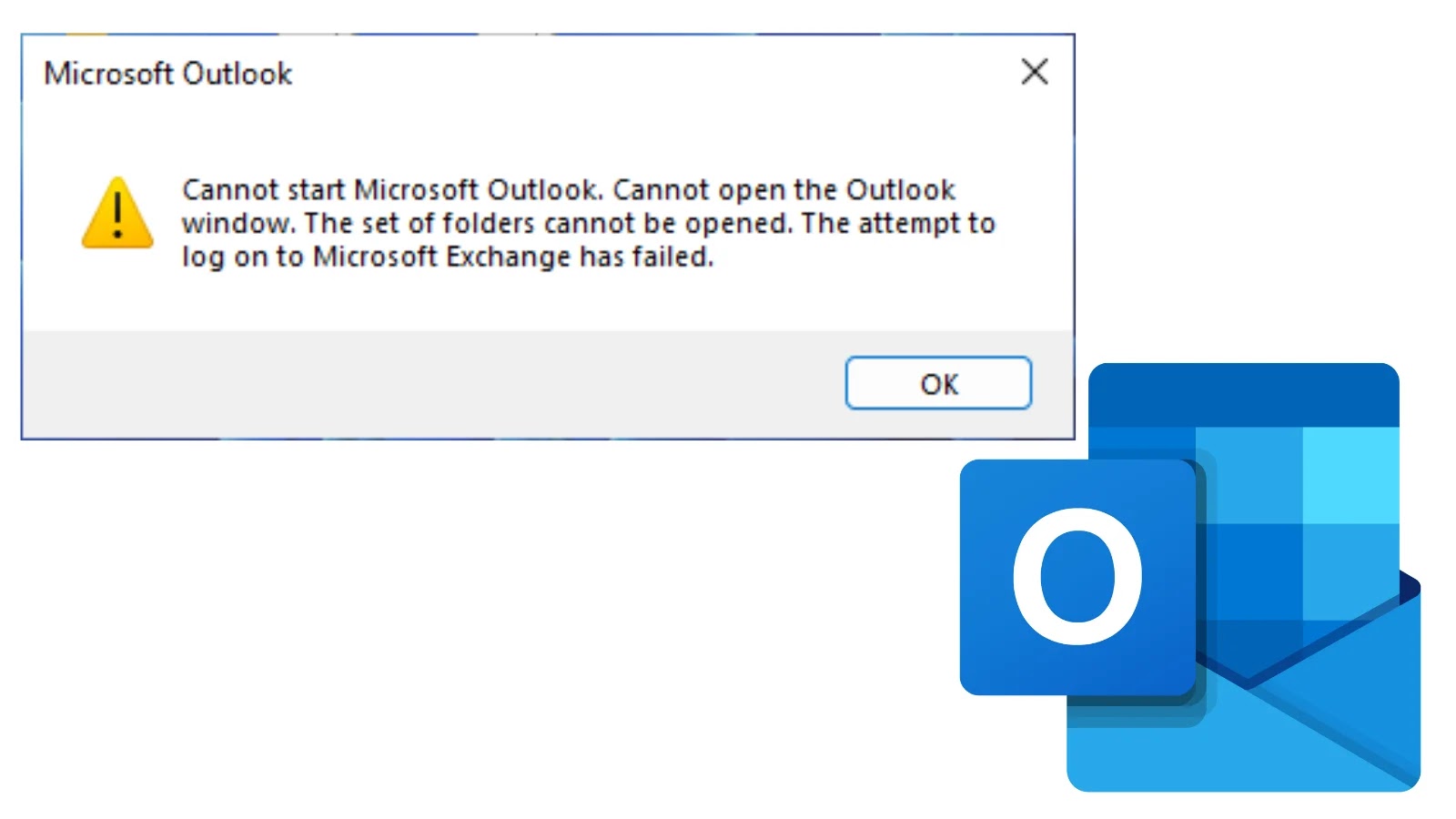
Outlook Crash Chaos: When Your Inbox Becomes a Black Hole For countless professionals, Microsoft Outlook is the digital nerve center of their workday. It’s [...]
A critical alert for all Google Chrome users and cybersecurity professionals: Google has rolled out an urgent security update, Chrome 141, to address a [...]
Red Hat Data Breach: The Crimson Collective’s Bold Claim of 28K GitHub Repositories Breached The digital landscape has once again been shaken by a [...]
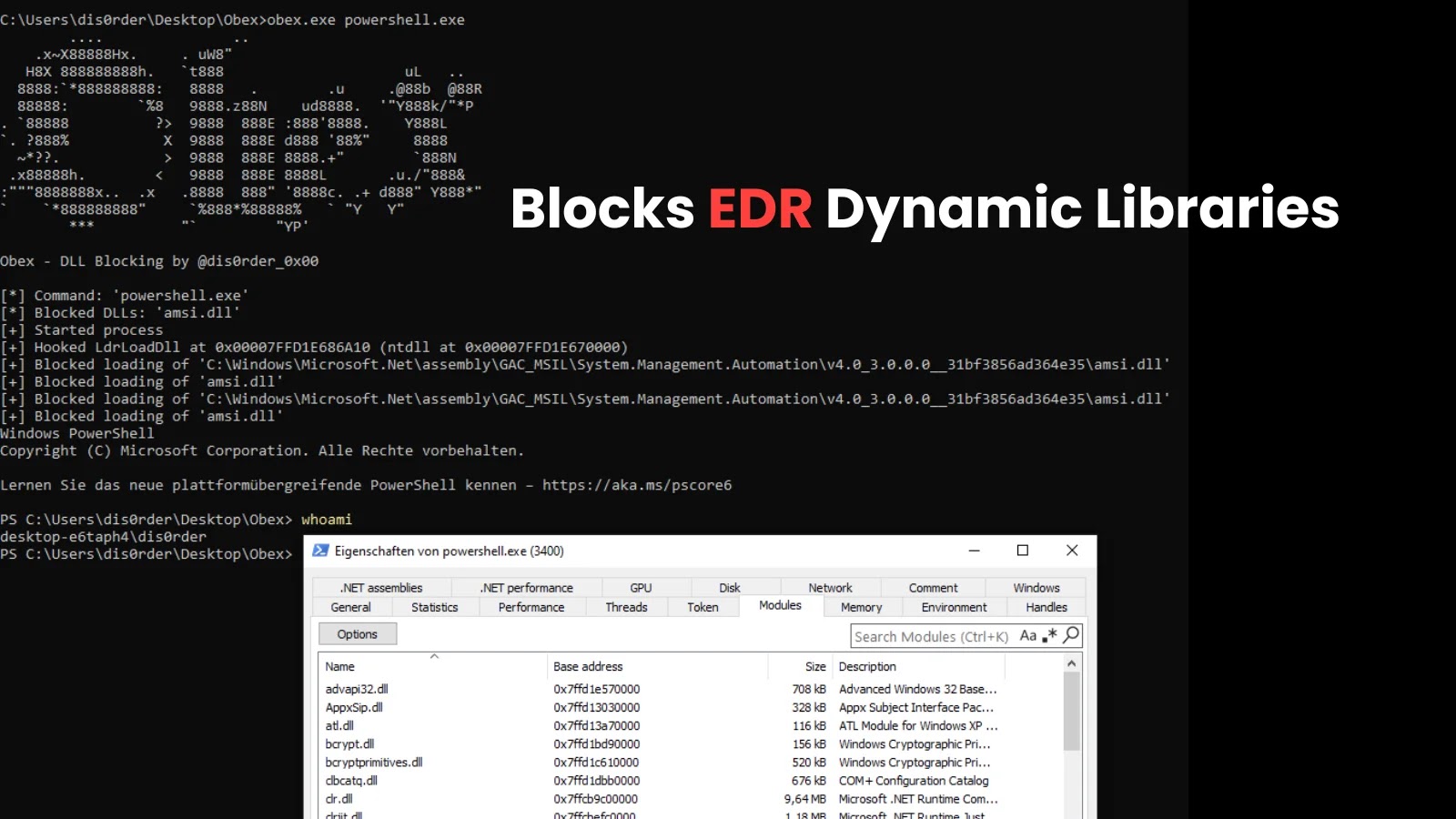
Endpoint Detection and Response (EDR) solutions are a cornerstone of modern cybersecurity, designed to monitor endpoints for malicious activity and provide threat visibility. However, [...]