Unmasking the Kubernetes C# Client Vulnerability: A Critical Look at MiTM Risks In the intricate landscape of cloud-native infrastructure, the integrity of communication channels [...]
Elevating Data Security: Google Sheets Now Features Client-Side Encryption In an era where data breaches are unfortunately common and compliance regulations are increasingly stringent, [...]
A fundamental security assumption for many organizations relies on BitLocker’s robust encryption to protect sensitive data on Windows systems. However, a recently disclosed critical vulnerability, [...]
FinWise Insider Breach: A Cautionary Tale of Data Exfiltration The digital landscape is fraught with perils, and while external threats often dominate headlines, the [...]
Linux Kernel’s KSMBD Vulnerability: A Critical Resource Exhaustion Threat In the complex landscape of server infrastructure, the stability and availability of services are paramount. [...]
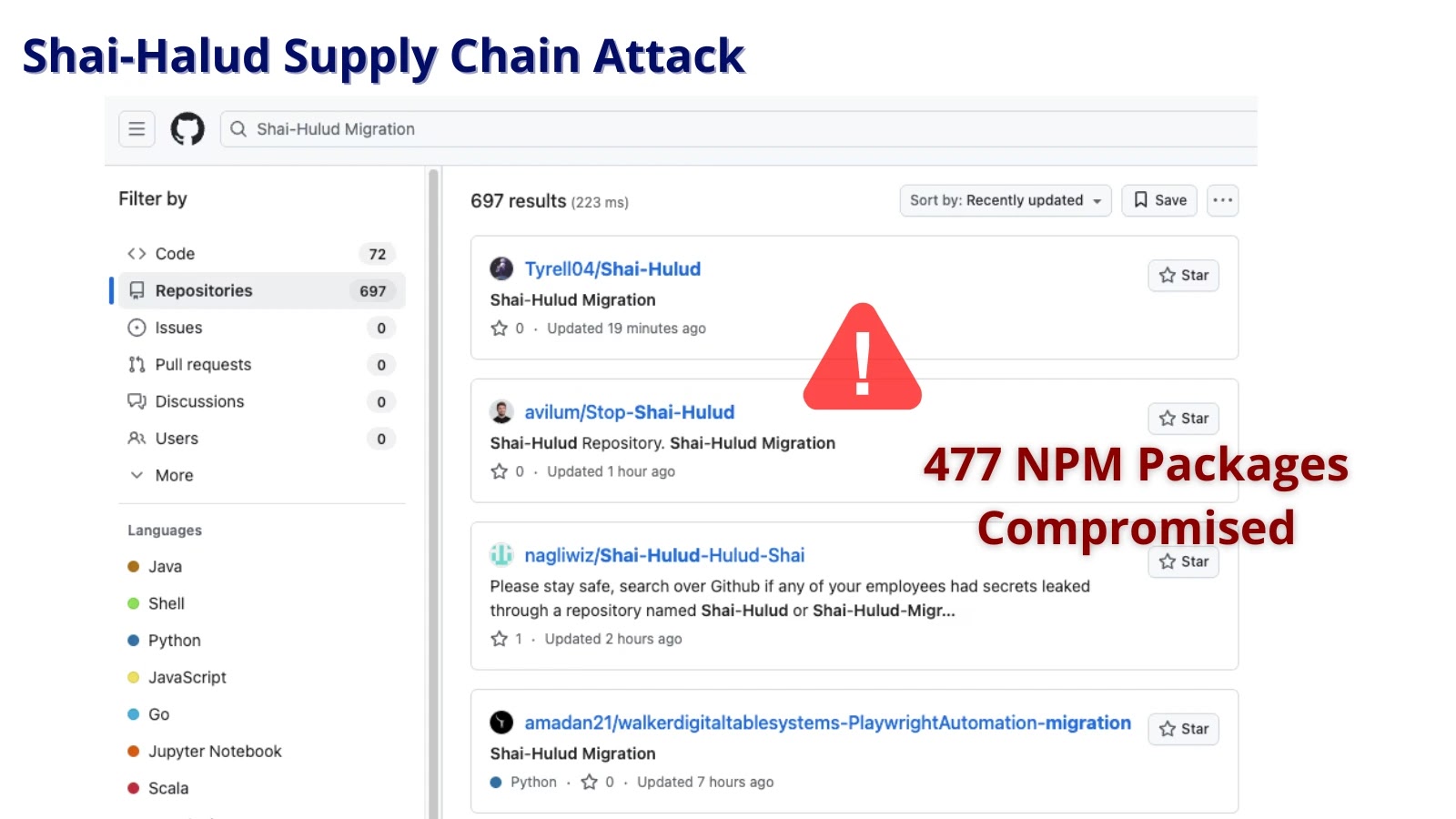
The JavaScript ecosystem, a cornerstone of modern web development, has once again been rocked by a sophisticated supply chain attack. Dubbed “Shai-Halud,” this large-scale [...]
The pace of modern business is unrelenting. In a landscape where innovation is key, speed often feels like an imperative. Yet, for any organization [...]
Elevating Enterprise Security: Seraphic Browser-Native Protection Joins the CrowdStrike Marketplace In the dynamic landscape of modern cyber threats, securing the endpoints where users interact [...]
The Silent Saboteur: How AI Code Assistants Can Be Weaponized for Backdoors and Malicious Content Modern software development thrives on efficiency, and AI-driven coding [...]
Unveiling the Critical Importance of Privileged Access Management (PAM) In the relentless landscape of modern cyber threats, safeguarding privileged accounts is not merely best [...]