A critical alert echoes across the cybersecurity landscape as unauthenticated remote attackers can now exploit serious vulnerabilities within Xerox FreeFlow Core, a widely adopted [...]
The digital frontier is under siege. Recent data from the first half of 2025 paints a stark picture: Web Distributed Denial of Service (DDoS) [...]
The Resurgence of ShinyHunters: A Tactical Evolution Targeting Salesforce and Potential Scattered Spider Alliance The digital threat landscape is in constant flux, with cybercriminal [...]
The landscape of cybersecurity is constantly shifting, and with the rapid advancements in artificial intelligence, a new and insidious threat has emerged: “AI-induced destruction.” [...]
Unmasking Out-of-Bounds Read and Write Vulnerabilities: A Critical Threat to System Integrity Imagine a digital fortress with robust walls, yet a hidden flaw allows [...]
DragonForce Ransomware: Unmasking a Rapidly Evolving Threat The cybersecurity landscape faces a persistent and often overwhelming challenge from ransomware operations. Among the newer, more [...]
Imagine navigating a legitimate website, intending to complete a routine task, only to be confronted by a CAPTCHA. You diligently solve it, as you’ve always [...]
Urgent CISA ICS Advisories: Critical Vulnerabilities Impacting Industrial Control Systems The Cybersecurity and Infrastructure Security Agency (CISA) has issued a series of critical advisories [...]
Urgent macOS Alert: SHAMOS Malware Surges, Threatening Credentials Via Fake Support Sites The digital landscape is under constant siege, and macOS users are now [...]
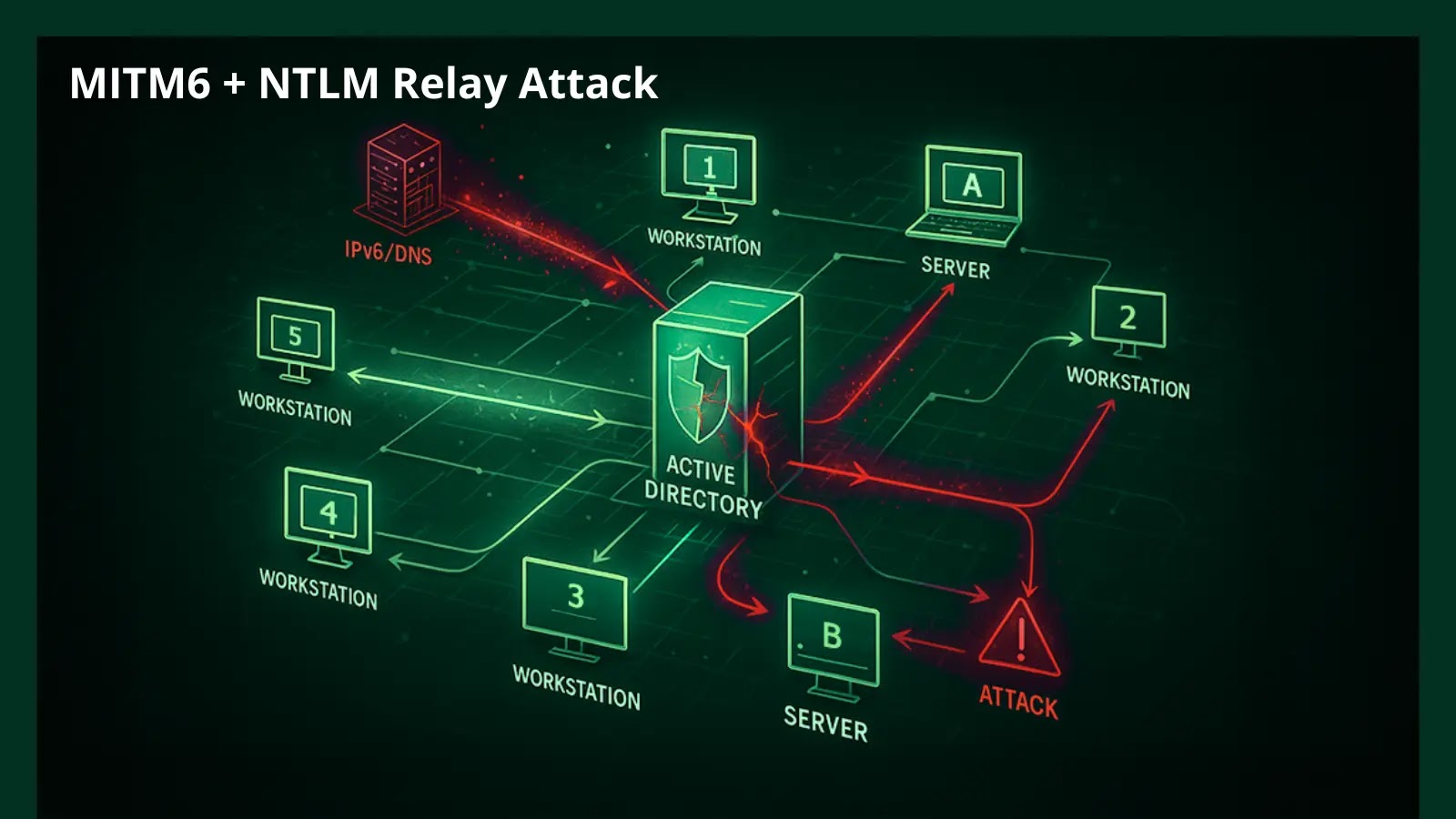
Unmasking the MITM6 + NTLM Relay Attack: A Path to Domain Admin in Minutes The digital landscape is a constant battleground, and threat actors [...]