Urgent Alert: New Android Malware Poses Severe Risk to Indian Banking Customers A sophisticated Android malware campaign has emerged, directly threatening the financial security [...]
Web Application Firewalls (WAFs) are a critical line of defense against cyberattacks, designed to protect web applications by filtering and monitoring HTTP traffic. However, [...]
The Open-Source Ecosystem: A New Battleground for Cybercriminals The open-source software ecosystem, long celebrated for its collaborative spirit and innovation, is facing an escalating [...]
The AI-Powered NPM Threat: How a Malicious Package Drains Crypto Wallets The landscape of cyber threats is continuously reshaped by innovative, and often alarming, [...]
Critical Squid Vulnerability: Understanding CVE-2025-54574 and Its Impact A significant security flaw has been uncovered in Squid Web Proxy Cache, posing a serious threat to [...]
The Silent Threat: Cursor IDE’s CurXecute Vulnerability Exposes Developer Machines The pace of software development demands efficiency, and AI-powered code editors like Cursor IDE [...]
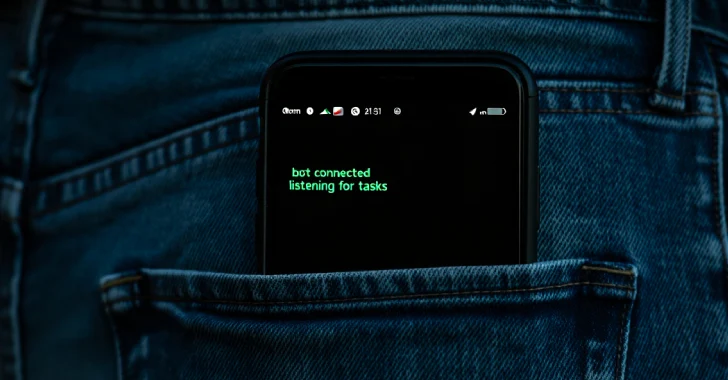
In a stark warning to Android users globally, cybersecurity researchers have unearthed a nascent yet alarmingly rapidly propagating remote access trojan (RAT) dubbed PlayPraetor. [...]
Interlock Ransomware Leverages ClickFix: A New Era of Social Engineering Threats The cybersecurity landscape is in a perpetual state of flux, with threat actors [...]
The digital streaming world, fueled by services like Netflix, Amazon Prime Video, and Disney+, relies heavily on robust Digital Rights Management (DRM) systems to [...]
Navigating the Evolving Threat Landscape: A Week in Cybersecurity The digital realm remains a dynamic battleground, constantly challenging defenders with emerging vulnerabilities and sophisticated [...]