Critical Zero-Day: Symantec Endpoint Management Suite Exposes Enterprises to Remote Code Execution The digital perimeter of enterprise networks is under constant siege, and a [...]
The digital battleground just escalated. Recent reports from Cloudflare reveal a worrying surge in hyper-volumetric Distributed Denial of Service (DDoS) attacks, with individual incidents [...]
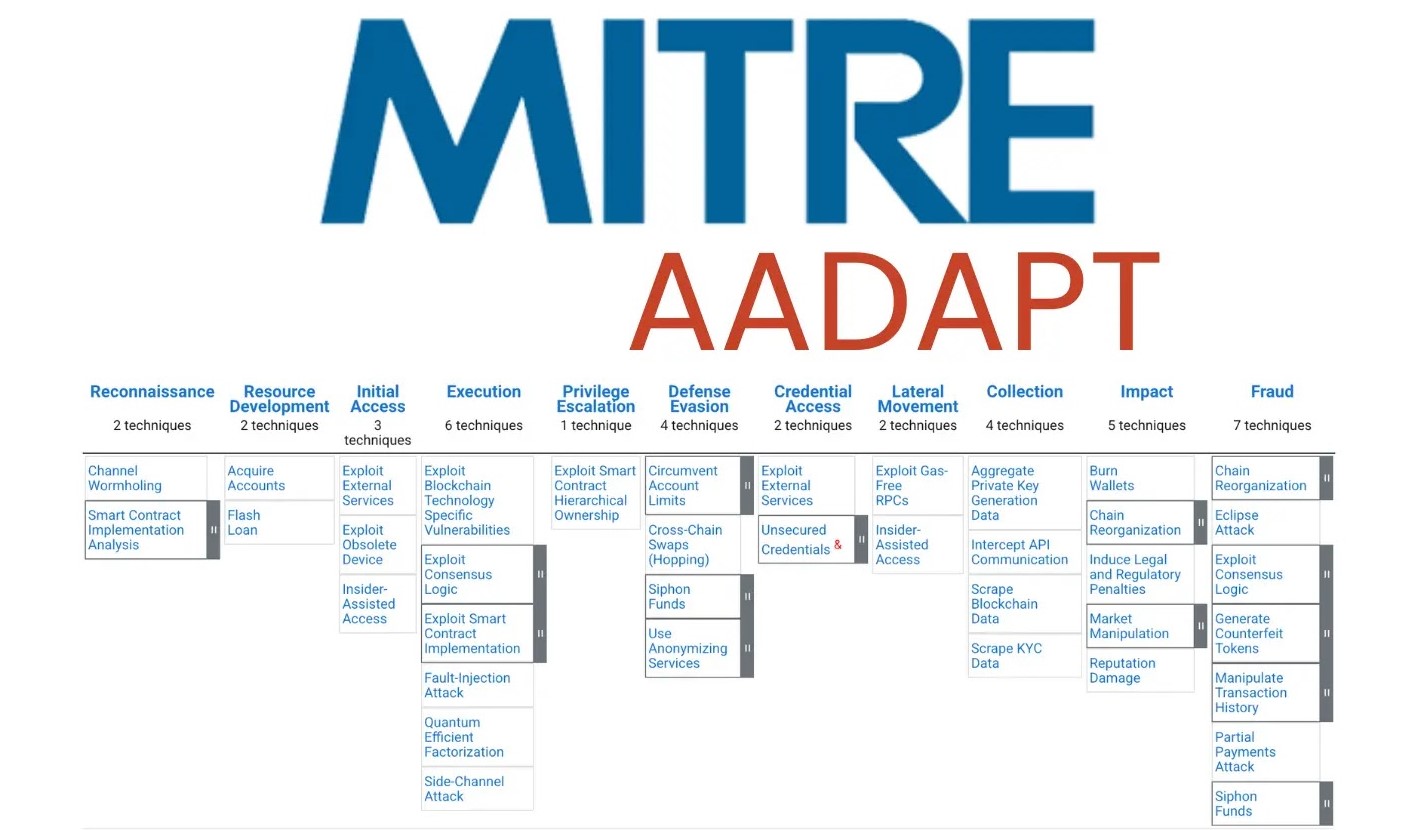
Unveiling AADAPT: MITRE’s Critical Framework for Digital Asset Security The landscape of digital assets, from cryptocurrencies to tokenized real estate, continues its meteoric rise, [...]
Unmasking the LaRecipe Vulnerability: A Critical Threat to Server Control In the expansive realm of software development, tools designed to streamline processes are invaluable. [...]
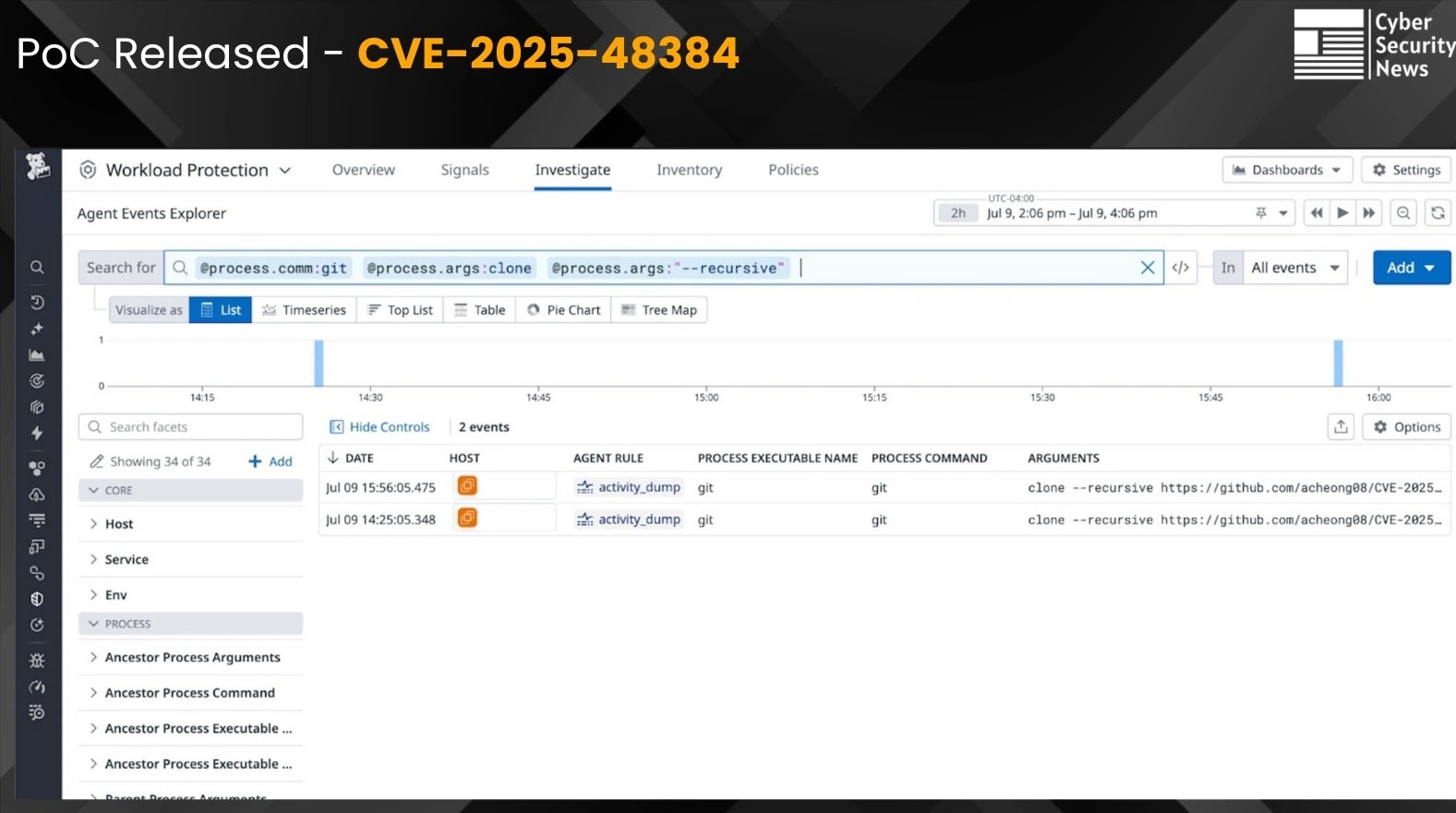
The rapid pace of software development relies heavily on version control systems, and Git stands as an undisputed leader. However, its pervasive use also [...]
In a significant victory against international cybercrime, a coordinated operation recently led to the arrest of fourteen individuals implicated in a large-scale tax fraud scheme. [...]
The promise of Artificial Intelligence agents automating complex tasks, from financial reconciliation to real-time incident response, heralds a new era of operational efficiency. Yet, [...]
AsyncRAT’s Open-Source Code Sparks Surge in Dangerous Malware Variants Across the Globe The dark underbelly of open-source development has once again revealed a critical [...]
State-Backed HazyBeacon Malware Leverages AWS Lambda for Data Exfiltration from SE Asian Governments Sensitive government data in Southeast Asia is under siege. A newly [...]
The open-source ecosystem, a cornerstone of modern software development, is under relentless assault. North Korean state-sponsored threat actors, notorious for their sophisticated tactics, have once [...]