Yesterday, a significant power outage at one of Microsoft’s West US data centers caused widespread service disruptions, highlighting the inherent vulnerabilities within even the [...]
The digital threat landscape is a perpetually shifting battleground. Cybercriminals, demonstrating an alarming adaptability, are increasingly “living off the cloud” – a strategy designed to [...]
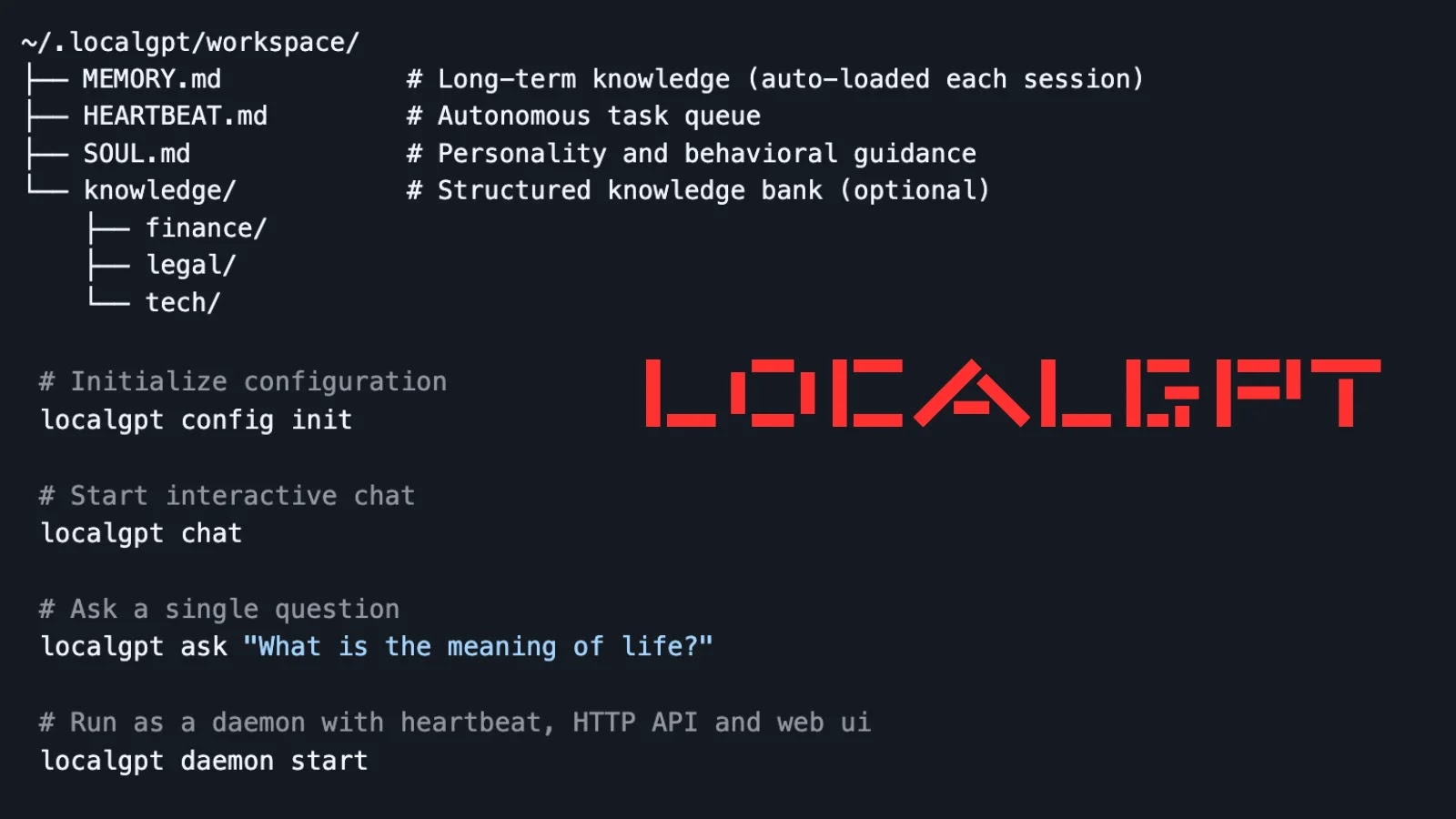
The proliferation of artificial intelligence (AI) has ushered in an era of unprecedented technological advancement, yet it has also presented new challenges, particularly concerning data [...]
The cyber threat landscape never sleeps, and this week brings a fresh wave of vulnerabilities and attacks demanding immediate attention from every IT professional [...]
Urgent Alert: SolarWinds Web Help Desk RCE Vulnerability Under Active Attack In a pressing development for organizations globally, a critical remote code execution (RCE) [...]
The rapid evolution of AI agents has ushered in unprecedented efficiency across various digital tasks, from managing complex email systems to orchestrating cryptocurrency trades. However, [...]
A significant cybersecurity threat has emerged, potentially impacting thousands of organizations globally. BeyondTrust, a leading provider of privileged access management solutions, has disclosed a critical [...]
Securing the AI Frontier: OpenClaw and VirusTotal Forge a Partnership for ClawHub’s Future The burgeoning landscape of Artificial Intelligence (AI) agents is transforming how businesses [...]
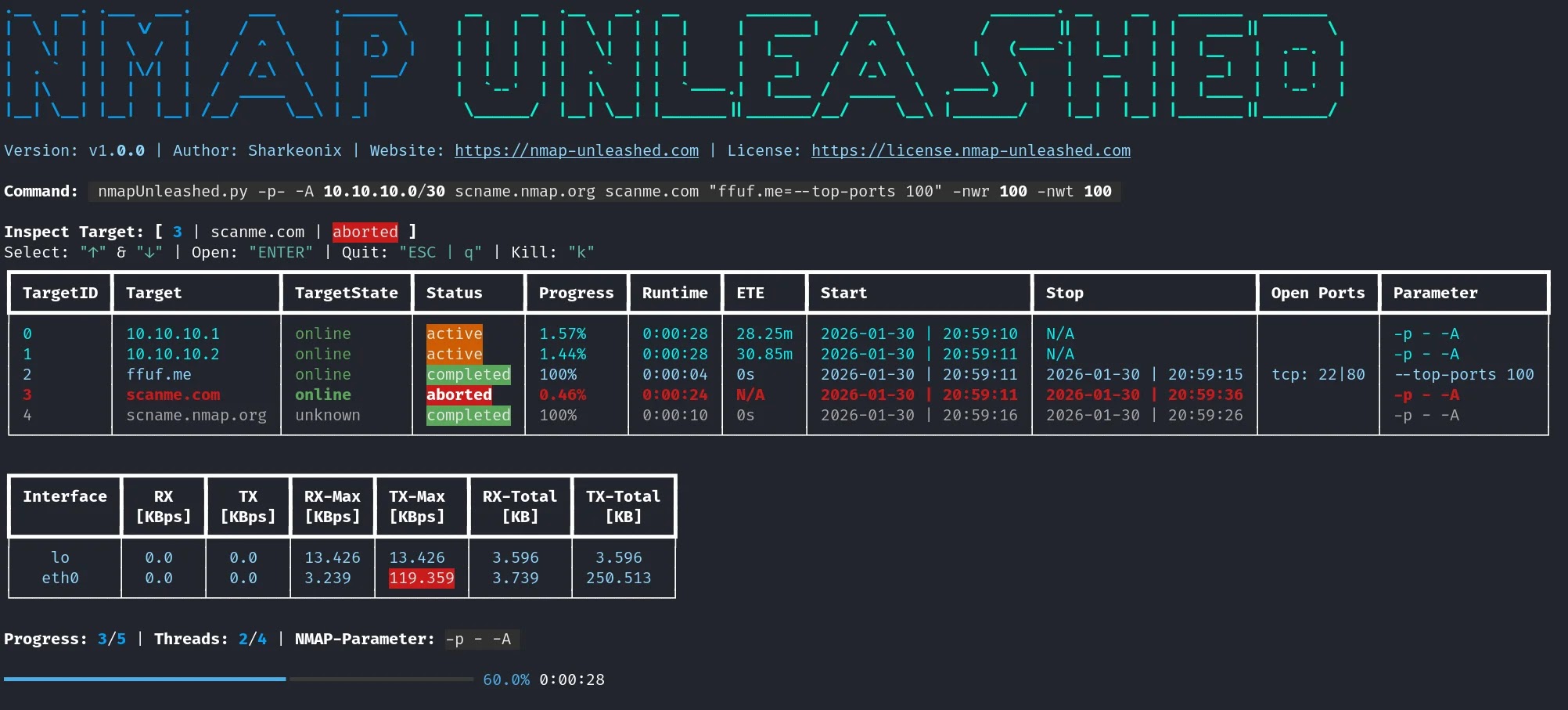
Network reconnaissance is the bedrock of effective cybersecurity. For decades, the Nmap (Network Mapper) tool has been the industry standard for uncovering network topology, identifying [...]
The Silent Threat: How Malicious Cybersquatting Becomes a Malware Gateway The digital landscape is a constant battleground, and even seemingly innocuous domain name disputes have [...]