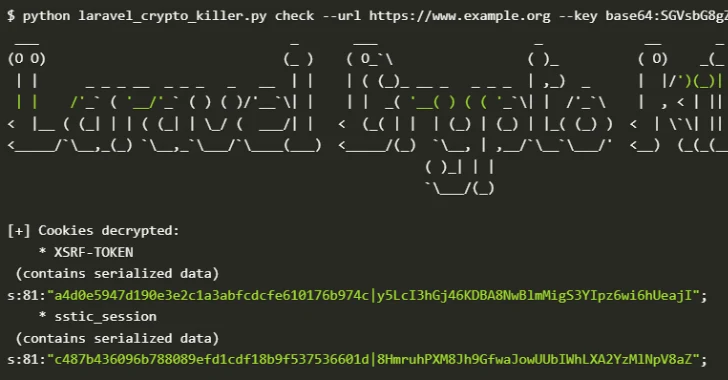
In the intricate landscape of web application security, a seemingly innocuous leak can trigger a cascade of critical vulnerabilities. Recent findings by cybersecurity researchers [...]
A Critical Flaw in AWS Organizations: Understanding the Full Control Takeover Risk In the complex landscape of cloud security, even seemingly minor misconfigurations can [...]
Qilin Surges: Unpacking the Rise of Ransomware’s New Apex Predator and Fortinet’s Unpatched Peril The digital threat landscape is in a perpetual state of [...]
The cybersecurity landscape has historically painted Windows as the primary target for malicious actors. However, a significant and concerning shift is underway: macOS users [...]
In the relentless pursuit of robust digital defenses, organizations face an escalating tide of sophisticated cyber threats. For enterprises operating within the Microsoft 365 [...]
The cybersecurity landscape is in constant flux, and the rapid emergence of new threats demands immediate attention. A recent critical warning from CISA highlights just [...]
Iranian APTs Intensify Cyber Warfare Against US Critical Infrastructure The digital battleground is expanding, and state-sponsored threat actors are increasingly targeting the very backbone [...]
The operational technology (OT) landscape faces a persistent and evolving threat. On July 10, 2025, the Cybersecurity and Infrastructure Security Agency (CISA) issued a [...]
Urgent Warning: Critical Wing FTP Server Vulnerability Actively Exploited in the Wild (CVE-2025-47812) A severe security flaw affecting Wing FTP Server, tracked as CVE-2025-47812, [...]
Bluetooth Vulnerabilities Expose Millions of Vehicles to Remote Code Execution The modern vehicle is a sophisticated network of interconnected systems, with Bluetooth connectivity often [...]