A Startling Shot: When Cybercrime Hits the Court The arrest of a professional basketball player on charges of orchestrating an extensive ransomware campaign sends [...]
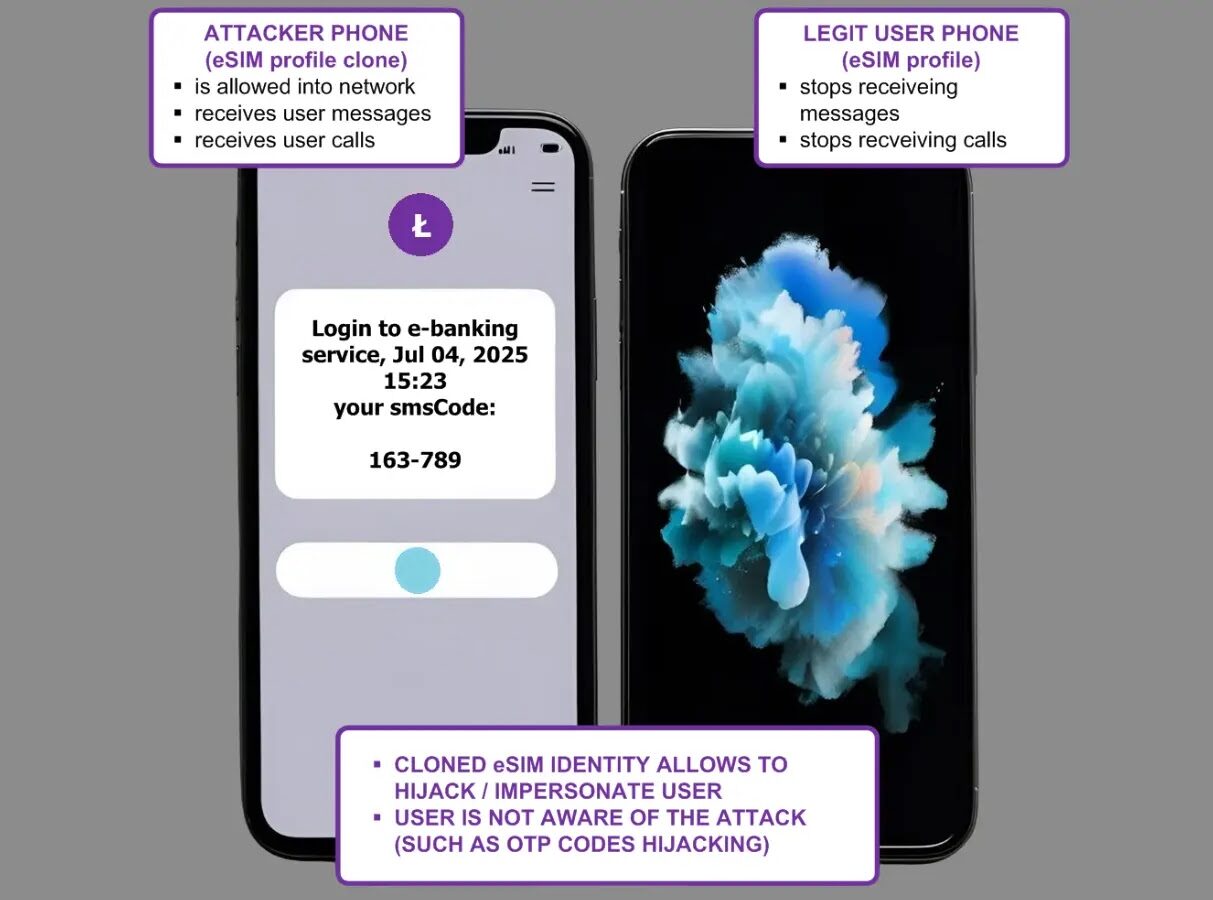
The ubiquity of mobile devices in our daily lives means the security of our cellular connections is paramount. With the advent of eSIM technology, [...]
The digital landscape is relentlessly challenged by persistent security threats. Among the most concerning vulnerabilities are those that demand no prior authentication or user [...]
Apache HTTP Server 2.4.64: Critical Update Addressing 8 Vulnerabilities Maintaining a secure web infrastructure is paramount for any organization. The Apache HTTP Server, a [...]
AMD Warns of Transient Scheduler Attacks: A Deep Dive into Processor Vulnerabilities The landscape of processor security has been significantly reshaped by a recent [...]
The digital threat landscape is in constant flux, and security teams worldwide are grappling with sophisticated attacks that leverage newly discovered vulnerabilities. A critical [...]
Rockerbox Data Leak: 245,949 Sensitive Records Exposed – A Deep Dive into Cloud Misconfiguration Risks In the relentless current of data breaches, a new [...]
The relentless evolution of cybercrime presents a significant challenge to digital security. As threat actors grow more sophisticated, the imperative for robust digital forensic [...]
In the dynamic landscape of modern IT, system administrators (SysAdmins) serve as the bedrock of organizational effectiveness and security. Their ability to ensure seamless [...]
Unveiling Windows 11’s New Black Screen of Death: A Critical UI Shift In the complex landscape of operating systems, stability and user experience are [...]