A Critical Cybersecurity Breach: eScan Antivirus Update Server Hacked The digital landscape is a constant battleground, where even the most trusted tools can become vectors [...]
The Looming Shutdown: Microsoft Exchange Online Deprecates SMTP AUTH Basic Authentication A significant security transformation is on the horizon for cloud email users. Microsoft [...]
Critical SolarWinds Web Help Desk Vulnerabilities Expose Organizations to Remote Code Execution A recent discovery by Horizon3.ai researchers has unveiled a severe chain of [...]
Unmasking the Semantic Chaining Jailbreak: A New Threat to Grok 4 and Gemini Nano The rapid advancement of artificial intelligence, particularly in multimodal Large [...]
Unmasking Swarmer: How a New Tool Sneaks Past EDR with Stealthy Registry Persistence In the evolving landscape of cyber threats, defenders constantly refine their [...]
The year is 2026, and your digital footprint is no longer a mere collection of online activities; it’s a rapidly expanding attack surface. Every [...]
A critical security vulnerability has surfaced within Check Point’s Harmony SASE (Secure Access Service Edge) Windows client software, posing a significant risk to organizations utilizing [...]
SoundCloud Data Breach: Unpacking the Exposure of 29.8 Million User Accounts In an era where digital footprints are increasingly extensive, the security of personal data [...]
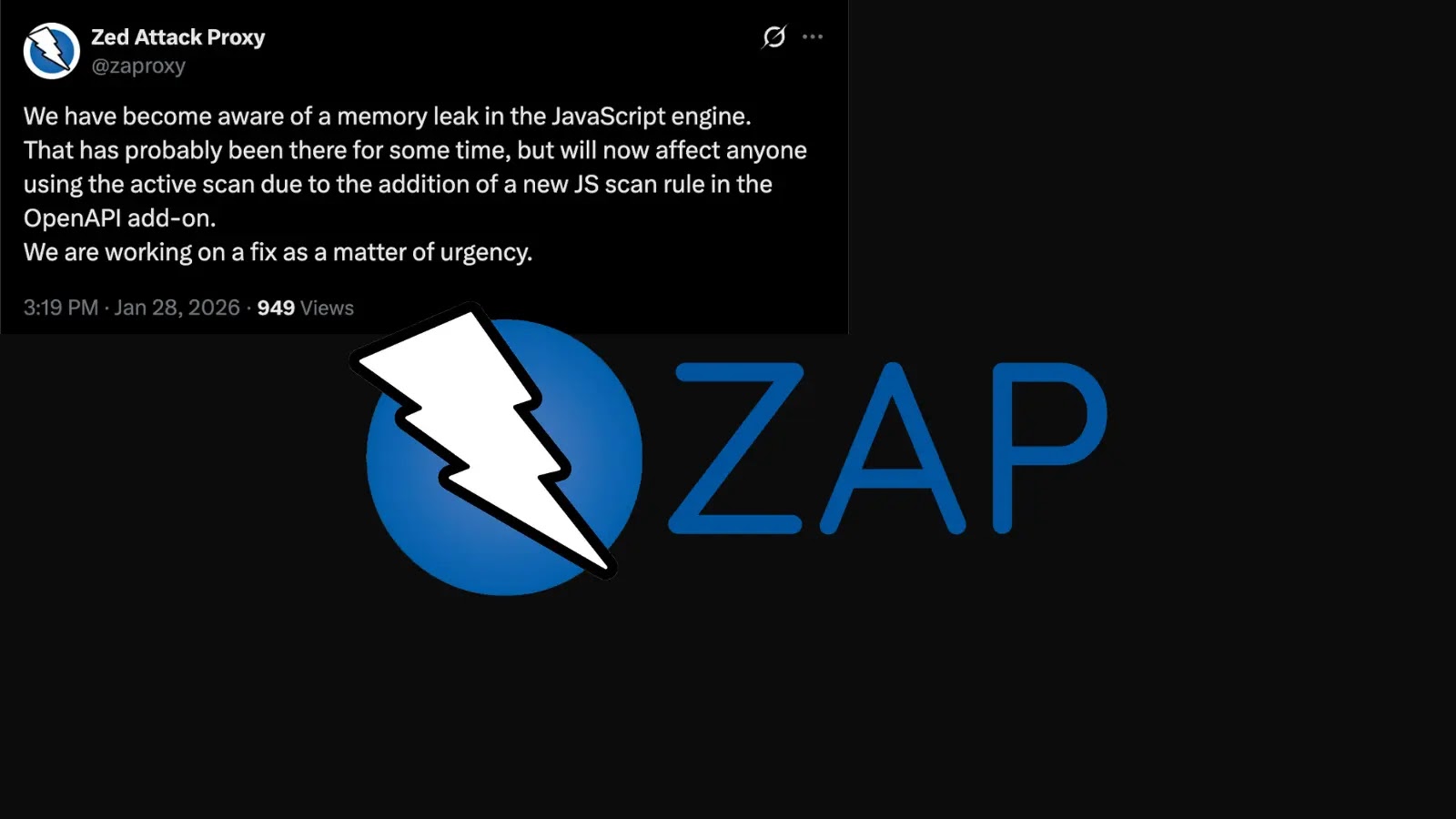
ZAP JavaScript Engine Memory Leak Undermines Active Scanning Capabilities The Zed Attack Proxy (ZAP) project, a cornerstone open-source web application security scanner, has recently brought [...]
A silent threat has emerged from the shadows, casting a long and concerning shadow over the security landscape. A critical zero-day vulnerability in the Gemini [...]