Secure Access Service Edge (SASE): What is it? The digital transformation rapidly reshaping today’s business landscape demands a robust approach to network security and access. [...]
In Cybersecurity for Autonomous Vehicles: Securing the Future As the automotive industry races toward a future filled with autonomous vehicles, the significance of cybersecurity for [...]
Social Engineering Attacks in 2025: The Psychology of Social Engineer In the ever-evolving landscape of cybersecurity, understanding the psychology of social engineers and the tactics [...]
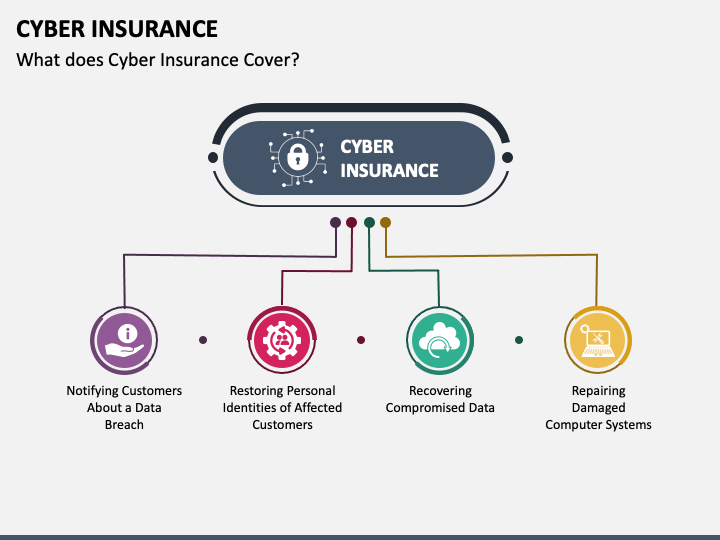
What it Cyber Insurance Policies Doesn’t Covers: Coverage and Cyber Liability In an era where digital threats loom large, securing your business against cyber [...]
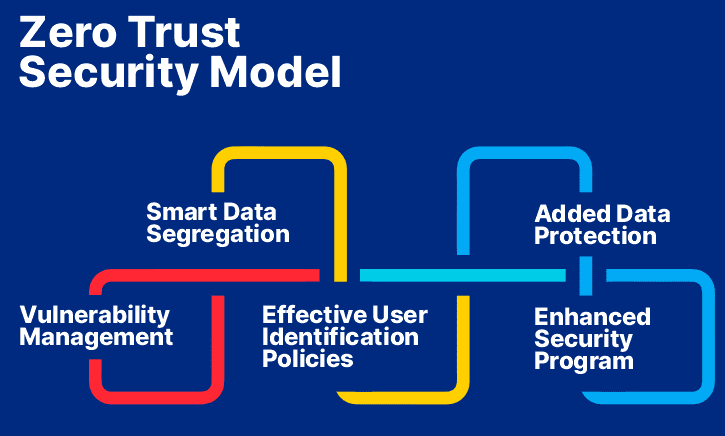
In today’s digital age, where cyber threats are increasingly sophisticated and pervasive, traditional security models that rely on implicit trust are no longer sufficient. [...]
Cybersecurity for Smart Cities: Preserving the Future As cities transform into smart cities, technology is being incorporated into daily life more and more. Interconnected systems [...]
As we navigate the increasingly complex digital landscape of 2024, the intersection of artificial intelligence and cybercrime presents unprecedented challenges for cybersecurity professionals and organizations [...]
In today’s digital age, cybersecurity is paramount, especially for startups and small businesses. These organizations often face unique challenges in protecting their sensitive information and [...]
In today’s digital landscape, cybersecurity is not just about firewalls and antivirus software; it’s also about understanding the human element. A social engineering attack represents [...]
Your Digital Network: Guidance & Essentials for Business Success In today’s interconnected world, understanding the intricacies of digital networks is crucial for business success. Digital [...]