In the rapidly evolving world of technology, maintaining a reliable network infrastructure is vital for any business aiming to achieve operational excellence. At Teamwin Global [...]
In today’s digital age, ensuring the security of your wireless network is more critical than ever. As businesses and individuals increasingly rely on wireless connectivity, [...]
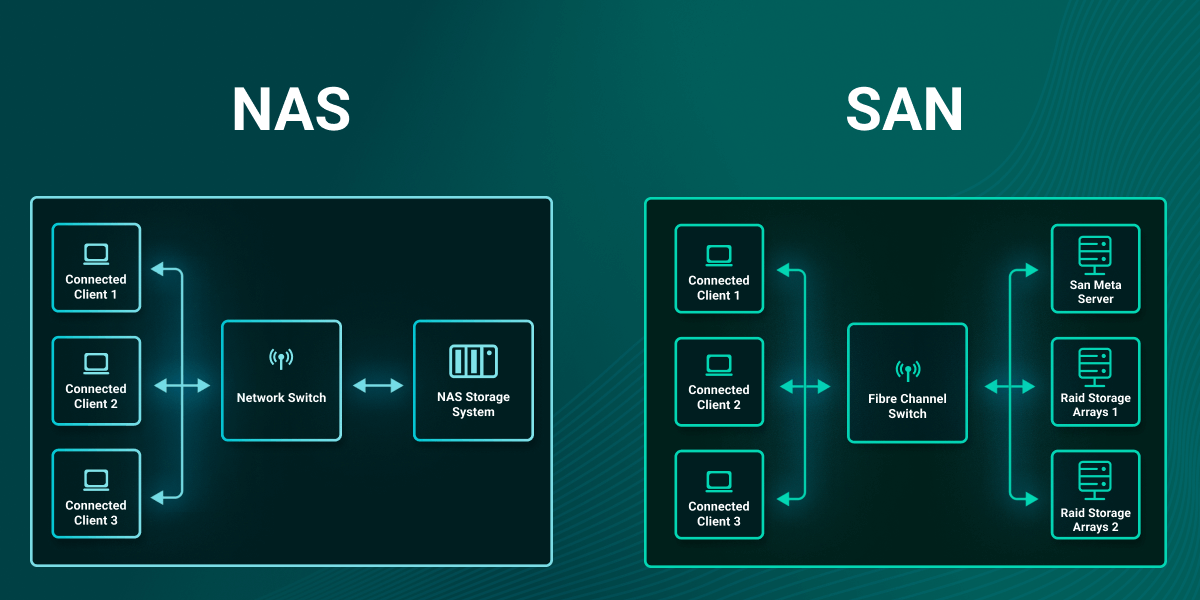
How to Choose Between SAN and NAS: Storage Area Network vs Network Attached Storage In the rapidly evolving domain of data management, understanding storage options [...]
Network Security Mistakes Small Businesses Make In today’s digital landscape, small businesses face a myriad of cybersecurity threats that demand attention and proactive measures. As [...]
In today’s digital landscape, safeguarding sensitive data and protecting intellectual property is paramount for any enterprise, which is why robust privileged identity management is essential. [...]