What is a SOC Framework, Elements & Benefits of Security Operation Centre If a company is serious about cybersecurity, its beating heart will be the Security [...]
Multiple Fortinet Vulnerabilities Let Attackers Execute Arbitrary Code Multiple vulnerabilities have been discovered in FortiOS and FortiProxy that were related to administrator cookie leakage, arbitrary [...]
10 Best Network Security Solutions for IT Managers Network security solutions employ a variety of techniques to prevent attacks targeting networks. To filter incoming and [...]
Exploring the Latest Trends in Firewall Technology Firewalls remain a critical component of network security, acting as the first line of defense against cyber threats. [...]
The Importance of VPNs for Network Security In the past, securing a network meant controlling access to servers physically located on the premises. The IT [...]
Uncovering Shadow IT Risks in Your Network Security Shadow IT refers to IT systems, applications, and services that are used within an organization without explicit [...]
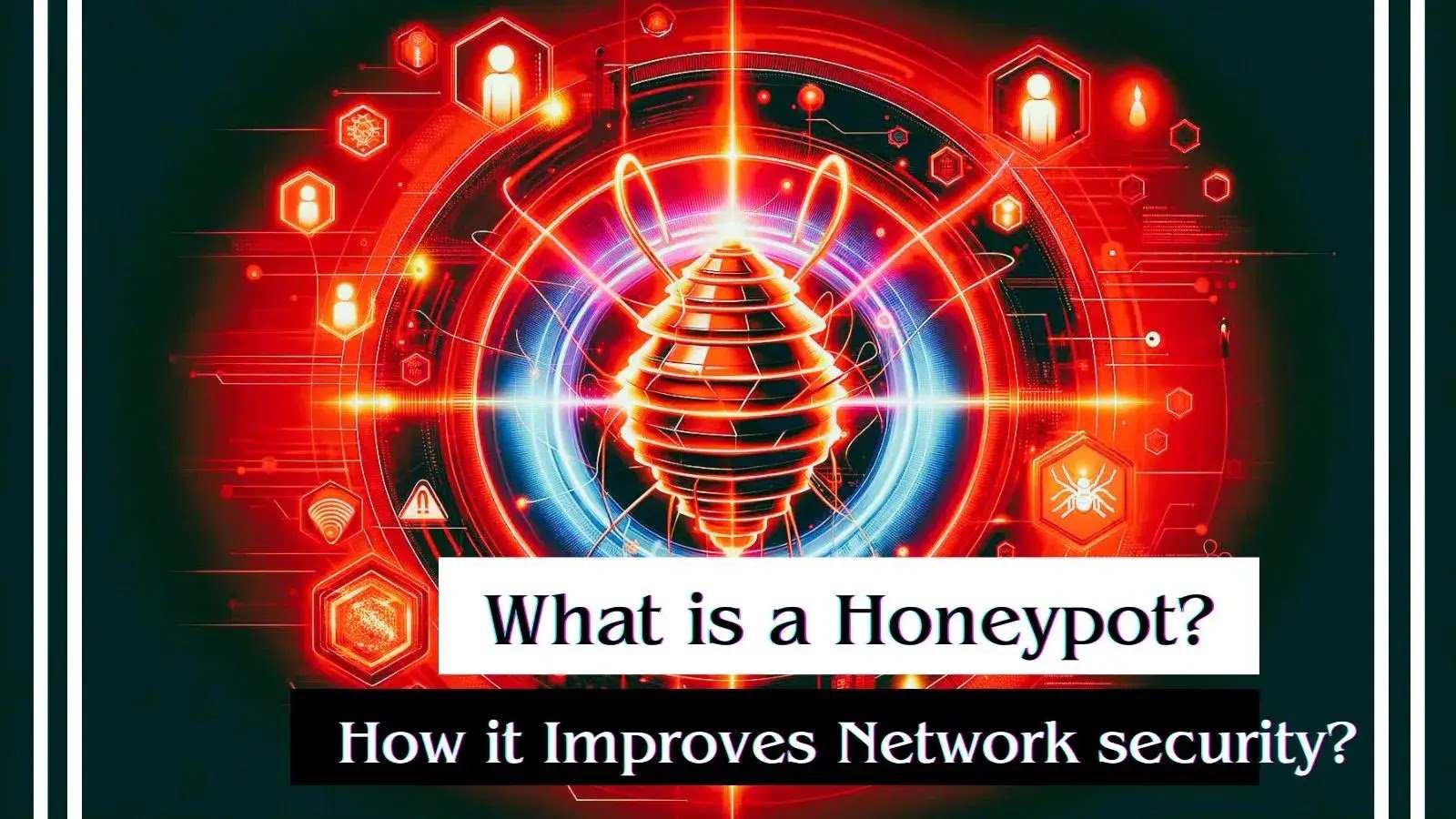
What is a Honeypot? How does it Improve Network security? One security measure that can be used to entice attackers is a honeypot, which creates [...]
Top 10 Security Service Edge (SSE) Solutions for Network Security – 2024 Security Service Edge (SSE) is an idea in cybersecurity that shows how network [...]
What is a Security Operations Center (SOC)? In this article, we will explore the concept of a Security Operations Center (SOC) in greater detail, including [...]
Network Security Checklist – Complete Guide To Protect Enterprise Networks (2024) Network security is paramount in today’s digital landscape, where organizations face increasingly sophisticated threats. [...]