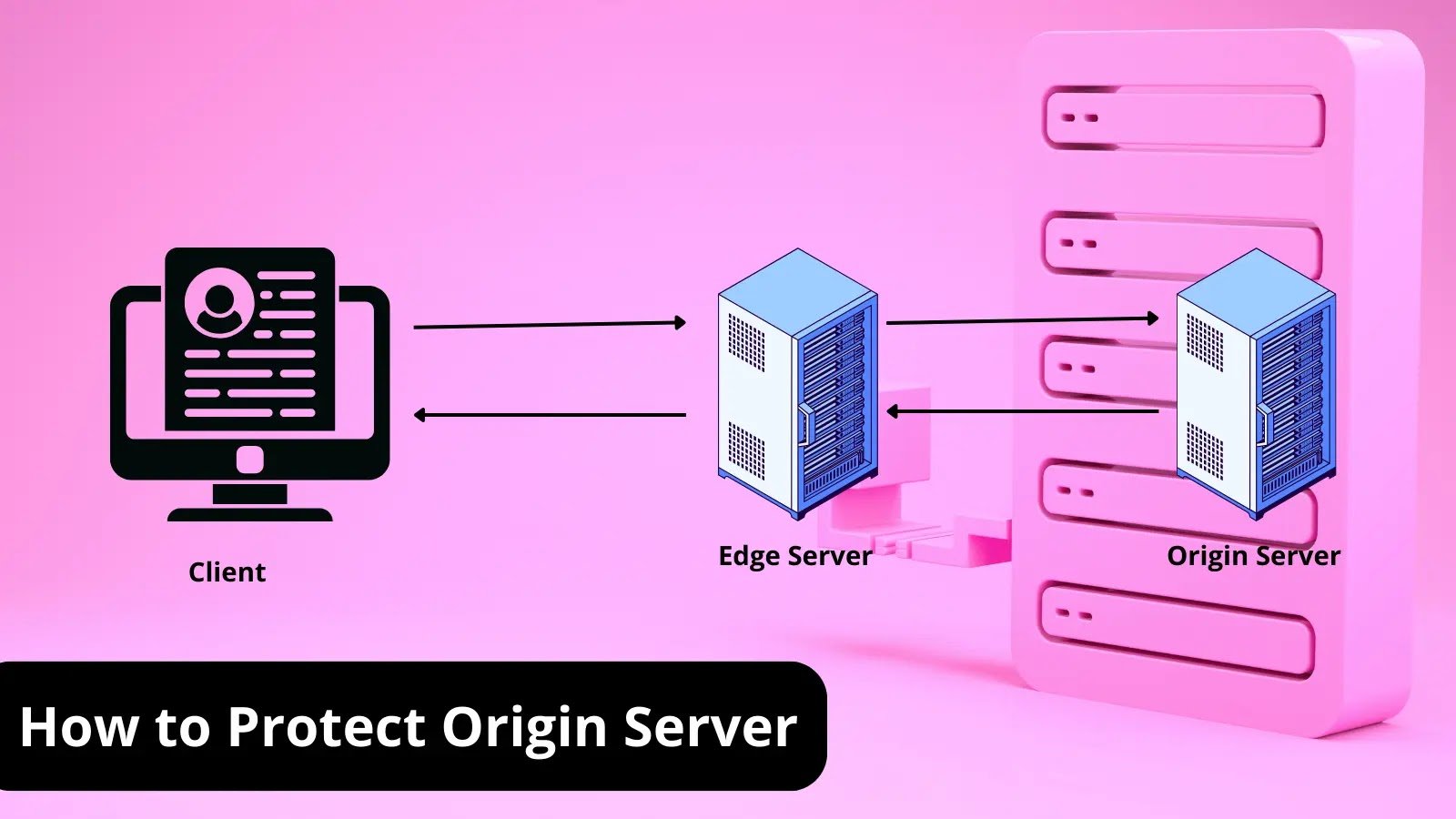
What is Origin Server? How To Protect it? A Detailed Guide The origin server stores a website’s or application’s content and data. As the starting [...]
3 Key Ways VPNs Can Benefit Your Business In an age when security and privacy have become major considerations on the Internet, VPNs have become [...]
The age-old adage knowledge is power has never rung truer than in today’s digital era where cyber threats lurk around every corner. However, amidst these [...]
Take an Offensive Approach to Password Security by Continuously Monitoring for Breached Passwords Passwords are at the core of securing access to an organization’s data. [...]
Imagine waking up one morning only to find your bank account emptied or your personal photos leaked online for the world to see. Scary thought, [...]
Hackers Turned Mac Systems into Proxy Exit Nodes: In a world where cyber threats are becoming increasingly sophisticated, it seems no operating system can escape [...]
Multiple vulnerabilities in CyberPower PowerPanel Enterprise DCIM (Data Centre Infrasture Management) platform and Dataprobe PDU could expose data centers to hacking. Researchers from Trellix Advanced [...]
In today’s fast-paced business environment, staying ahead of the competition requires more than just making smart decisions – it necessitates having the right tools to [...]
In a world where artificial intelligence continues to advance at an unprecedented pace, the emergence of EvilGPT has sent shockwaves throughout the tech industry and [...]
“WormGPT vs Antivirus Systems: A Never-Ending Battle in Cyberspace” In the sprawling expanse of cyberspace, an eternal clash of wits unfolds between two formidable adversaries: [...]