WormGPT: The Dangers and Potentials of Artificial Intelligence Malware? In a world where technology continues to advance at an unprecedented pace, the emergence of artificial [...]
In an era where cybercrime is becoming increasingly sophisticated, the need for robust defense systems has never been greater. Enter WormGPT, the revolutionary AI-powered guardian [...]
The Impact of CCTV Surveillance: Empowering or Discriminating Marginalized Communities? In an increasingly interconnected world, the proliferation of Closed Circuit Television (CCTV) surveillance systems has [...]
How can PAM/PAS solutions integrate with cloud environments and hybrid infrastructures? In today’s fast-paced and interconnected world, businesses are increasingly adopting cloud environments and hybrid [...]
In an era of increasing concerns about security and public safety, Closed Circuit Television (CCTV) surveillance has emerged as a powerful tool in preventing and [...]
How can Artificial Intelligence and Machine Learning be integrated with CCTV cameras to enhance security and analytics? Integrating artificial intelligence (AI) and machine learning (ML) [...]
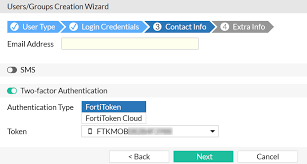
Transfer FortiToken Mobiles: Enhancing Security or Vulnerability Risk? Transfer FortiToken Mobiles is a feature that allows users to seamlessly move their FortiToken Mobile authentication app [...]
What is DDoS? DDoS stands for “Distributed Denial of Service.” It is a type of cyber-attack in which multiple compromised computers or devices (often referred [...]
What is Spoofing Attack? Spoofing is the act of disguising a communication or identity so that it appears to be associated with a trusted, authorized [...]
Which types of password cracking techniques are used by hackers? In ethical hacking, password cracking techniques are used to assess the security of systems and [...]