Installation and Configuration Process of CC TV Cameras. Planning: Identify the areas you want to monitor and determine the number of cameras needed. Consider factors [...]
Different types of CCTV Cameras and their Uses: CCTV (Closed Circuit Television) cameras come in various types, each designed for specific purposes and environments. Here [...]
Forti Guard Intrusion Prevention service The Ultimate Guide to Forti Guard Intrusion Prevention Service: Protecting Your Network Like Never Before FortiGuard Intrusion Prevention Service (IPS) is [...]
Five key principles of Resilience – PAM Privileged Access Management (PAM), there are several key principles that contribute to building resilience and enhancing security. While [...]
Protecting Backups with PAM Protecting backups with Privileged Access Management (PAM) involves securing and controlling access to privileged accounts and actions that can impact backup [...]
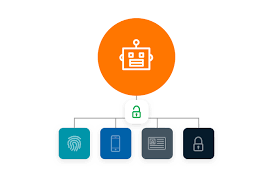
Are PAM (Privileged Access Management) and IAM (Identity And Access Management) the same? Let us explain the difference. PAM and IAM are same or not. [...]
How does Privileged Process Automation Work? Privileged Process Automation (PPA) refers to the automation of privileged tasks and processes within an organization’s IT infrastructure. It [...]
What are the Ransomware attacks and preventing ransomware from being devasting What are Ransomware attacks? Ransomware attacks are a type of malicious cyber attack where [...]
Responding to the Unique needs of Managed Security Service Provider. Managed Security Service Providers (MSSPs) play a crucial role in helping organizations address their security [...]
Security service boundary in Cloud computing and what are the responsibilities of Cloud Service Provider and Cloud Customer? In cloud computing, the security service boundary [...]