converge your vision and values
🛡️ PIM & PAM Solutions – Teamwin Global
Secure, Monitor & Control Privileged Access.
Protect critical assets with advanced Privileged Identity & Access Management solutions.
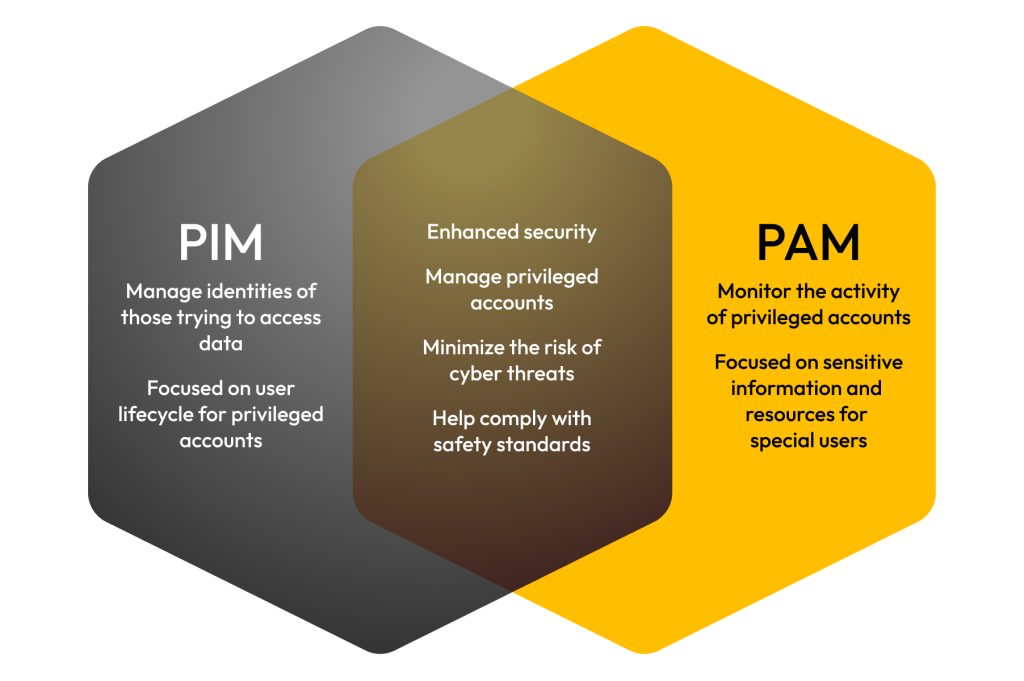
🔍 What is PIM/PAM?
-
Control & audit privileged accounts
-
Prevent insider threats & data breaches
-
Support Zero Trust & compliance
🎯 Why It Matters
-
🛑 Block unauthorized access
-
📋 Ensure compliance (ISO, GDPR, HIPAA)
-
👀 Full visibility of privileged sessions
🧩 Vendor Solutions We Offer
| Vendor | Category |
|---|---|
| CyberArk | Enterprise PAM, Vaulting |
| BeyondTrust | Endpoint & Session Mgmt |
| Delinea (Thycotic) | Vaulting & Policy Control |
| ManageEngine PAM360 | Affordable PAM for SMBs |
| One Identity | Session Monitoring |
| HashiCorp Vault | Secrets Management |
| Wallix | EU Compliance Focused |
| ARCON | Identity Governance & PAM (India) |
| Secureden | Lightweight PAM for SMEs |
⚙️ Key Features
-
🔑 Privileged Access Control
-
📈 Session Recording & Auditing
-
⏱️ Just-in-Time Access
-
🔐 Password Vaulting
Expertise and Experience:
Highly Skilled Team: Our team consists of certified professionals with extensive experience in various IT domains.
Comprehensive Solutions:
End-to-End Services: We offer a wide range of services, including network management, cybersecurity, cloud solutions, and IT consulting.
why choose us
Our Cyber Security & Secure networking Services
Fast. Reliable. Future-Ready. 🧠 1. Introduction Brief overview of modern enterprise networking needs Importance of speed, reliability, and smart planning 🔀 2. 10G Network Switching [...]
Biometric devices and management platforms are central to modern enterprise identity and access control. Together, they provide secure, efficient, and scalable solutions for employee authentication, [...]
Structured Cabling & Managed IT Services by TeamWin TeamWin delivers trusted structured cabling services and networking solutions tailored for businesses of all sizes. Our expert [...]
Articles from the latest news
Latest Tech Articles news
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in OpenSSL Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: MEDIUM Software Affected OpenSSL version 3.6. [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in Progress ShareFile Storage Zones Controller (SZC) Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: CRITICAL [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in Microsoft Azure and Bing Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: CRITICAL Software Affected [...]




