the latest from the industry
tech blog for cyber security and tech updates
In an era where cyber threats loom larger than ever, organizations must critically assess their cybersecurity measures to avoid vulnerabilities that could lead to significant breaches. As the digital landscape evolves, networking solutions companies are faced with a multitude of challenges, including conducting comprehensive IT security assessments and implementing advanced threat protection systems. Best practices in cybersecurity are not merely optional; they are essential for safeguarding sensitive data and maintaining operational integrity. From endpoint security solutions provided by industry leaders such as Crowdstrike, SentinelOne, and Sophos, to infrastructure support from companies like Aruba and Ubiquiti, businesses must adopt a proactive approach to ensure their networks remain secure.
To bolster defenses against cyber threats, organizations can leverage a variety of solutions tailored to their specific needs. For instance, utilizing firewall technologies from FortiGate or Checkpoint can create robust barriers against unauthorized access, while tools like TrendMicro and Seqrite offer advanced threat detection capabilities. Additionally, engaging with cybersecurity consulting firms that specialize in risk assessment and remediation can provide invaluable insights into potential vulnerabilities within an organization’s network architecture. With the complexity of today’s digital environments, companies must also consider incorporating enterprise WiFi heatmap analyses to optimize network performance and security, ensuring that every corner of their infrastructure is fortified against intrusion.
Ultimately, the responsibility for cybersecurity lies with each organization. By embracing a culture of vigilance and continually updating security protocols, businesses can significantly enhance their resilience against evolving cyber threats. Utilizing solutions from established names such as SonicWall, D-Link, and CommScope will not only strengthen defenses but also instill confidence in stakeholders about the organization’s commitment to safeguarding its assets. As the stakes rise, investing in cybersecurity measures is no longer a choice but a necessity in today’s interconnected world.
The Silent Menace: Threat Actors Weaponizing Malicious Go Packages Supply chain attacks represent a critical and escalating threat in the cybersecurity landscape. Unlike traditional [...]
The digital frontier of cryptocurrency, while promising immense innovation, also presents a fertile ground for sophisticated cyberattacks. Imagine logging into your trusted crypto wallet, only [...]
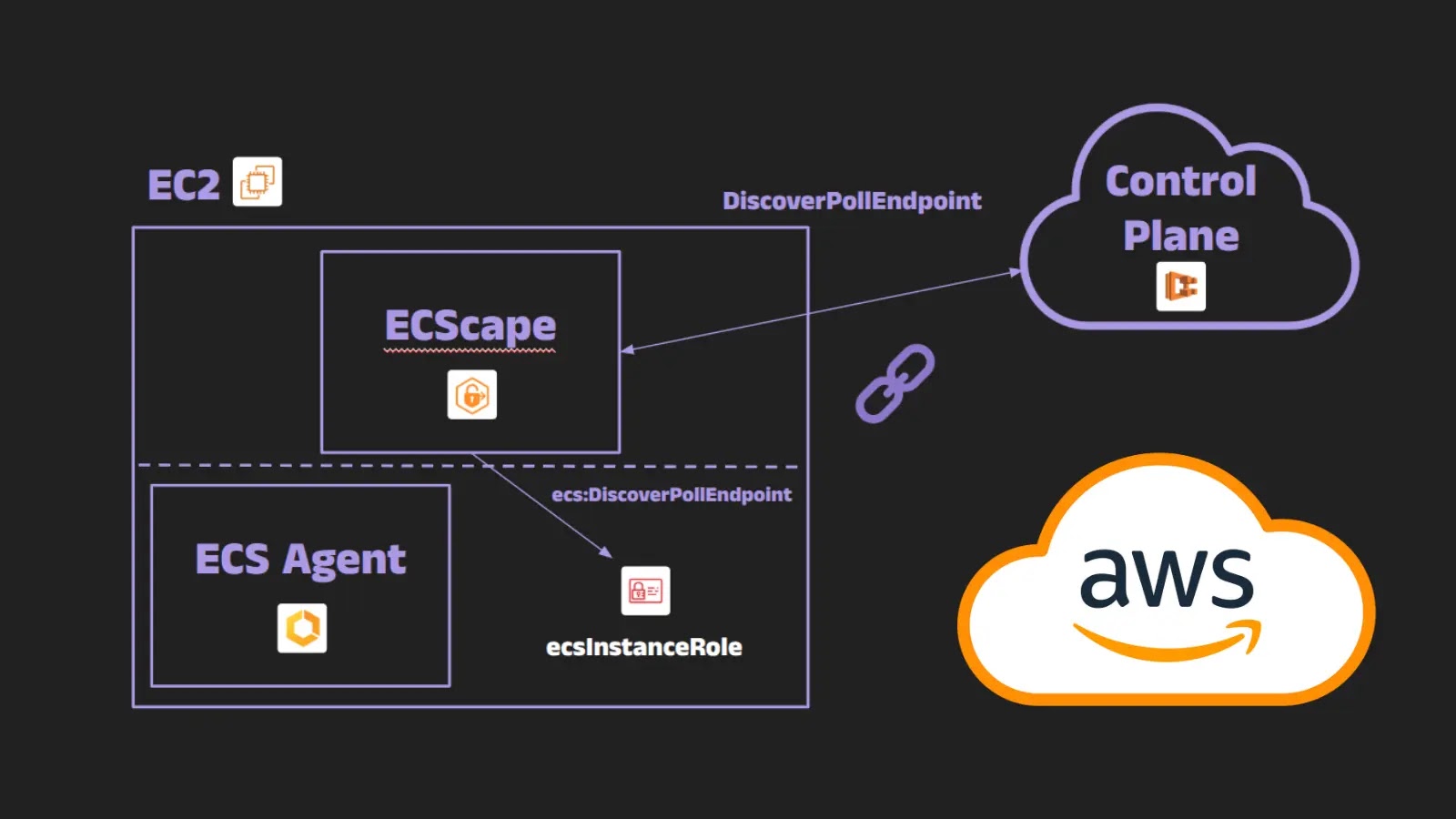
Cloud environments offer unprecedented scalability and flexibility, but they also introduce complex security challenges. A recent discovery, dubbed “ECScape,” highlights a significant vulnerability within [...]
Unveiling ChatGPT-5: A New Era in AI Agent Technology The landscape of artificial intelligence is experiencing a seismic shift with the official release of [...]
Urgent Action Required: CISA Mandates Immediate Patching of Critical Exchange Server Vulnerability (CVE-2025-53786) The cybersecurity landscape is in constant flux, and organizations must remain [...]
The digital landscape is under constant siege, with threat actors continually innovating new methods to bypass defenses. A concerning new trend has emerged: cybercriminals [...]
The long arm of justice often moves slowly, but for sophisticated cybercriminals, it invariably catches up. A recent extradition from France to the United States [...]
In an era where every new cybersecurity headline seems to scream “zero-day,” a recent statement from SonicWall has brought a crucial perspective to light. [...]
Microsoft 365 Direct Send: A New Frontier for Credential Theft Attacks The digital landscape is a constant battleground, and threat actors continuously refine their tactics [...]