the latest from the industry
tech blog for cyber security and tech updates
In an era where cyber threats loom larger than ever, organizations must critically assess their cybersecurity measures to avoid vulnerabilities that could lead to significant breaches. As the digital landscape evolves, networking solutions companies are faced with a multitude of challenges, including conducting comprehensive IT security assessments and implementing advanced threat protection systems. Best practices in cybersecurity are not merely optional; they are essential for safeguarding sensitive data and maintaining operational integrity. From endpoint security solutions provided by industry leaders such as Crowdstrike, SentinelOne, and Sophos, to infrastructure support from companies like Aruba and Ubiquiti, businesses must adopt a proactive approach to ensure their networks remain secure.
To bolster defenses against cyber threats, organizations can leverage a variety of solutions tailored to their specific needs. For instance, utilizing firewall technologies from FortiGate or Checkpoint can create robust barriers against unauthorized access, while tools like TrendMicro and Seqrite offer advanced threat detection capabilities. Additionally, engaging with cybersecurity consulting firms that specialize in risk assessment and remediation can provide invaluable insights into potential vulnerabilities within an organization’s network architecture. With the complexity of today’s digital environments, companies must also consider incorporating enterprise WiFi heatmap analyses to optimize network performance and security, ensuring that every corner of their infrastructure is fortified against intrusion.
Ultimately, the responsibility for cybersecurity lies with each organization. By embracing a culture of vigilance and continually updating security protocols, businesses can significantly enhance their resilience against evolving cyber threats. Utilizing solutions from established names such as SonicWall, D-Link, and CommScope will not only strengthen defenses but also instill confidence in stakeholders about the organization’s commitment to safeguarding its assets. As the stakes rise, investing in cybersecurity measures is no longer a choice but a necessity in today’s interconnected world.
Few events send ripples through the cybersecurity community quite like the seizure of a VPN provider’s servers. It’s a moment that forces us to question [...]
API Security Best Practices: How to Secure APIs and Improve Security Against Cyber Attack In today’s interconnected digital world, APIs (Application Programming Interfaces) have become [...]
A critical alert echoes across the cybersecurity landscape as the U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued a stark warning regarding an actively [...]
F5, a critical player in application delivery networking and security, has recently released its February 2026 Quarterly Security Notification, detailing a series of patched vulnerabilities [...]
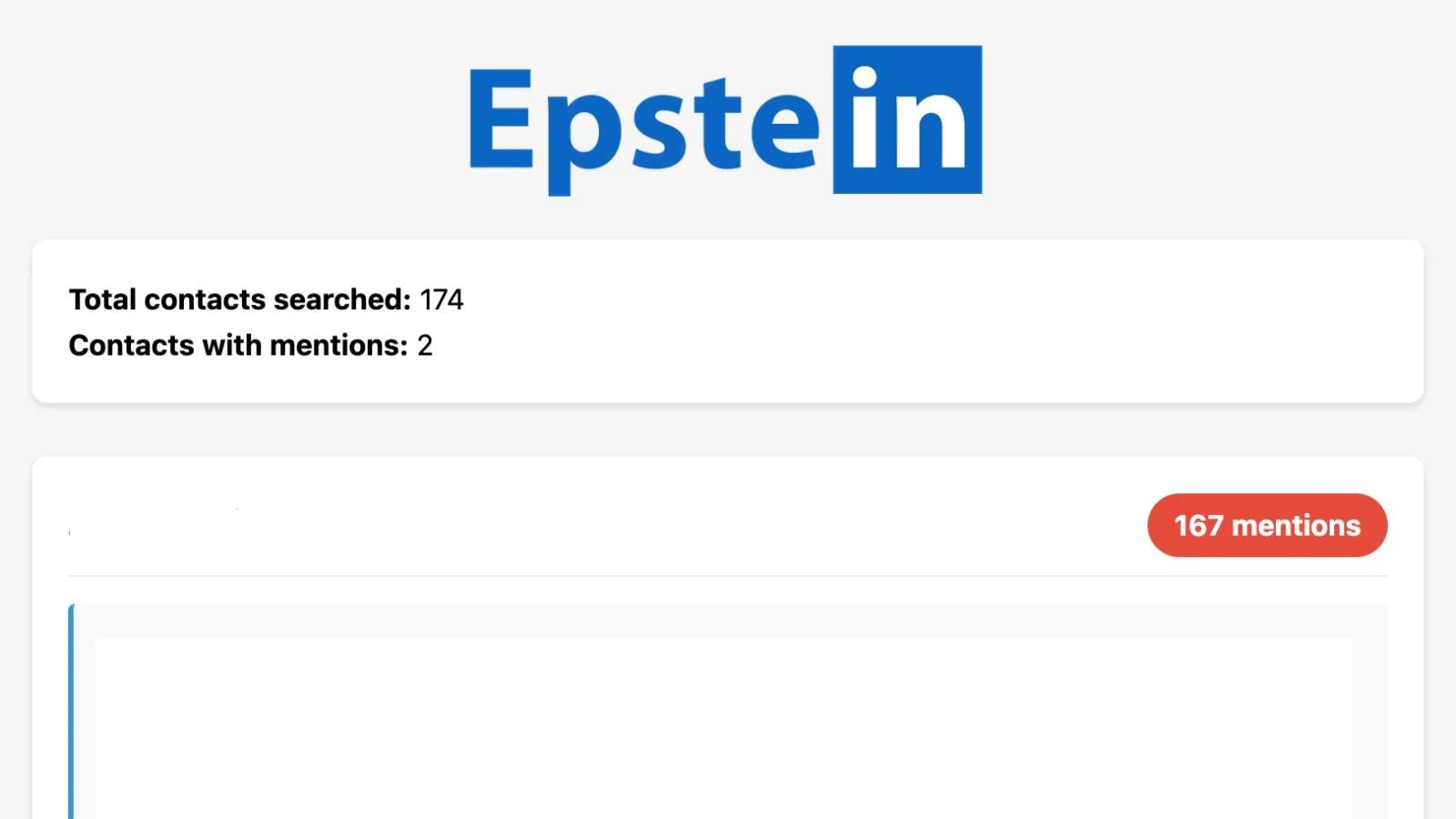
Unveiling Connections: How a New Python Tool Scans LinkedIn Against Epstein Files The recent release of over 3.5 million pages of Jeffrey Epstein court [...]
Urgent Alert: Fake PDF Spam Campaign Installs RMM Tools for Covert Access In a landscape where cyber threats constantly evolve, a new and aggressive spam [...]
Critical Privilege Escalation in WatchGuard VPN Client for Windows A significant security flaw has been uncovered in WatchGuard’s Mobile VPN with IPSec client for [...]
Unmasking the Critical n8n Vulnerability: RCE via Weaponized Workflows The landscape of enterprise automation is constantly evolving, with platforms like n8n empowering organizations to [...]
ShadowSyndicate Evolves: The Server Transition Technique in Ransomware Attacks The cybersecurity landscape demands constant vigilance against evolving threat actor tactics. One such group, ShadowSyndicate, [...]