the latest from the industry
tech blog for cyber security and tech updates
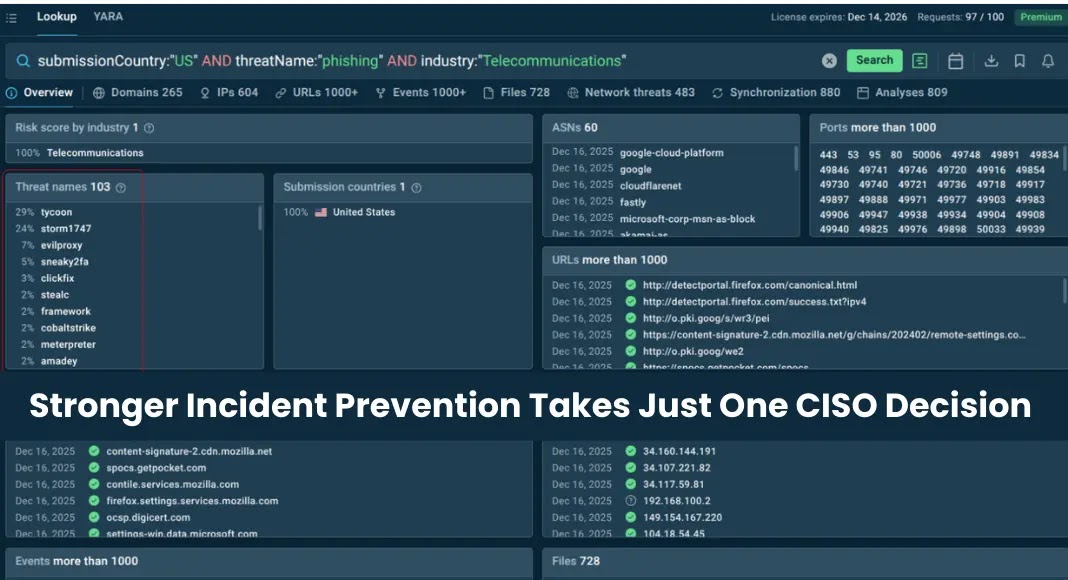
In an era where cyber threats loom larger than ever, organizations must critically assess their cybersecurity measures to avoid vulnerabilities that could lead to significant breaches. As the digital landscape evolves, networking solutions companies are faced with a multitude of challenges, including conducting comprehensive IT security assessments and implementing advanced threat protection systems. Best practices in cybersecurity are not merely optional; they are essential for safeguarding sensitive data and maintaining operational integrity. From endpoint security solutions provided by industry leaders such as Crowdstrike, SentinelOne, and Sophos, to infrastructure support from companies like Aruba and Ubiquiti, businesses must adopt a proactive approach to ensure their networks remain secure.
To bolster defenses against cyber threats, organizations can leverage a variety of solutions tailored to their specific needs. For instance, utilizing firewall technologies from FortiGate or Checkpoint can create robust barriers against unauthorized access, while tools like TrendMicro and Seqrite offer advanced threat detection capabilities. Additionally, engaging with cybersecurity consulting firms that specialize in risk assessment and remediation can provide invaluable insights into potential vulnerabilities within an organization’s network architecture. With the complexity of today’s digital environments, companies must also consider incorporating enterprise WiFi heatmap analyses to optimize network performance and security, ensuring that every corner of their infrastructure is fortified against intrusion.
Ultimately, the responsibility for cybersecurity lies with each organization. By embracing a culture of vigilance and continually updating security protocols, businesses can significantly enhance their resilience against evolving cyber threats. Utilizing solutions from established names such as SonicWall, D-Link, and CommScope will not only strengthen defenses but also instill confidence in stakeholders about the organization’s commitment to safeguarding its assets. As the stakes rise, investing in cybersecurity measures is no longer a choice but a necessity in today’s interconnected world.
In the evolving landscape of cyber threats, a new sophisticated phishing campaign has emerged, specifically targeting macOS users. This campaign leverages meticulously crafted fake [...]
Unpacking the Latest PDFly Variant: A Deep Dive into Custom PyInstaller Obfuscation The cybersecurity landscape is a relentless battleground, and threat actors are continuously [...]
In the complex theater of cybersecurity, a persistent and often misleading narrative suggests that when the digital battleground gets noisy, the immediate solution is [...]
A disturbing trend has emerged in the cybersecurity landscape: threat actors are actively leveraging a critical remote code execution (RCE) vulnerability within React Native’s Metro [...]
The ubiquity of PDF documents in professional and personal workflows makes the tools we use to interact with them critical components of our digital security [...]
Mac Under Threat: Infostealers Leverage Python and Trusted Platforms The digital threat landscape is in constant flux, and a concerning trend has emerged: infostealer [...]
The Deceptive Lure of Fake Dropbox: Unpacking a Multi-Stage Phishing Attack The digital landscape is a constant battleground, and cybercriminals are relentlessly innovating. A [...]
The digital supply chain is a bedrock of modern software development, yet it remains a critical attack vector for malicious actors. A recent and [...]
The digital landscape is a constant battleground, and even the most innovative technologies can become targets. Just two months after its disclosure, a critical [...]