The Ultimate SaaS Security Admin Guide – 2024 Software as a Service (SaaS), which provides flexible, available, and cost-effective software solutions, has changed how businesses [...]
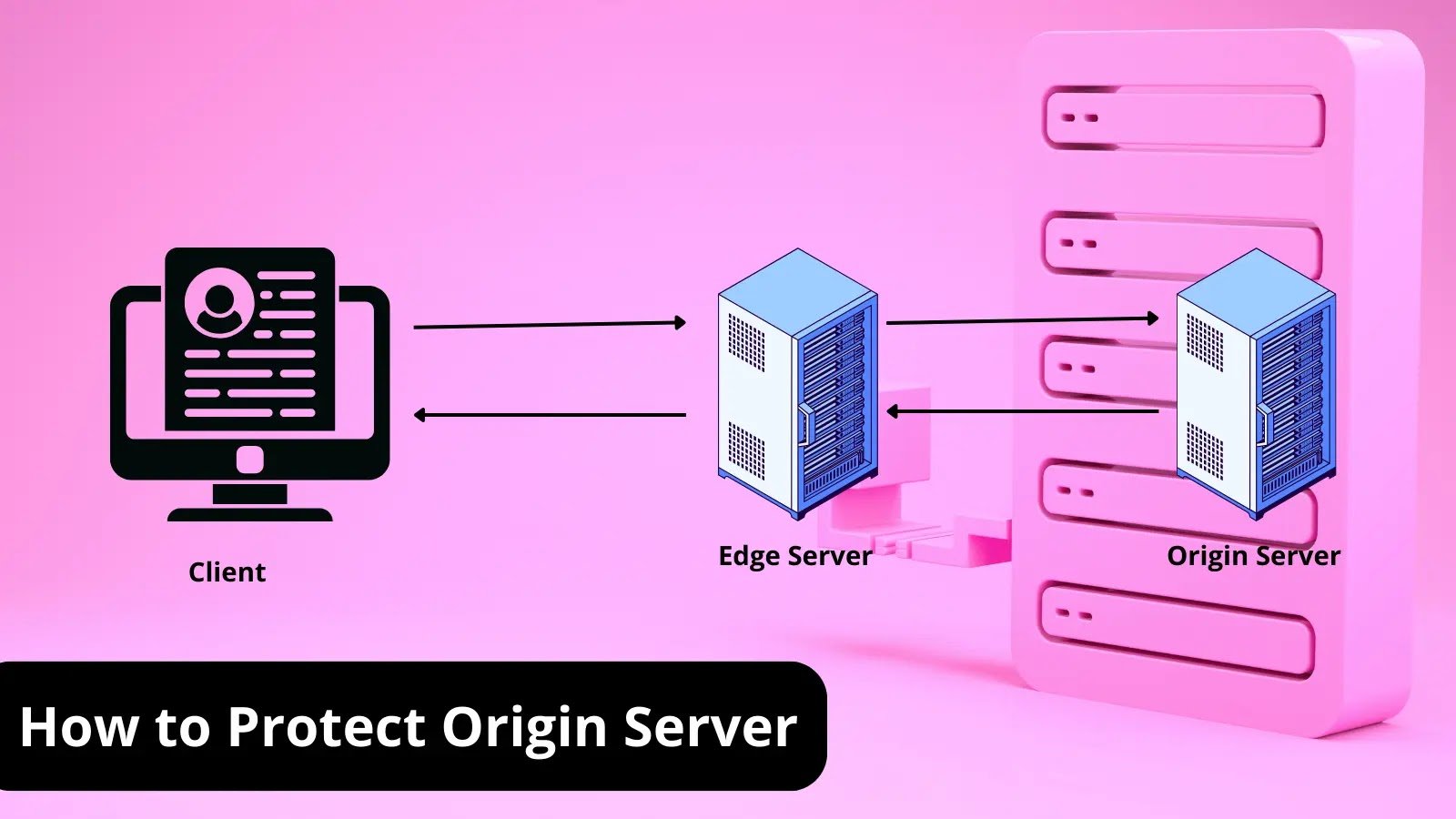
What is Origin Server? How To Protect it? A Detailed Guide The origin server stores a website’s or application’s content and data. As the starting [...]
Best Network Security Companies for CISOs Features. Network security vendors offer a variety of products and services to prevent harm to an organization’s computer networks, [...]
8-Point Security Checklist For Your Storage & Backups – 2024. On September 27th, Johnson Controls International announced a massive ransomware attack, that encrypted many of the [...]
5 New Zero-day Vulnerabilities Patched in the Microsoft Security Update Microsoft has released their security patches as part of their Patch Tuesday for November 2023. [...]
Fortinet Secure SD-WAN: The Fortinet Secure SD-WAN solution provides all these and more, protecting your investment along your digital-first journey by scaling and adapting to [...]
Ransomware Roundup – No Escape NoEscape is a financially motivated ransomware group that emerged in May 2023. The group runs a Ransomware-as-a-Service program. The developer [...]
Large Provincial Ministry Chooses Fortinet Secure SD-WAN: In regional or provincial government, the office of the chief of staff, or head ministry, provides a broad [...]
8 New Metasploit Exploit Modules Released Targeting Critical Vulnerabilities Metasploit is an open-source penetration testing framework created by Rapid7 that enables security professionals to simulate [...]
Threat Predictions for 2024: Chained AI and CaaS (Cybercrime – as – a – Service) Operations Give Attackers More “Easy” Buttons Than Ever: With the [...]