The Art of Cable Management: How to Organize Your Cabling Chaos Cable management is a crucial aspect of maintaining a clean and organized workspace. [...]
The Future of Wireless Security: Quantum Cryptography Quantum cryptography is a cutting-edge field that holds promise for revolutionizing wireless security. Unlike traditional cryptographic methods, which [...]
Top 3 Cybersecurity Trends for SME Business Leaders in 2024 As Cynet’s COO, my team and I get to work closely with risk management executives [...]
Hackers using Weaponized Office Document to Exploit Windows Search RCE A new attack chain campaign has been discovered, which involves the exploitation of CVE-2023-36884 and [...]
5 Benefits of XDR for Cybersecurity Cybersecurity requires staying one step ahead. A main force of digital protection is eXtended Detection and Response (XDR). This [...]
Endpoint Management And Security : Key To Handling And Securing Future IT Operations Endpoint management and security is not one of the top areas of discussion [...]
Securing Your Digital World: The Latest in Cybersecurity Innovations The importance of robust cybersecurity measures cannot be overstated in the digital age. As technology advances, [...]
Reflectiz Introduces AI-powered Insights on Top of Its Smart Alerting System Reflectiz, a cybersecurity company specializing in continuous web threat management, proudly introduces a new [...]
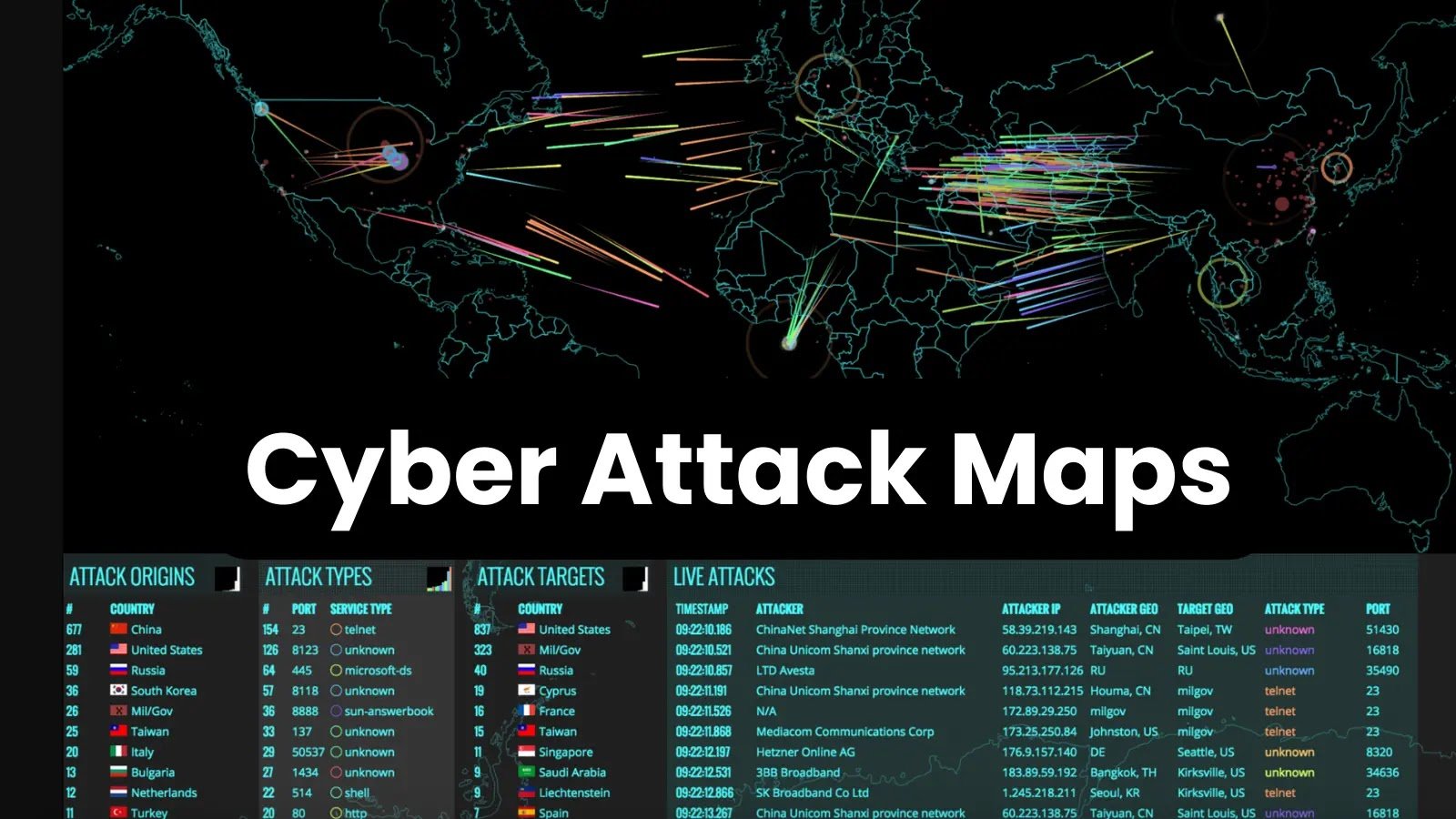
Top 10 Cyber Attack Maps to See Digital Threats In 2024 Cyber attack maps are visual representations or interactive tools that provide real-time or historical [...]
What is SSL and Why it is Important? The protocols SSL (Secure Sockets Layer) and TLS (Transport Layer Security), are used to create secure connections [...]