10 Best Firewall as a Service (FWaaS) Providers – 2024 Firewall as a Service (FWaaS) is an emerging security model in cloud computing and network [...]
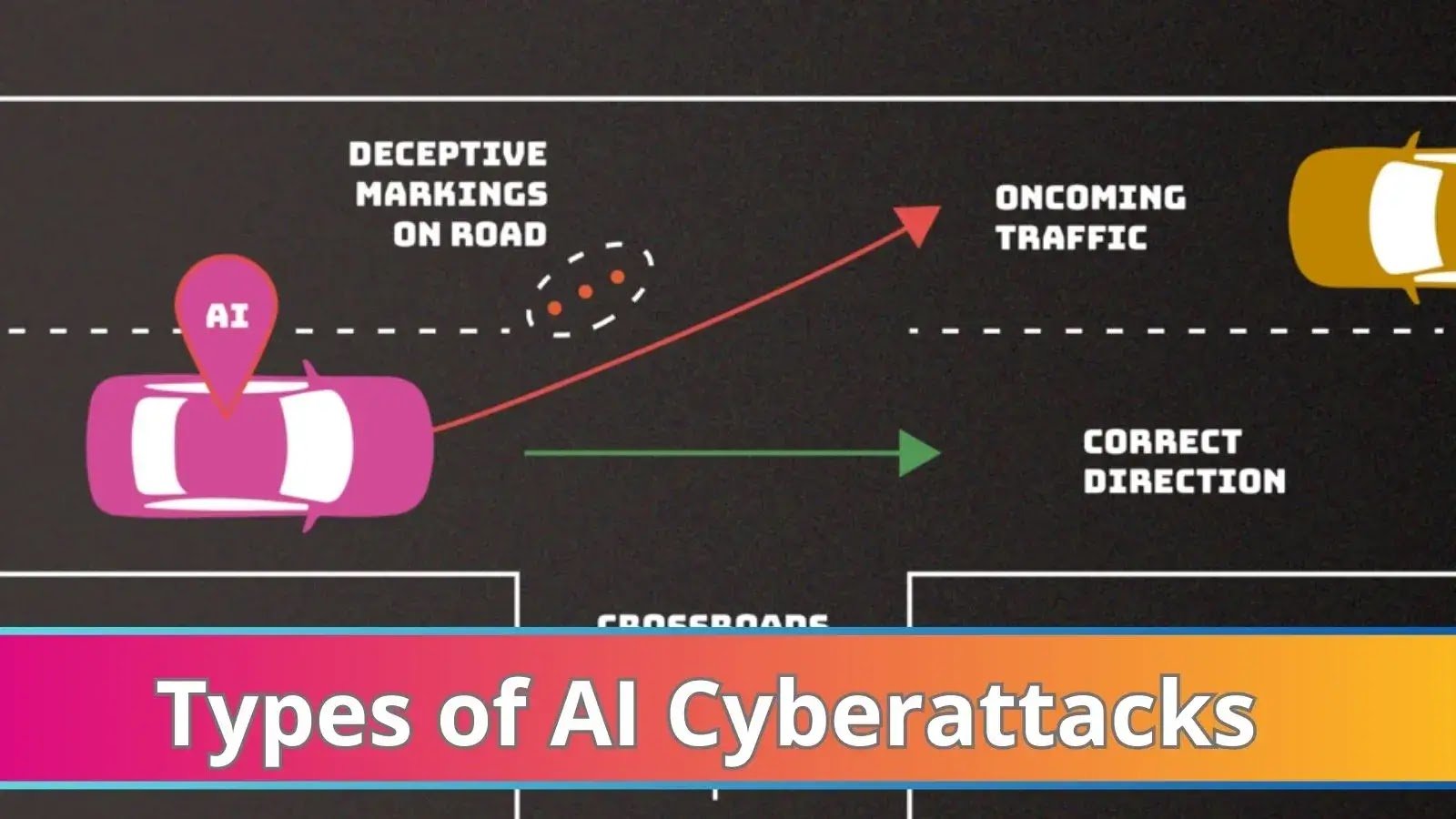
NIST Details Types of Cyberattacks that Leads to Malfunction of AI Systems Artificial intelligence (AI) systems can be purposefully tricked or even “poisoned” by attackers, [...]
Network Security Checklist – Complete Guide To Protect Enterprise Networks (2024) Network security is paramount in today’s digital landscape, where organizations face increasingly sophisticated threats. [...]
Hackers Employ New Evasion Mechanisms to Bypass Security Solutions The digital landscape, once a serene meadow, has morphed into a battleground where attackers and security [...]
Wi-Fi Alliance Announces Wi-Fi 7 to Boost performance Wi-Fi Alliance unleashes the next generation of connectivity with Wi-Fi CERTIFIED 7™. This revolutionary technology promises to [...]
Sea Turtle APT Group Exploiting Known Vulnerabilities to Attack IT-service Providers To obtain access to a variety of clients’ systems and data in a single [...]
The Future of IoT Gateways: Bridging Devices for Seamless Connectivity The future of IoT gateways holds significant promise as these devices play a crucial role [...]
SonicWall Acquires Banyan Security for Security Service Edge (SSE) Solutions SonicWall has made a strategic move in the evolving cybersecurity landscape, acquiring Banyan Security, a [...]
The Rise of Zero Trust Architecture in SaaS Security Zero Trust Architecture (ZTA) has gained significant traction in the realm of SaaS (Software as a [...]
Unveiling the Myths and Truths about Cloud-Based CCTV Surveillance Cloud-based CCTV surveillance has gained popularity due to its flexibility, scalability, and accessibility. However, like any [...]