CCTV as a Service: Outsourcing Your Surveillance Needs “CCTV as a Service” (CCTVaaS) refers to the outsourcing of surveillance needs to third-party providers who offer [...]
10 Best Network Security Solutions for IT Managers Network security solutions employ a variety of techniques to prevent attacks targeting networks. To filter incoming and [...]
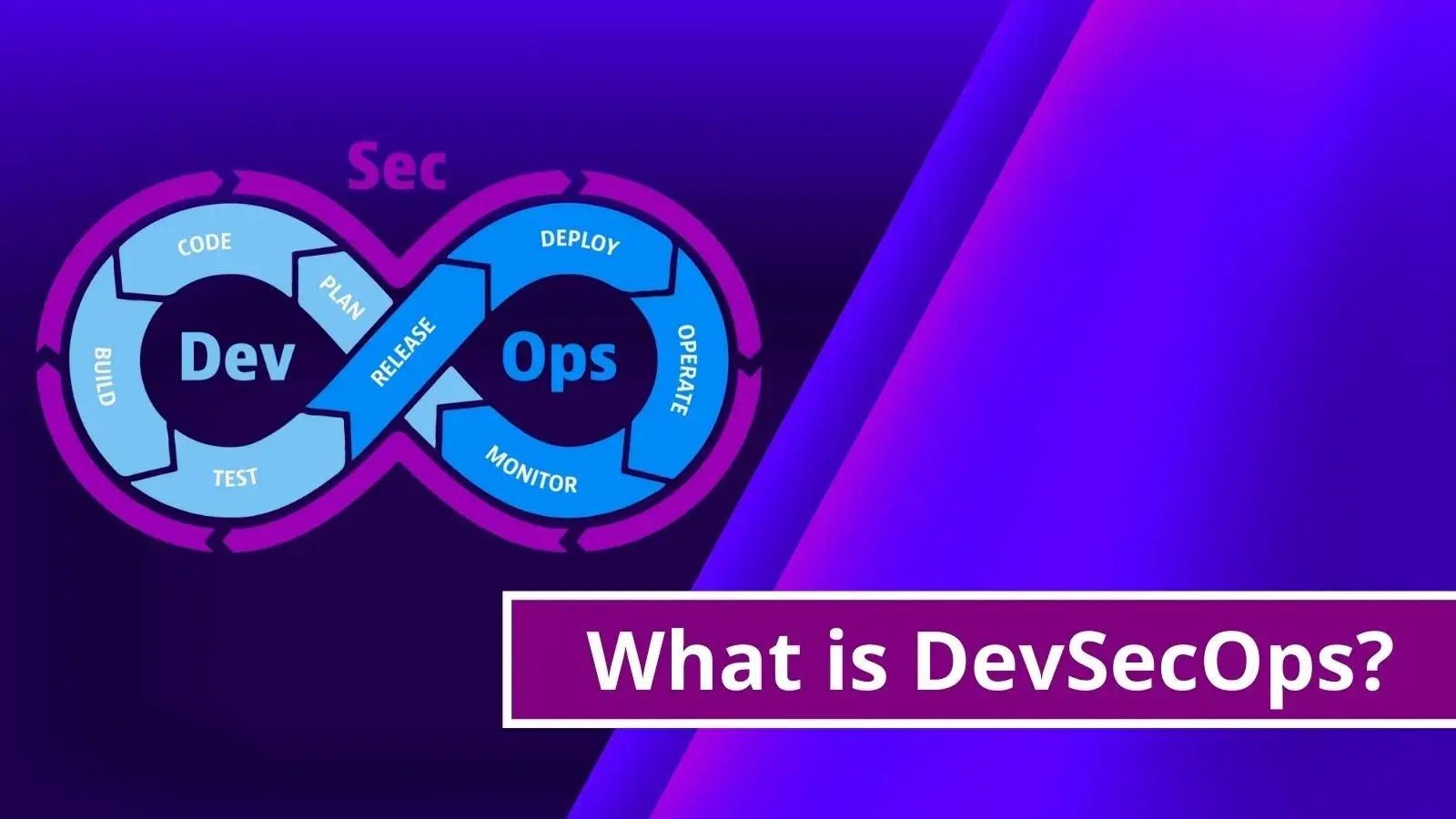
What is DevSecOps? Benefits of Automated DevOps Security DevSecOps is a methodology that integrates security as a shared responsibility throughout the entirety of the information [...]
What is Malware? Removal and Prevention Malware, which is an abbreviation for “malicious software,” is any software that is purposefully designed to do damage to [...]
Exploring the Latest Trends in Firewall Technology Firewalls remain a critical component of network security, acting as the first line of defense against cyber threats. [...]
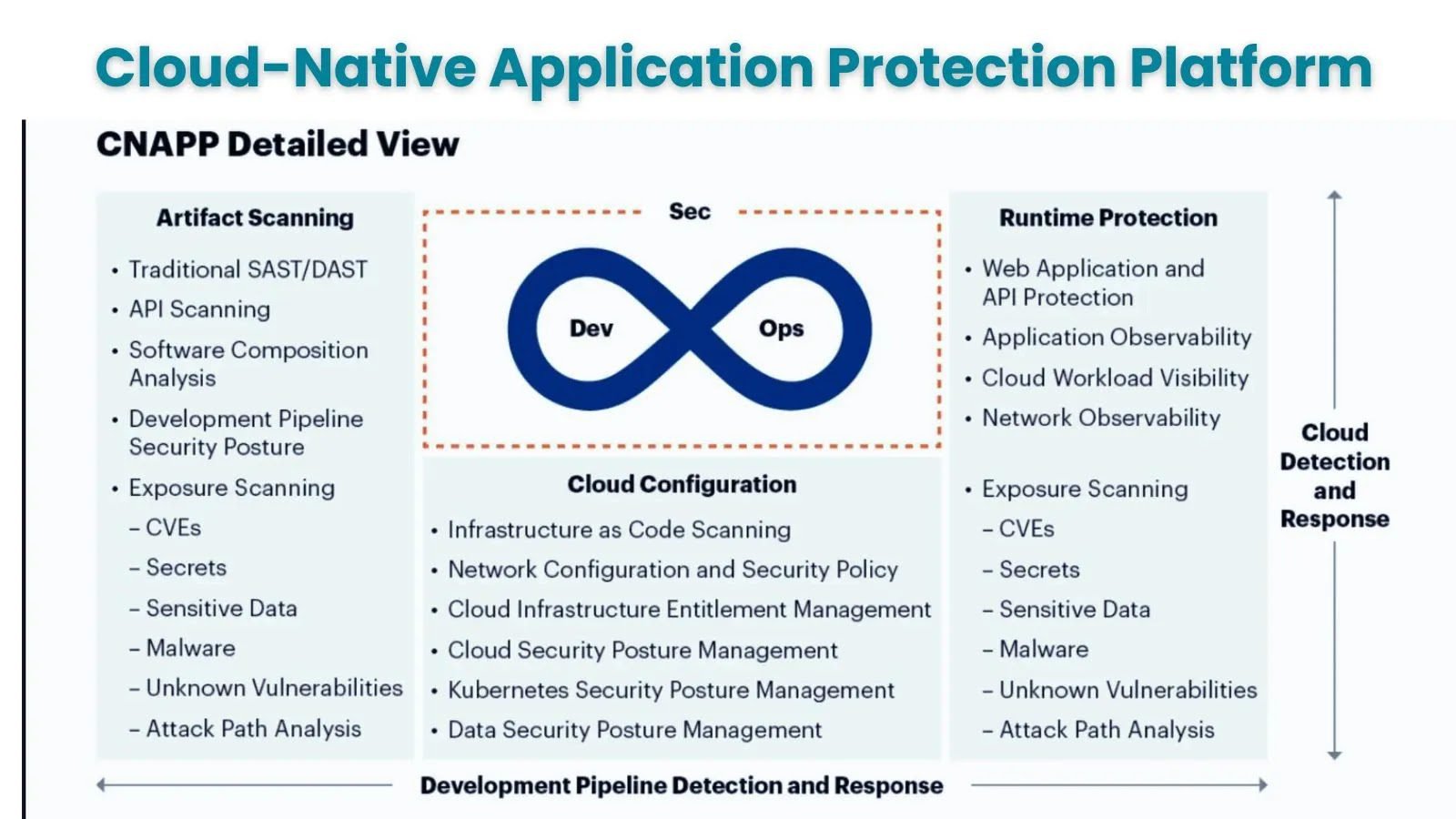
What is CNAPP ? How It Benefits for Multi-Cloud & Hybrid Infrastructure Protection Multi-cloud and hybrid infrastructures are becoming the norm among enterprises nowadays. Around [...]
NSA Releases Top 10 Cloud Security Mitigation Strategies NSA and CISA jointly released “Top 10 Cloud Security Mitigation Strategies” to advise cloud users on critical [...]
Empower Your Security and IT with Microsoft Copilot: The Ultimate AI Tool Microsoft Security Copilot, a generative AI solution for security professionals, will be generally [...]
What is Linux Firewall? How to Enable Packet Filtering With Open Source Iptables Firewall? One of the most important security tools for Linux is the [...]
Cloud-Based Firewall for Today and The Future In the age of cloud computing, where data and other mission-critical assets are accessed over the Internet, it’s [...]