The relentless churn of security alerts has become a modern-day Sisyphean plight for Security Operations Centers (SOCs). As digital footprints expand and threat actors [...]
A disturbing trend has emerged from the ever-present shadow of cyber warfare: a sophisticated zero-day attack targeting Microsoft SharePoint Server installations. This isn’t a [...]
Navigating Treacherous Waters: APT Ransomware Strikes the Maritime Industry The global maritime industry, the silent engine behind approximately 90% of international trade, is increasingly [...]
Unpacking the Critical OAuth2-Proxy Authentication Bypass (CVE-2025-54576) The digital landscape demands robust authentication, especially when leveraging reverse proxies for identity management. A recent critical [...]
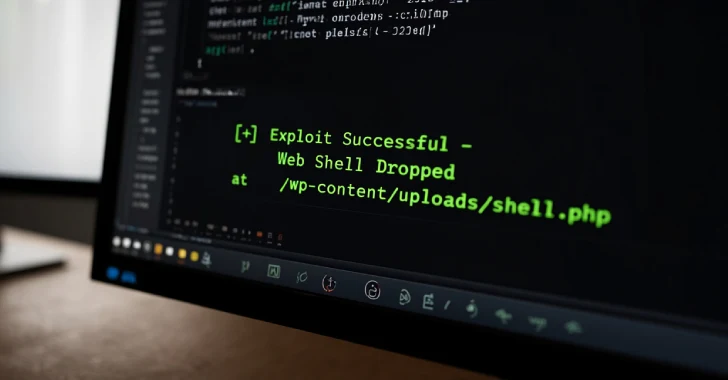
Urgent Warning: Critical WordPress Theme Flaw Exploited by Hackers The digital landscape is under constant assault, and a new threat has emerged, targeting a [...]
The Alarming Rise of Qilin Ransomware: Weaponizing Obscure Drivers to Cripple EDR Endpoint Detection and Response (EDR) systems are the bedrock of modern cybersecurity [...]
The cryptocurrency landscape, while offering unparalleled opportunities, remains a prime target for sophisticated cybercriminals. A new, stealthy threat has emerged on the horizon, specifically [...]
Unmasking Scattered Spider: CISA and FBI Detail Evolving Ransomware Tactics The digital landscape is a constant battlefield, and staying ahead of sophisticated threat actors [...]
Victims Rejoice: Free Decryptor Released for AI-Assisted FunkSec Ransomware The digital battlefield is constantly shifting, with threat actors leveraging cutting-edge technologies to amplify their [...]
In the relentless battle against cybercrime, one often overlooked but critically important player is the infrastructure provider. When these providers knowingly or unknowingly facilitate malicious [...]