The Passwordless Future of Authentication: Passwordless Authentication Login & Beyond Password In an era where cyber threats are increasingly sophisticated, the future of authentication is [...]
In the rapidly evolving landscape of digital experiences, augmented reality (AR) and virtual reality (VR) stand out as transformative technologies reshaping how we interact with [...]
IoT Security at the Edge Computing: Securing Industrial IoT Edge Devices In the rapidly evolving landscape of the Industrial Internet of Things (IIoT), securing IoT [...]
Using AI and Machine Learning for Insider Threat Detection In a world where cybersecurity challenges are ever-evolving, the role of AI and machine learning in [...]
The Role of Blockchain in Cybersecurity: Enhancing Data Security Cyber Defense In the modern digital era, the role of blockchain in cybersecurity is garnering significant [...]
The Silent Attack: How a Punycode Vulnerability Hijacks Your Email The digital identities we rely on daily, from social media to critical banking, are [...]
Unmasking MeetC2: The Covert Google Calendar C2 Framework The cybersecurity landscape is in a constant state of flux, with threat actors consistently evolving their [...]
Urgent Alert: CISA Warns of Android Zero-Day Under Active Exploitation The digital landscape is under constant siege, and a new, critical threat has emerged directly [...]
Urgent Warning: Critical SAP S/4HANA Vulnerability Under Active Attack Organizations worldwide relying on SAP S/4HANA are facing an immediate and severe cybersecurity threat. A [...]
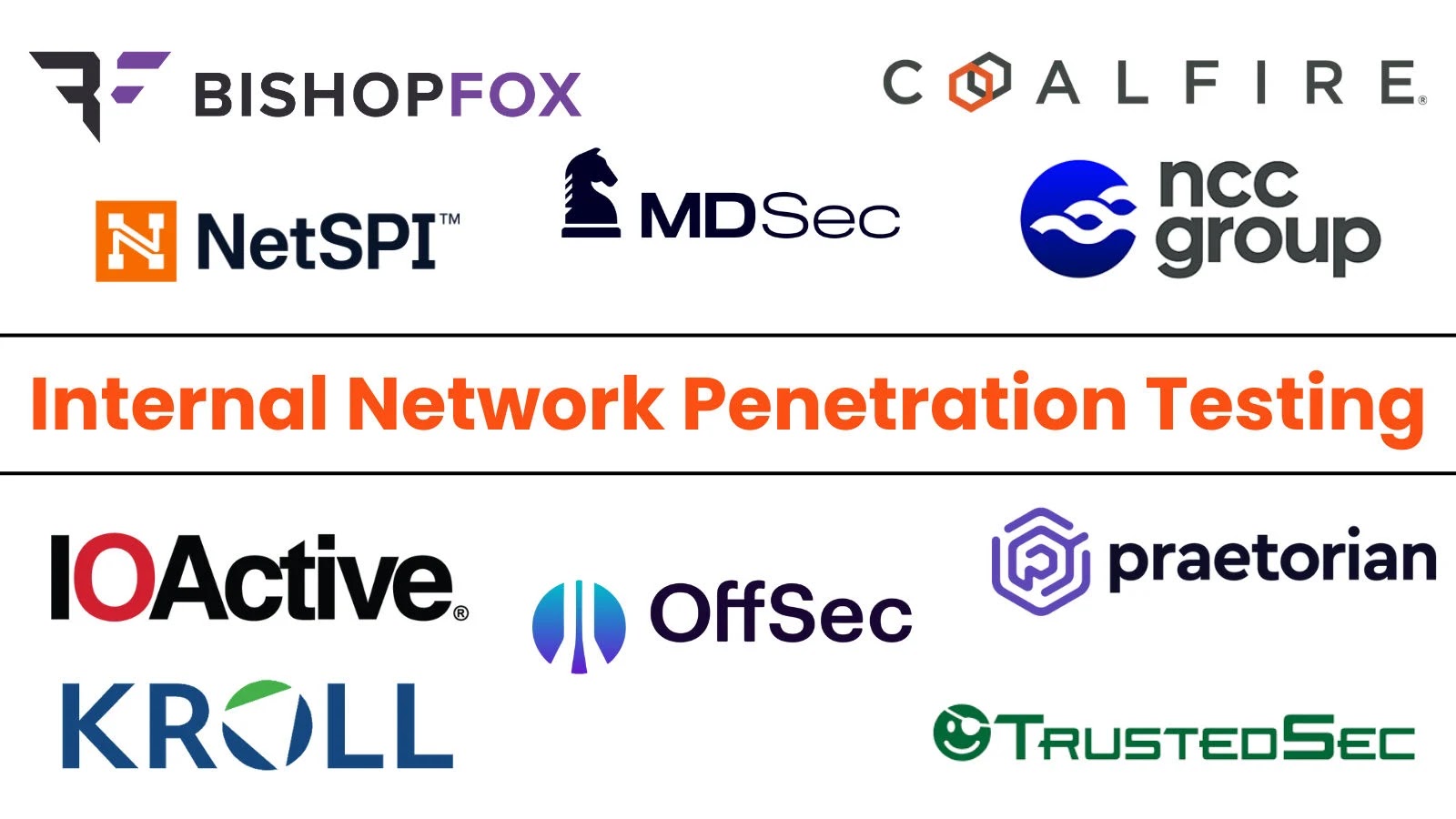
Why Internal Network Penetration Testing is Non-Negotiable in 2025 Organizations often prioritize hardening their external perimeter, investing heavily in firewalls, intrusion detection systems, and [...]