Recent events have once again cast a stark light on the pervasive threat of cyberattacks targeting critical industrial infrastructure. When a global manufacturing behemoth like [...]
The digital threat landscape is constantly evolving, with cybercriminals deploying increasingly sophisticated tactics to bypass security defenses. One of the most insidious threats involves advanced [...]
Urgent Threat: Unprecedented Scanning for Cisco ASA Vulnerabilities by 25,000+ IPs The cybersecurity landscape is constantly shifting, but some threats emerge with an alarming [...]
Immediate Alert: Chrome 140 Patches Six Vulnerabilities, Including Critical Remote Code Execution Flaw Browser security is paramount. Every new vulnerability presents a potential gateway for [...]
Urgent Android Security Update: Patching Actively Exploited 0-Day Vulnerabilities The digital landscape is a constant battlefield, and the latest skirmish highlights the critical importance [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in Drupal modules Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software Affected Drupal Authenticator [...]
A significant cybersecurity alert has been issued for organizations utilizing Microsoft’s Internet Information Services (IIS), particularly those employing the Web Deploy (msdeploy) tool. A [...]
The quiet hum of our digital lives was recently disrupted by a stark warning from the Cybersecurity and Infrastructure Security Agency (CISA). A critical [...]
The digital landscape is under perpetual siege, with new threats constantly emerging to challenge enterprise security. A recent, particularly insidious addition to this threatscape is [...]
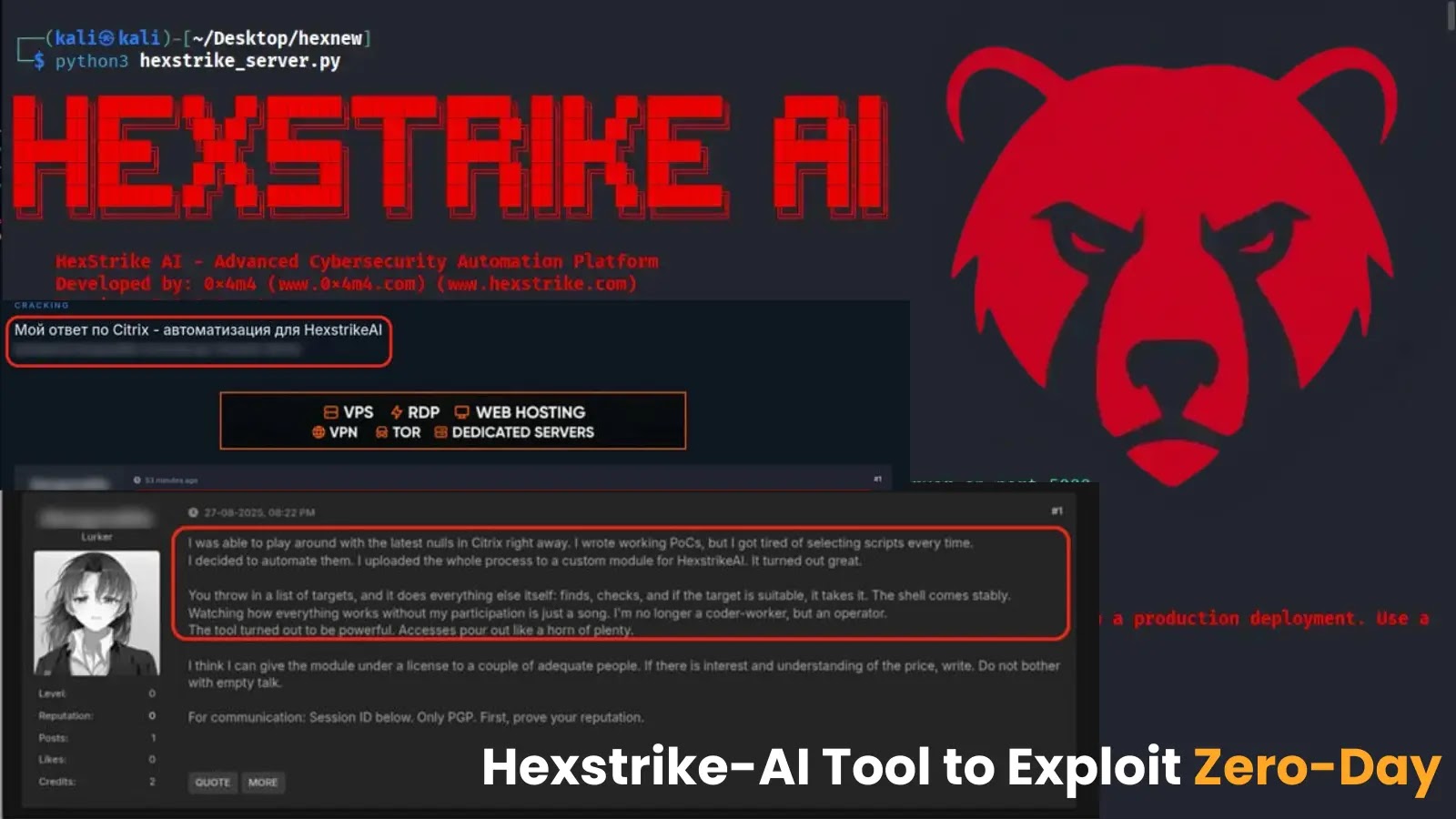
The cybersecurity landscape has just been fundamentally reshaped. Threat actors are now leveraging an advanced AI tool, Hexstrike-AI, to identify and exploit zero-day vulnerabilities [...]