KawaiiGPT: The Alarming Rise of a New Black-Hat AI Tool The cybersecurity landscape has been fundamentally reshaped by advancements in artificial intelligence. While AI [...]
A Dangerous Confluence: Russian and North Korean Hackers Forge Alliances The landscape of cyber warfare is in constant flux, but few shifts are as [...]
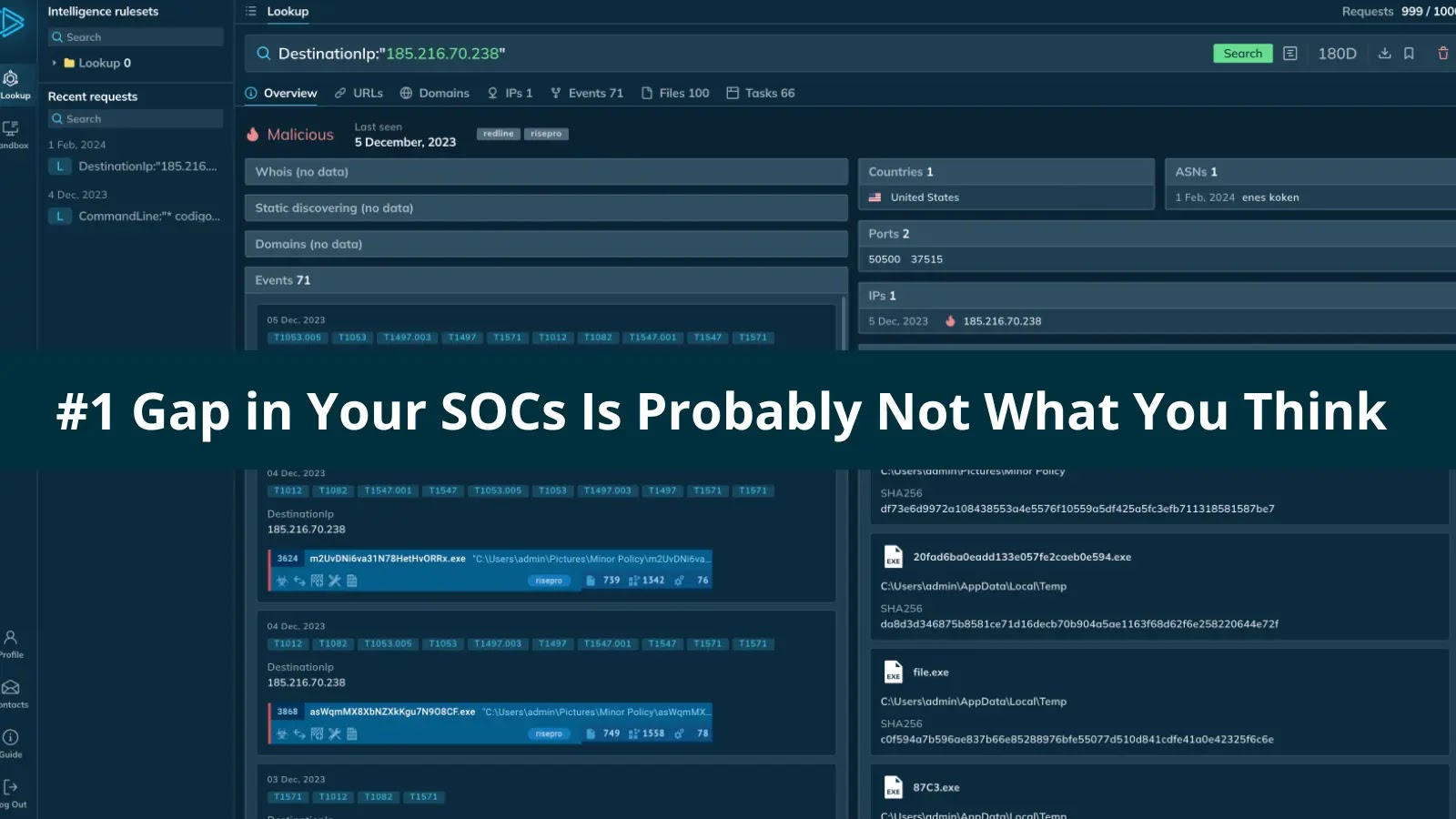
The Unseen Foe: Why Your SOC’s Biggest Weakness Isn’t What You Expect Leading a Security Operations Center (SOC) often feels like an unending struggle [...]
SitusAMC Data Breach: A Deep Dive into the Compromise of Financial Records and Legal Agreements The digital landscape for financial services is fraught with [...]
Another day, another grim reminder of the persistent threats lurking within our digital lives. Delta Dental of Virginia, a non-profit dental insurance provider, recently [...]
In the dynamic realm of cybersecurity, staying ahead of sophisticated threats requires continuous innovation in both defensive and offensive strategies. Penetration testers and red teams [...]
Identity and Access Management (IAM) systems are the linchpin of modern security, controlling who can access what resources within an organization. When vulnerabilities emerge [...]
The landscape of cyber threats has fundamentally shifted. Traditional defenses, reliant on signature-based detection and file-centric analysis, are increasingly outmatched by sophisticated adversaries employing fileless [...]
Securing Smart Cities: Internet of Things (IoT) And Infrastructure Challenges in Smart Cities Smart cities represent a significant evolution in urban planning and management, leveraging [...]
Cyber in JLR Cyber attack: Automotive Manufacturing Cybersecurity Lessons from Learned Jaguar Land Rover In an era where the automotive sector increasingly relies on digital [...]