—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Remote Code Execution vulnerability in Unstructured.io Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: CRITICAL Software Affected Unstructured-IO [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Remote Code Execution Vulnerability in Microsoft Edge (Chromium-based) Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in GitLab Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software Affected Gitlab versions prior [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Use after free vulnerability in Google Chrome for Desktop Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH [...]
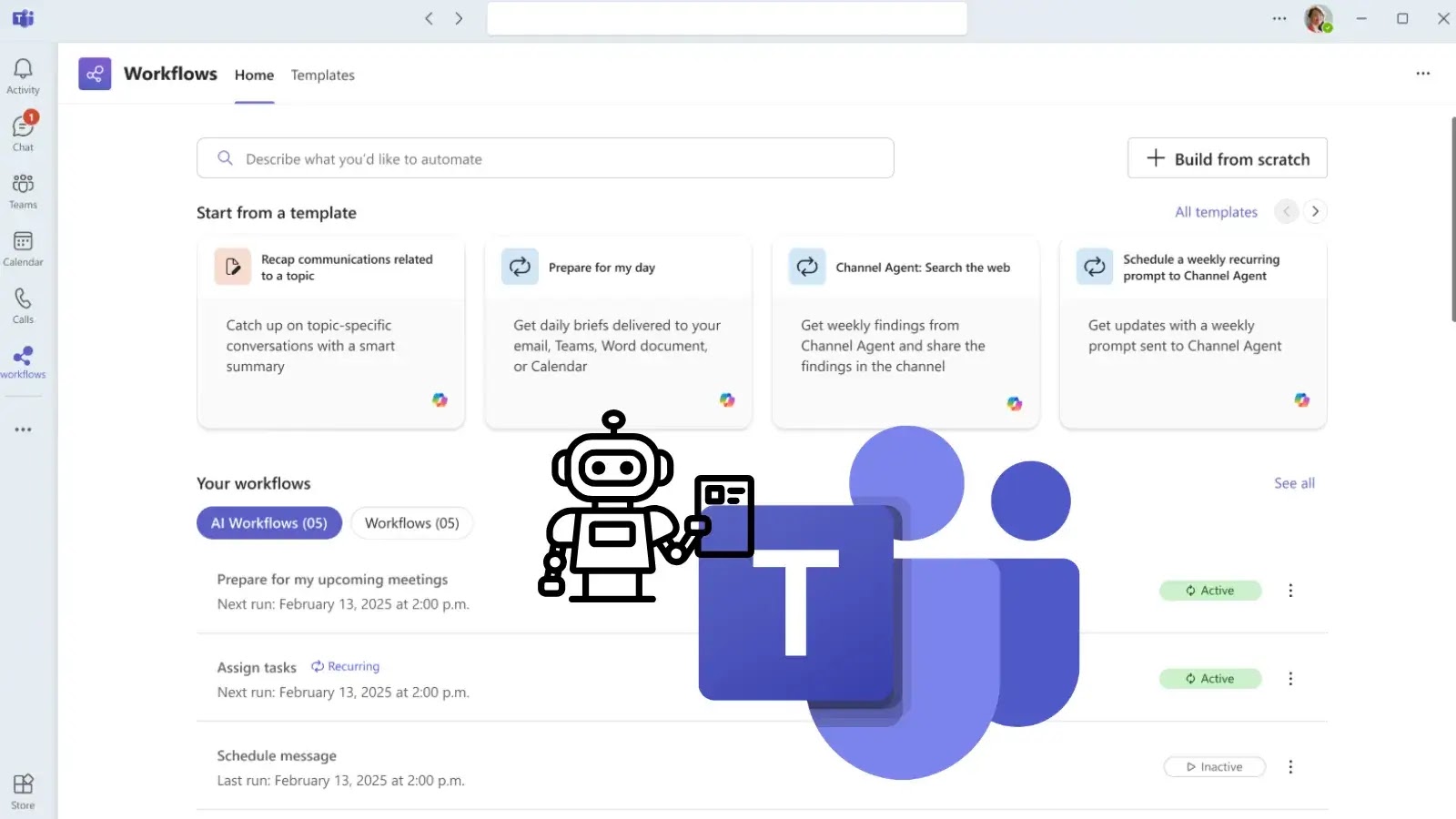
The relentless pace of modern business demands efficiency. Manual, repetitive tasks often consume valuable time and resources, hindering productivity and innovation. Recognising this challenge, Microsoft [...]
Rogue DHCP Server Protection: DHCP Snooping Preventing on Networks In the realm of network security, safeguarding against unauthorized access and malicious activities is paramount. DHCP [...]
Cybersecurity: The Role of Blockchain Technologies in Enhancing Cybersecurity In today’s digital landscape, cybersecurity threats are ever-evolving and increasingly sophisticated. Traditional security measures often struggle [...]
The Pernicious Reach of Keenadu: When Firmware Becomes a Foothold for Remote Control Imagine a smartphone or tablet that, from the moment it’s powered [...]
Navigating the NiFi Nuisance: Unpacking CVE-2026-25903 Authorization Bypass The integrity of data workflows relies heavily on robust authorization. When a critical data orchestration platform [...]
Unmasking the Langchain Community SSRF Bypass: A Gateway to Internal Exploits In the complex landscape of modern applications, Server-Side Request Forgery (SSRF) vulnerabilities continue [...]