Imagine a scenario where a seemingly innocuous Google Calendar invitation morphs into a sophisticated weapon, silently transforming your personal AI assistant into a covert [...]
Palo Alto Networks Firewall Vulnerability Triggers Critical Reboot Loop The stability of enterprise networks hinges on the unwavering performance of their security infrastructure. A recent [...]
What is DNS Security? Understand DNS cache poisoning, DNS hijacking, DNS tunneling and DNS amplification attacks In today’s digital landscape, where cyber threats are increasingly [...]
What is a Cyber Kill Chain Explained: Kill Chains, Definition, & Uses In the realm of cybersecurity, the cyber kill chain stands as a vital [...]
The Shifting Sands of Cybercrime: Legitimate Tools, Malicious Intent In the evolving landscape of cyber threats, adversaries are constantly refining their tactics. We traditionally [...]
GitGuardian Secures $50M to Combat the Non-Human Identity Crisis and AI Agent Security Gap The digital landscape is increasingly defined by automation, with non-human [...]
For IT professionals, security analysts, and developers, the emergence of a zero-day vulnerability in widely used software is always a critical concern. When that software [...]
A silent threat often lurks behind the most trusted components of our operating systems. Recently, Microsoft released an urgent security patch addressing just such [...]
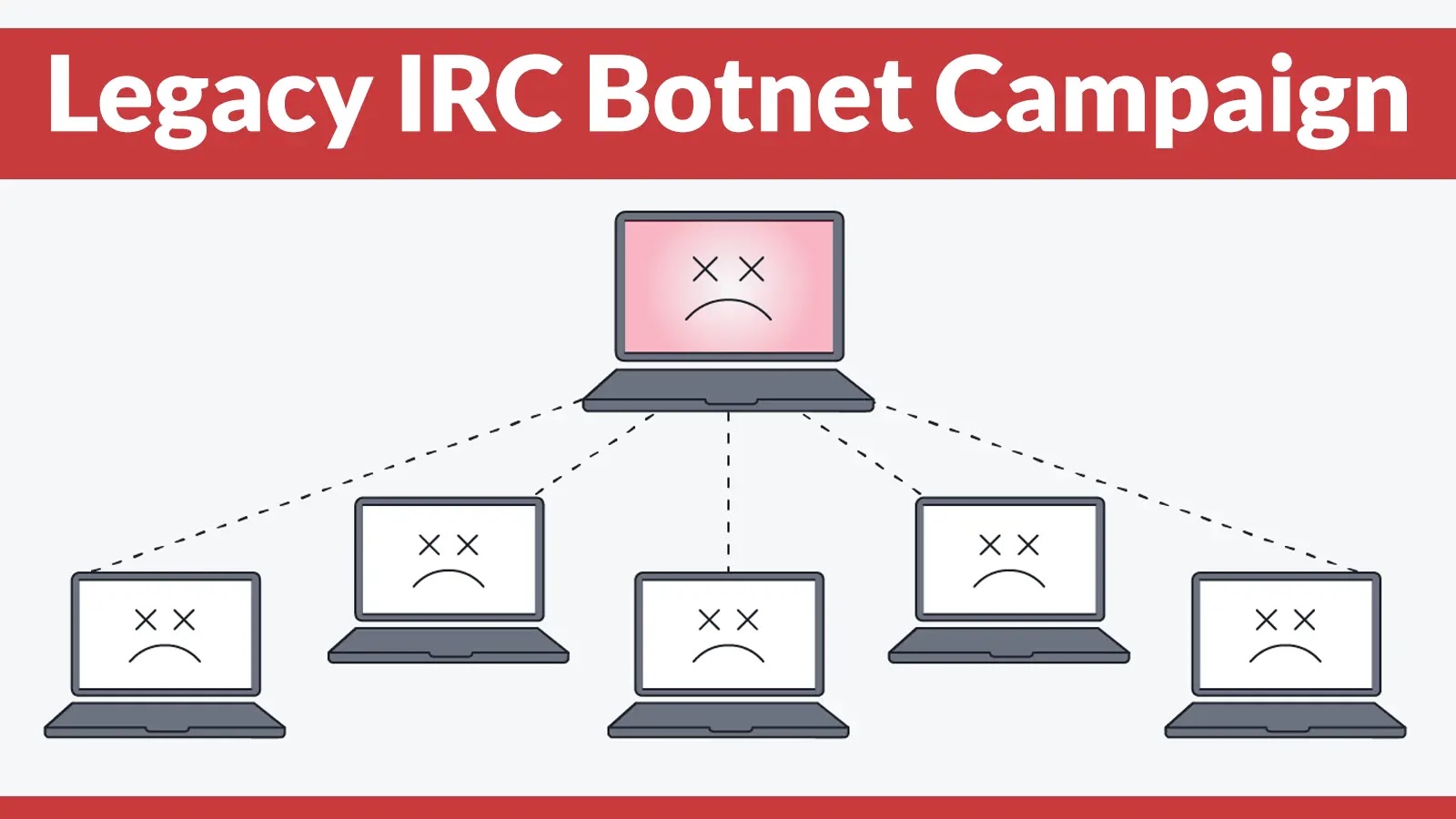
The silent hum of servers, the backbone of modern enterprise, often conceals a sinister undercurrent. In the ever-evolving landscape of cyber threats, a legacy attack [...]
The digital landscape is a constant battleground, and even the most seemingly innocuous components can harbor critical weaknesses. A recent discovery has sent ripples through [...]