ScarCruft’s Evolving Threat: Shifting Tactics and Cloud Abuse The digital threat landscape is in a constant state of flux, with sophisticated APT groups consistently refining [...]
Privacy is a fundamental expectation in digital communication, especially when it comes to email. Users rely on built-in features to protect their inbox from unwanted [...]
The digital perimeter of organizations is under unprecedented assault. Advanced Persistent Threat (APT) groups, once focused on breaching conventional endpoints, are now demonstrating a [...]
The Evolving Threat Landscape: How Hackers Leverage ClawHub Skills to Bypass VirusTotal Cybersecurity professionals face a constant uphill battle against increasingly sophisticated adversaries. A [...]
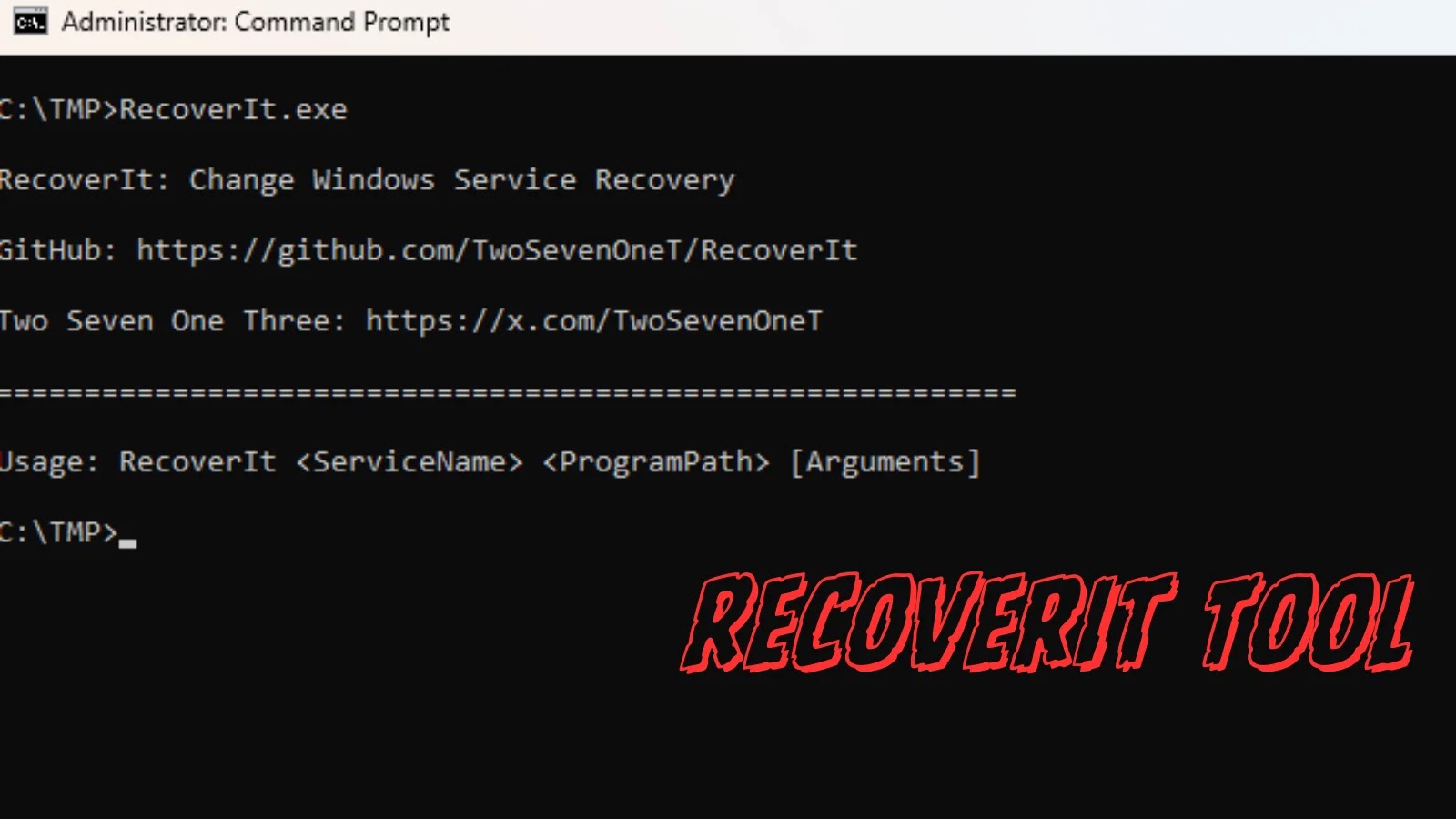
Unveiling RecoverIt: A Novel Persistence and Lateral Movement Tool The landscape of offensive security is continually reshaped by innovative techniques that challenge conventional defenses. [...]
In the evolving landscape of cyber threats, a new, sophisticated adversary has emerged, specifically targeting critical infrastructure and government entities. Dubbed Vortex Werewolf, this cyber [...]
Urgent Security Alert: Critical FortiClientEMS Vulnerability Demands Immediate Attention A critical security vulnerability has emerged within FortiClientEMS, Fortinet’s central management solution for endpoint protection, presenting [...]
Ransomware remains a relentless and financially debilitating threat to organizations worldwide. Its ability to encrypt critical data and demand hefty ransoms has driven cybersecurity professionals [...]
New Telegram Phishing Attack Abuses Authentication Workflows to Obtain Full Authorized User Sessions
The Silent Compromise: New Telegram Phishing Exploits Authentication Workflows The digital landscape is a constant battlefield, and threat actors are perpetually refining their tactics. A [...]
Black Basta’s Evolving Threat: BYOVD Integrated into Ransomware Payloads The relentless cat-and-mouse game between ransomware actors and cybersecurity defenders has taken a concerning turn. Recent [...]