Understanding the Microsoft Teams Image Retrieval Incident In the fast-paced world of enterprise communication, tools like Microsoft Teams are indispensable. They facilitate seamless collaboration, often [...]
DevSecOps Best Practices: Integrate Security in DevOps Security In today’s fast-paced software development landscape, integrating security into every stage of the DevOps process is not [...]
E-commerce Cybersecurity: Securing for Your E-commerce Platform In today’s digital marketplace, e-commerce businesses face a growing number of cyber threats. E-commerce cybersecurity is not just [...]
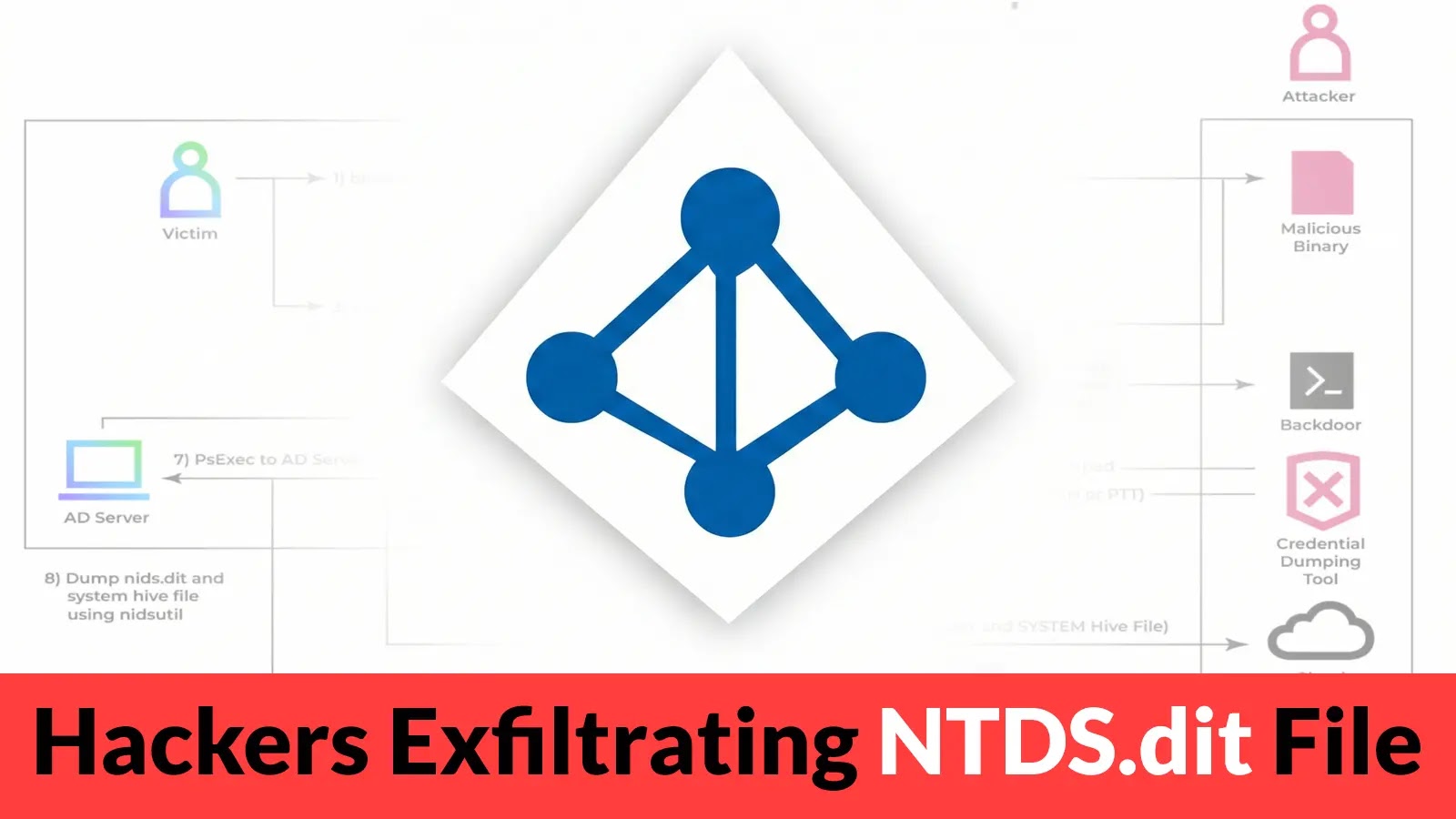
Few assets within an organization’s digital infrastructure are as critical as Active Directory. It’s the cornerstone of identity and access management, the gatekeeper to your [...]
A critical alert has been issued for developers leveraging the Django web framework. Recent disclosures reveal a series of severe vulnerabilities that could expose [...]
A disturbing discovery has recently sent ripples through the Kubernetes ecosystem: a critical security vulnerability in ingress-nginx, a widely adopted Kubernetes ingress controller. This flaw, [...]
Urgent Alert: Large-Scale Reconnaissance Targets Citrix NetScaler Login Panels The digital perimeter of many organizations relies heavily on robust gateways, and Citrix NetScaler (formerly Citrix [...]
Urgent Warning: SolarWinds Web Help Desk RCE Vulnerability Under Active Exploitation A critical remote code execution (RCE) vulnerability in SolarWinds Web Help Desk is [...]
Cybersecurity Metrics What Should you Track Every Team Needs: Key KPIs & Security Metrics In today’s digital landscape, understanding and utilizing cybersecurity metrics is essential [...]
How to Perform a Penetration Test: Process, Types, and Key Cyber Security Tools In today’s complex digital landscape, ensuring robust cyber security is paramount. A [...]