A significant cyber threat has emerged, prompting a critical alert from Salesforce. The notorious threat actor group ShinyHunters has reportedly targeted and successfully exploited misconfigured [...]
In an era where digital interconnectedness fuels global commerce, the integrity of supply chains and third-party vendor relationships has become a paramount concern for [...]
The cybersecurity landscape is a persistent battleground, and even the most robust defenses can sometimes harbor vulnerabilities. A recent discovery concerning Palo Alto Networks’ [...]
Imagine your Android phone, a device you trust with your most sensitive information, compromised in less than a minute. That’s the chilling reality brought [...]
The rapid proliferation of AI assistants has fundamentally reshaped how organizations operate, particularly in managing the deluge of emails, client communications, and critical incident response. [...]
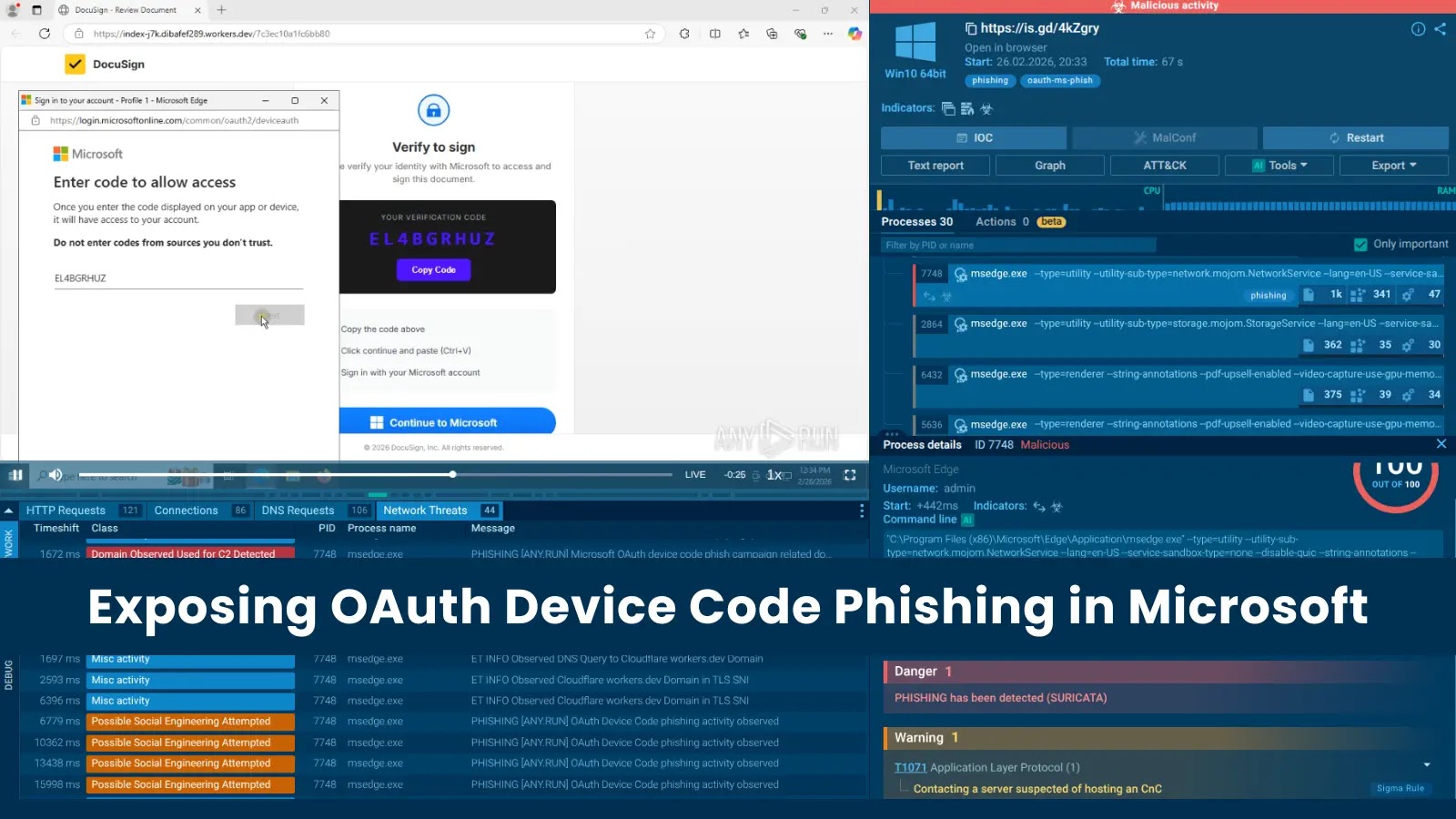
A disturbing trend in cyberattacks is leveraging legitimate Microsoft authentication processes to compromise Microsoft 365 accounts. Unlike traditional phishing, which relies on tricking users into [...]
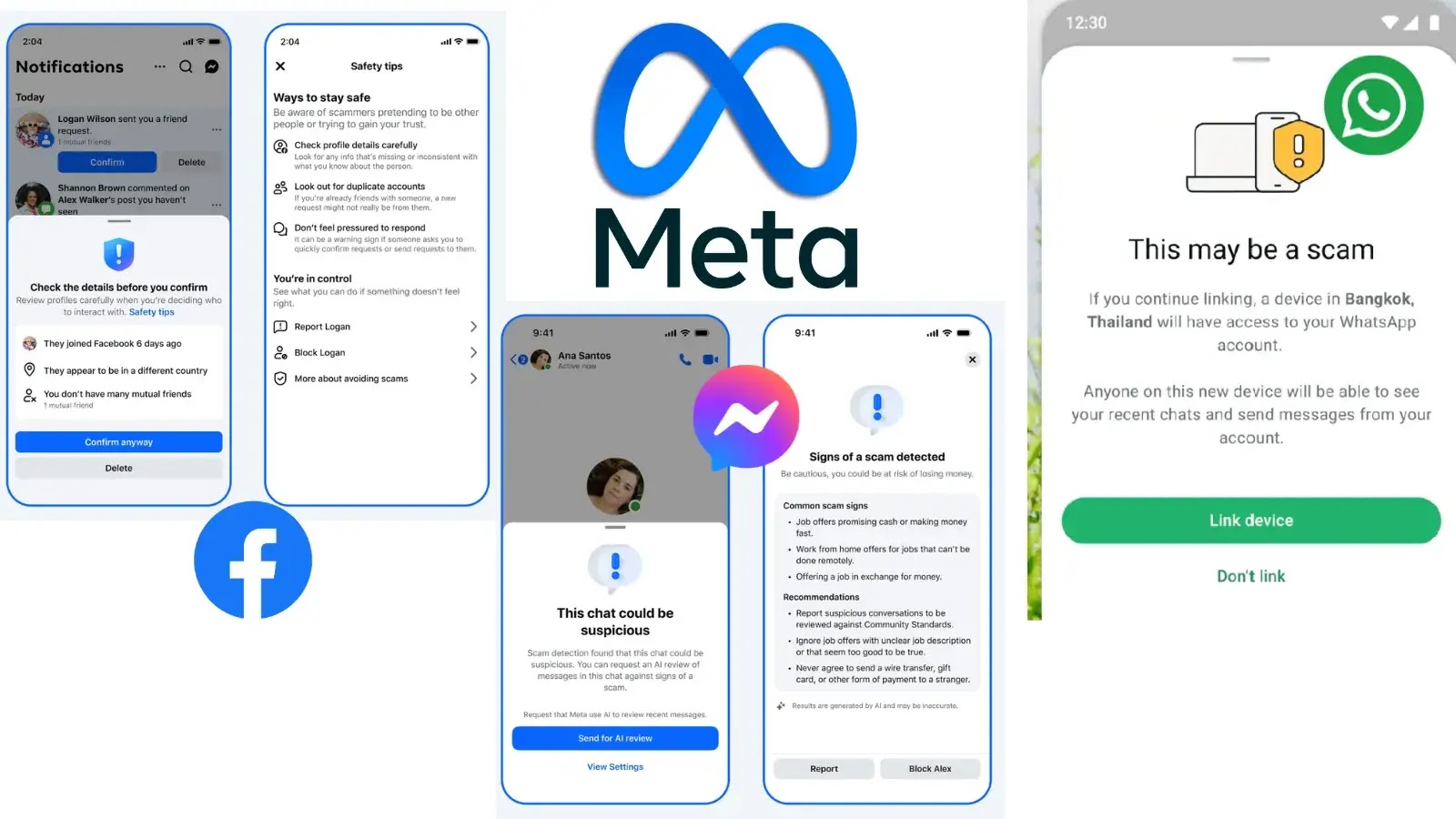
Meta Fortifies Defenses: New Anti-Scam Tools Arrive on WhatsApp, Facebook, and Messenger The digital landscape is a battleground, and the fight against online fraud [...]
A critical vulnerability has surfaced within OpenSSH, specifically impacting its GSSAPI Key Exchange mechanism. This recently discovered flaw, tracked as CVE-2026-3497, enables attackers to [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in Intel Products Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: High Software Affected Intel® Core™ [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Denial of Service Vulnerability in CISCO Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Systems Affected Cisco [...]