Cybersecurity for Supply Chain Management: Mitigating Cyber Risks in Digital Supply Chains In today’s interconnected world, supply chain management has become increasingly complex and reliant [...]
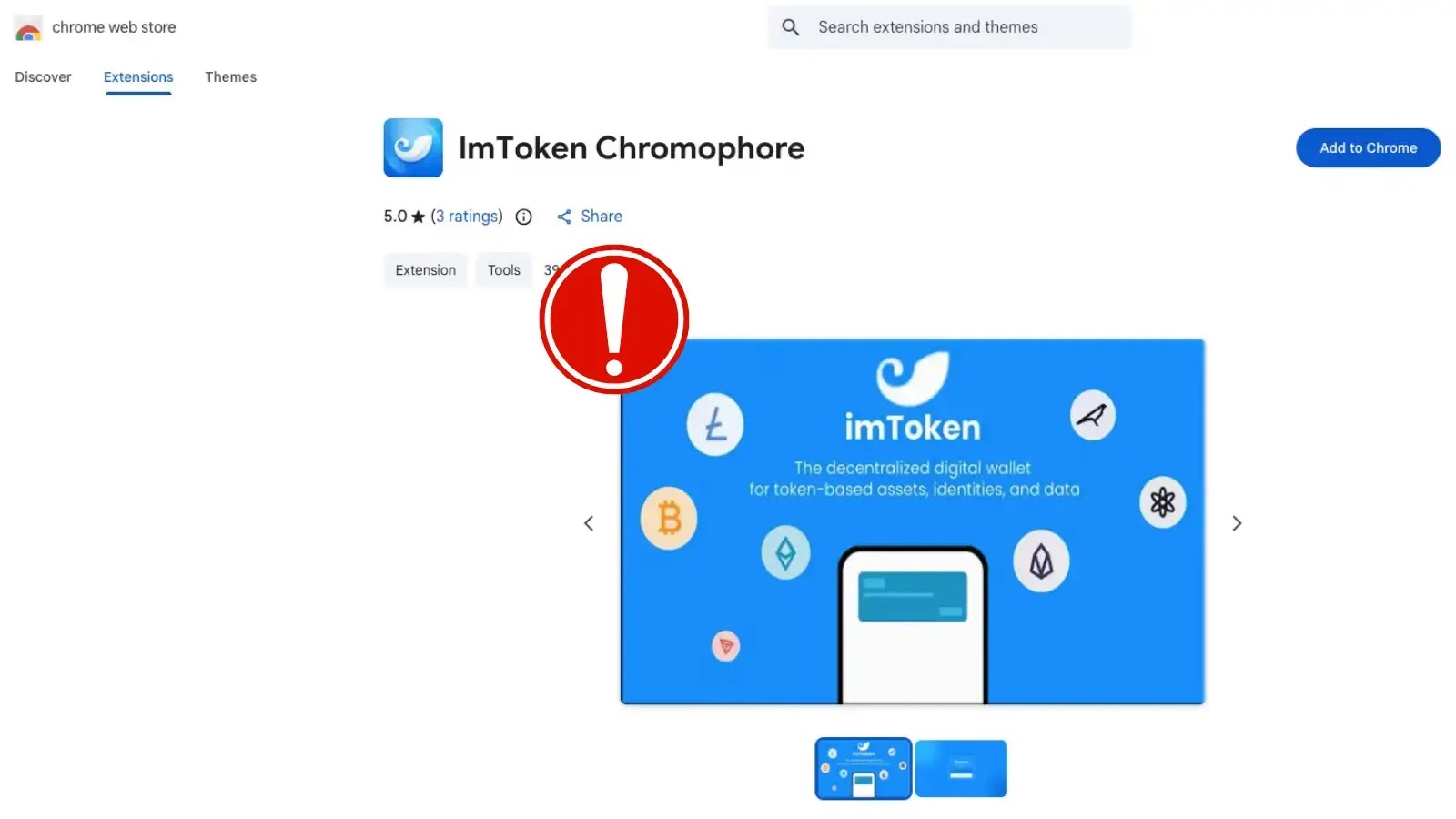
The Silent Threat: Malicious imToken Chrome Extension Steals Crypto Wallets In the decentralized world of cryptocurrency, the security of your digital assets hinges on [...]
The digital health landscape, while offering unparalleled convenience and efficiency, consistently presents a high-stakes target for malicious actors. A recent, sobering reminder of this vulnerability [...]
Unmasking the Critical AVideo Zero-Click Command Injection (CVE-2026-29058) The digital streaming landscape is an invaluable part of modern communication and entertainment, making the security [...]
A disturbing development in the cybersecurity underworld suggests a new, highly potent threat targeting Windows Remote Desktop Services (RDS). Reports indicate that a motivated threat [...]
Unseen Eyes: WiFi Signals, Human Activities, and the π RuView Surveillance Threat The invisible waves that power our daily connectivity are now revealing our [...]
The Dawn of Autonomous Application Security: OpenAI’s Codex Security Unleashed In the relentless battle against software vulnerabilities, security teams often find themselves overwhelmed by a [...]
A disturbing evolution in social engineering attacks has surfaced, directly targeting the powerful capabilities of Windows Terminal. Cybersecurity researchers have uncovered a new wave of [...]
Remote Monitoring and Management (RMM) tools are the unsung heroes of modern IT operations. For countless security professionals and system administrators, these platforms are indispensable, [...]
A cybersecurity incident rocking the Federal Bureau of Investigation (FBI) has sent ripples through national security circles. A sensitive internal network, crucial for managing wiretapping [...]