The Critical Marimo RCE Exploitation: A 10-Hour Race Against Time The cybersecurity landscape just delivered another stark reminder of its relentless pace. Less than [...]
The cybersecurity community is on high alert following the disclosure of a critical security flaw in Axios, a widely used promise-based HTTP client for [...]
In the rapidly evolving landscape of technology, the delicate balance between innovation and user autonomy is consistently tested. A recent public outcry from Mozilla [...]
Organizations worldwide rely on Apache Tomcat for serving Java applications, making its security paramount. A recent emergency security release from the Apache Software Foundation has [...]
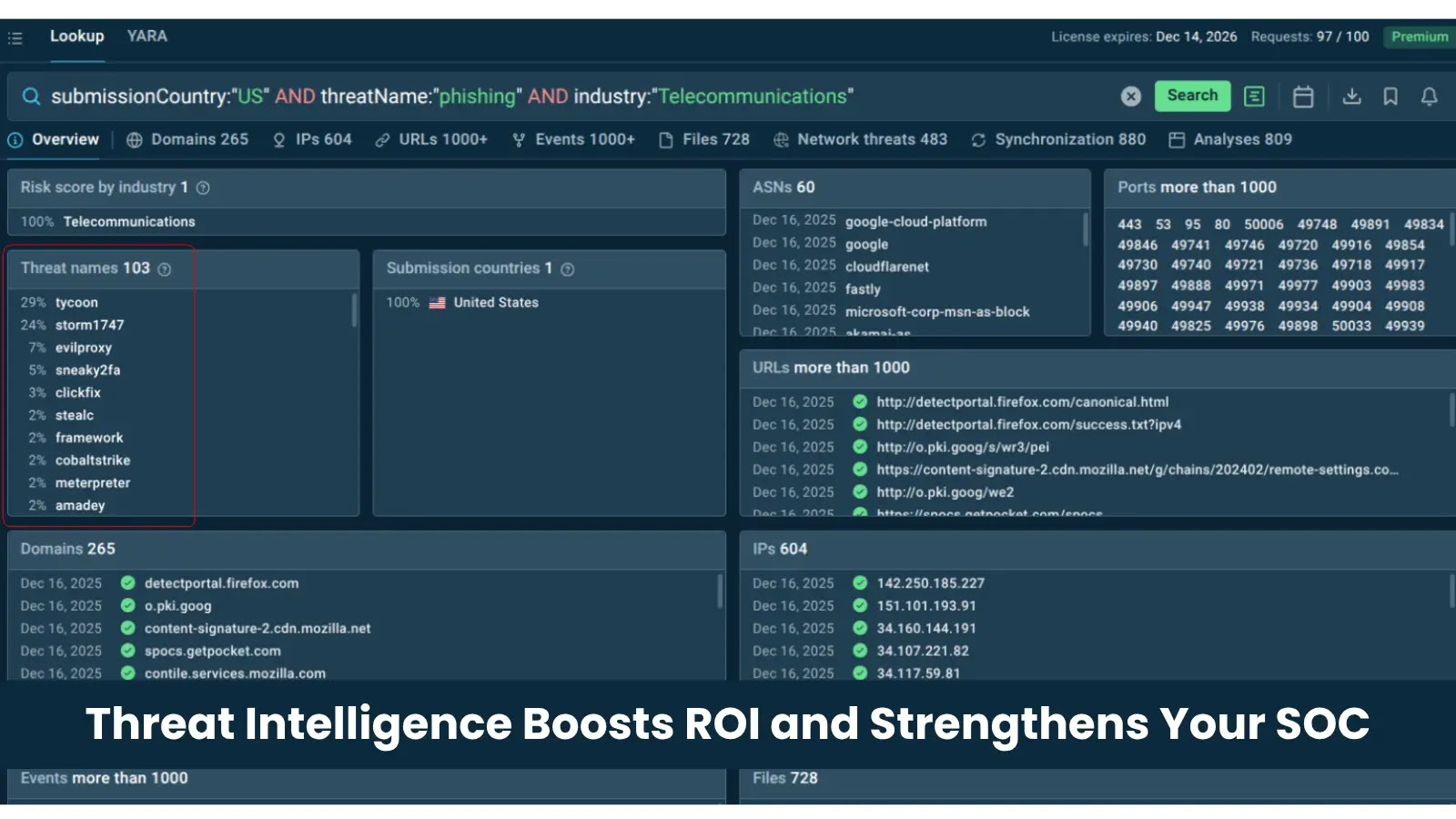
Unlocking ROI: How Threat Intelligence Transforms Your SOC Operations For many cybersecurity leaders, demonstrating the tangible return on investment (ROI) of Security Operations Center [...]
The Rising Tide: Iran-Linked CyberAv3ngers Targets Water Utilities and Industrial Control Systems In an increasingly interconnected world, the security of critical infrastructure remains paramount. Recent [...]
The Deceptive Lure: Phishing Campaigns Abusing GitHub and Jira Notifications In a concerning evolution of social engineering tactics, cybersecurity analysts are observing a new [...]
The digital shadows are deepening, and within them, new threats constantly emerge, evolving with cunning sophistication. One such insidious development is the discovery of VIPERTUNNEL, [...]
The digital landscape is increasingly reliant on artificial intelligence, and when these critical systems falter, the impact can be significant. Recently, users of Anthropic’s [...]
Rockstar Games Suffers Major Data Breach: 78.6 Million Records Exposed via Third-Party Integration In a significant cybersecurity incident that reverberated through the gaming and [...]