How Threat Intelligence Drives a Real ROI Boost for Your SOC
Unlocking ROI: How Threat Intelligence Transforms Your SOC Operations
For many cybersecurity leaders, demonstrating the tangible return on investment (ROI) of Security Operations Center (SOC) activities remains a persistent uphill battle. It’s hard to convince stakeholders, especially those in financial leadership, that funds allocated to risk mitigation directly contribute to the bottom line. The challenge lies in quantifying something that, by its very nature, aims to prevent rather than produce. However, this perspective often overlooks a critical accelerant: high-quality threat intelligence. When strategically integrated, threat intelligence isn’t just an expense; it’s a potent force that saves money, streamlines operations, and delivers measurable, defensible business value. Let’s delve into how a robust threat intelligence program can undeniably boost your SOC’s ROI.
The Undeniable Value Proposition of Threat Intelligence
The core issue CISOs and SOC leaders face is the perception that security investments don’t drive value. They’re often seen as necessary evils or cost centers. Threat intelligence fundamentally shifts this narrative by providing foresight and context, enabling proactive rather than reactive security postures. This proactive stance isn’t just “good practice”; it translates directly into financial benefits.
Tangible Outcomes: Operational Efficiencies and Cost Savings
Threat intelligence doesn’t just promise benefits; it delivers concrete operational improvements and significant cost reductions. These aren’t theoretical gains; they are measurable impacts that directly contribute to a positive ROI.
- Reduced Mean Time To Detect (MTTD) and Mean Time To Respond (MTTR): By providing context on emerging threats, attack vectors, and actor tactics, techniques, and procedures (TTPs), threat intelligence allows SOC analysts to identify and respond to incidents much faster. A quicker response minimizes damage, reduces recovery costs, and lessens business disruption. Knowing what to look for and where to look for it cuts down on alert fatigue and false positives, enabling analysts to prioritize real threats.
- Optimized Resource Allocation: With a clear understanding of the most relevant and impactful threats targeting their organization, SOCs can allocate their limited resources more effectively. This means focusing on hardening critical assets against known threats, rather than spreading resources thin across all possible vulnerabilities. Prioritization based on intelligence avoids wasted effort and ensures that critical security controls are in place where they are needed most.
- Proactive Vulnerability Management: Threat intelligence provides early warnings about newly discovered vulnerabilities that are actively being exploited in the wild. For example, if a severe vulnerability like CVE-2023-45678 is identified as highly exploited by a threat group targeting your industry, your SOC can prioritize patching or applying compensating controls before an attack occurs. This pre-emptive action avoids the colossal costs associated with post-breach remediation, legal fees, and reputational damage.
- Reduced Incident Response Costs: A well-informed SOC can prevent breaches, or at least significantly mitigate their impact. Preventing a single major data breach can save millions in legal fees, regulatory fines, public relations efforts, and lost business. When incidents do occur, having intelligence on the adversary’s TTPs allows for a more efficient and targeted response, reducing the time and resources needed for recovery.
- Enhanced Tool Efficacy: Threat intelligence feeds can be integrated directly into SIEMs, EDRs, and other security tools, enriching alerts and improving detection capabilities. This turns generic logs into actionable insights, maximizing the return on investment of your existing security infrastructure.
Strategic Advantages: Beyond Cost Savings
While cost savings are a significant component of ROI, threat intelligence also delivers strategic advantages that contribute to long-term business resilience and competitive advantage.
- Improved Risk Management: By understanding the threat landscape relevant to the organization, threat intelligence empowers leadership to make more informed risk management decisions. This includes better budgeting for security, more accurate insurance assessments, and strategic planning for business continuity.
- Better Compliance and Governance: Many regulatory frameworks, such as GDPR, HIPAA, and PCI DSS, emphasize proactive security measures and timely incident reporting. Threat intelligence helps organizations meet these requirements by enabling better threat detection and response capabilities, thereby reducing the risk of non-compliance penalties.
- Enhanced Business Reputation and Trust: Preventing breaches and safeguarding customer data protects an organization’s reputation and maintains customer trust. In an era where data breaches are often front-page news, a strong security posture supported by intelligence is a distinct business differentiator.
Remediation Actions: Implementing a Threat Intelligence Program
Translating theoretical benefits into actual ROI requires a strategic approach to implementing and leveraging threat intelligence. Here’s how to get started:
- Identify Key Assets and Threat Landscape: Understand what your critical data and systems are, and which threat actors are most likely to target them. Tailor your intelligence gathering to these specific risks.
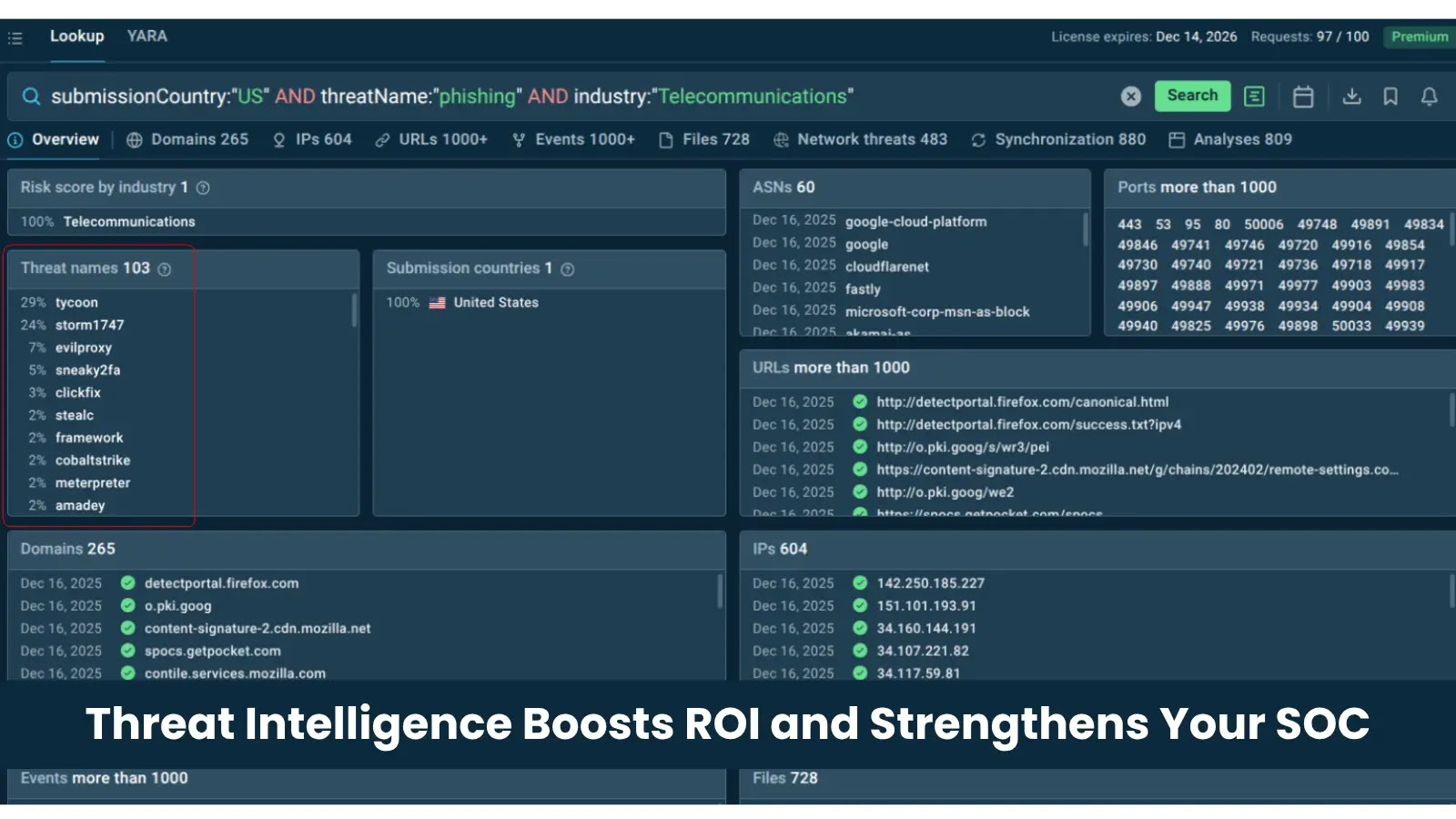
- Integrate Intelligence Feeds: Subscribe to high-quality, relevant threat intelligence feeds (open-source, commercial, and industry-specific). Integrate these feeds into your SIEM, EDR, SOAR platforms, and firewalls for automated detection and blocking.
- Develop Analyst Skills: Train your SOC analysts to understand, interpret, and act on threat intelligence. They need to go beyond simply reading an alert; they need to understand the underlying context and implications.
- Automate Where Possible: Leverage automation to enrich alerts with threat intelligence, automate response playbooks based on identified threats, and reduce manual effort. CVE-2022-12345, for instance, might trigger an automated block if it matches indicators of compromise (IOCs present in your intelligence feed).
- Measure and Report: Continuously track metrics like MTTD, MTTR, number of prevented incidents, and efficiency improvements directly attributable to threat intelligence. Present these findings to leadership in terms they understand – financial savings and risk reduction.
Conclusion: Threat Intelligence as a Strategic Investment
The notion that security is purely a cost center is outdated and detrimental. High-quality threat intelligence transforms a SOC from a reactive incident response team into a proactive, strategic business asset. By enabling faster detection, more efficient resource allocation, proactive vulnerability management, and significant cost savings associated with breach prevention, threat intelligence delivers a powerful and measurable ROI. It’s not just about securing the network; it’s about securing the business’s future, its reputation, and its financial health. Investing in threat intelligence is investing in a resilient and profitable enterprise.





